Search Security
Search SecurityWhat is Zero Trust? Ultimate Guide to the Network Security Model
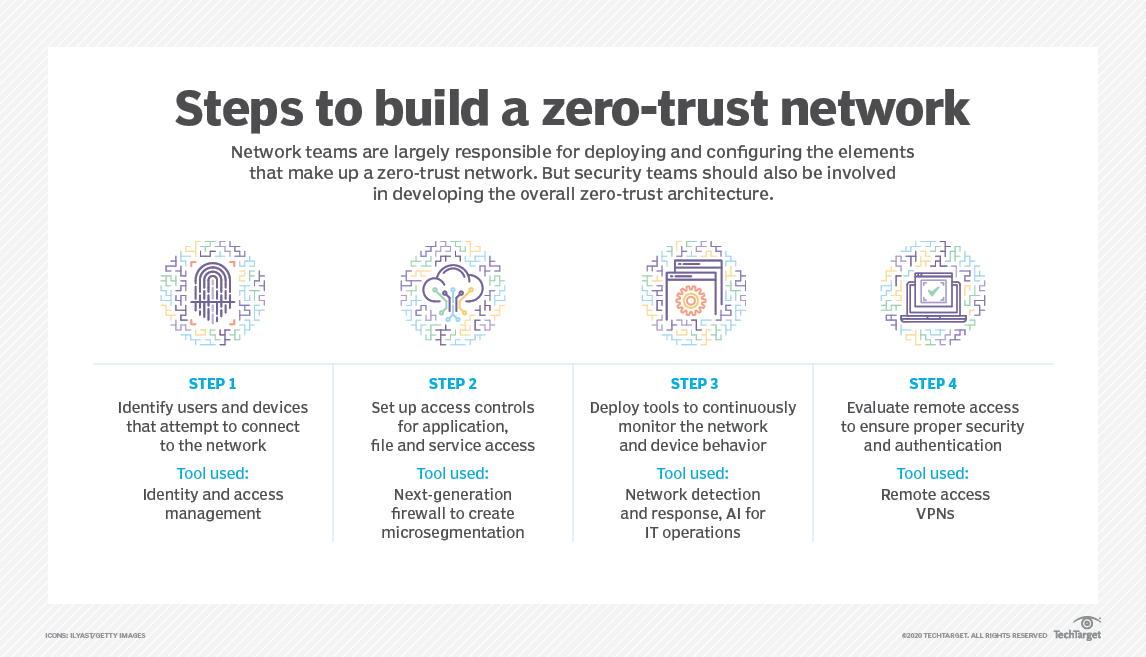
This guide goes in-depth into the origins of zero trust, its architecture, the technology and products that comprise a zero-trust model, as well as how to implement and manage zero trust.
Here's how adopting zero trust enables organizations to do the following:
- Protect company data
- Boost the ability to do compliance auditing
- Lower breach risk and detection time
- Improve visibility into network traffic
- Increase control in a cloud environment.