
Getty Images/iStockphoto
A list of AWS networking services cloud users should know
AWS has cloud networking services for load balancing, traffic routing, content delivery and more. Learn which services and features work best with this overview.
A cloud architecture requires secure and reliable network connectivity. Whether an organization hosts all its workloads in the cloud or keeps some applications and data on premises, the system will only function properly if there's a secure, reliable connection to the cloud network and between resources.
IT teams rely on public cloud networking services to manage and monitor traffic, facilitate communication across environments, protect sensitive data from public exposure, and perform various other functions.
AWS offers a range of services to help cloud consumers establish and maintain network connectivity and security for their applications -- on premises and in the cloud. Explore this list of key AWS networking services to see which features meet your network requirements.
Amazon Virtual Private Cloud
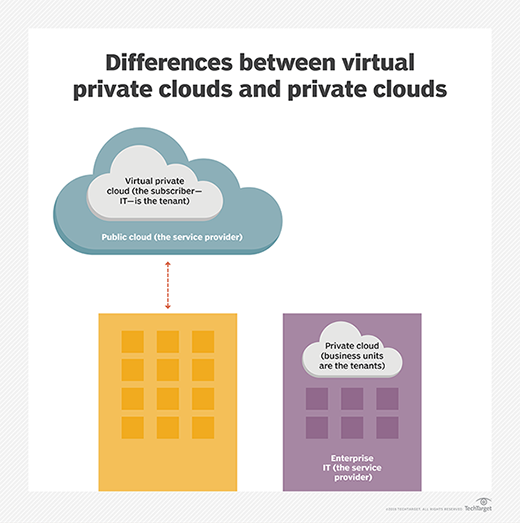
Amazon Virtual Private Cloud (Amazon VPC) creates a virtual network where developers can launch resources into an isolated virtual network. Developers use this service to enable secure communication between different parts of the cloud network, such as Amazon EC2 instances in different subnets.
Network configuration is customizable with Amazon VPC, so developers can control configuration choices such as IP address ranges as well as when to use public and private subnets. Developers and administrators can also create security groups and use network access control lists to filter traffic for a more secure virtual network. The VPC ingress routing feature is another way to boost VPC network security. VPC ingress routing enables you to deploy security appliances to screen inbound and outbound VPC traffic.
Common uses cases for an Amazon VPC are to connect cloud applications to their data centers and connect corporate networks to the cloud.
Elastic Load Balancing
Elastic Load Balancing (ELB) is an Amazon service that automatically distributes incoming application traffic across multiple targets and Availability Zones. It also scales resources to meet traffic demands. ELB distributes traffic to targets, including Amazon EC2 instances, containers, IP addresses and AWS Lambda functions.
This service monitors Amazon EC2 instance health to ensure traffic is routed to properly working instances. Developers can route traffic via a public, internet-facing load balancer or through an internal load balancer for network security purposes.
There are four types of load balancers within ELB that provide automated scaling and high availability:
- Application Load Balancer. Recommended for load balancing HTTP requests and provides routing for application architectures such as microservices and containers. This version of ELB is a OSI Layer 7 load balancer and works at the individual request and application level.
- Network Load Balancer. Best for network/transport protocols load balancing. It is built for load balancing traffic that requires high performance and low latency, including TCP, User Datagram Protocol and Transport Layer Security traffic. Network Load Balancer operates at a Layer 4 connection level.
- Gateway Load Balancer. Better if the user deploys and run third-party virtual appliances, such as firewalls, intrusion detection and prevention systems. It operates at Layer 3, the network layer.
- Classic Load Balancer. Fits applications built within EC2 Classic network. It performs load balancing across Amazon EC2 instances. This is a Layer 4 load balancer that operates at the request and connection level, though it has some Layer 7 functionality. Since is predates the other variants, it should not be used for new services.
Amazon Route 53
Amazon's scalable DNS web service, Route 53, directs end users to web applications by translating domain names into numbered IP addresses. It is used for three main functions: domain registration, DNS routing and health checking
This DNS service can route users to infrastructure inside and outside of the AWS cloud. Route 53 automatically routes users to the optimal DNS server location in the global network, based on network conditions.
Route 53 supports various routing types, such as geo-DNS, weighted round robin and latency-based routing. The Amazon Route 53 has a traffic flow feature that provide a visual editor that helps users create and maintain records in large and complex configurations as well as define policies for how end-user traffic is routed to applications.
Amazon CloudFront
Amazon CloudFront is AWS' native content delivery network (CDN) service. Organizations use CloudFront to quickly distribute both static and dynamic content. The CDN routes each request through the AWS network and to the nearest edge location to provide the fastest delivery path to end users. CloudFront also reduces the number of networks a user's request passes through in the content delivery process.
It is commonly used to accelerate static website content delivery as well as enable video on demand and live streaming video.
AWS Direct Connect
AWS Direct Connect provides a private connection between a customer's on-premises data center and the cloud without using the public internet. This Amazon networking service uses an Ethernet cable to connect an organization's internal workloads to one of AWS' Direct Connect locations. Its offers connection speeds from 50 Mbps to 100 Gbps.
This connection creates multiple virtual interfaces to Amazon's publicly accessible cloud services or to private resources hosted on AWS. Users can access private and public resources with the same connection while maintaining network separation between the two environments. AWS Direct Connect is particularly useful for organizations with strict governance and compliance rules that require private connectivity.
AWS cloud users can choose between two types of connections with this service:
- Dedicated. The dedicated connection uses an Ethernet cable to create a connection with an individual customer. AWS cloud users request a dedicated connection through the AWS Direct Connect console, the command line interface or the API.
- Hosted. The hosted connection requires an AWS Direct Connect Partner to provision the physical Ethernet connection on behalf of a customer. For the hosted connection, IT teams must choose a partner in the AWS Direct Connect Delivery Partners Program.
AWS Virtual Private Network
AWS VPN enables enterprises to connect their on-premises network to cloud users. The platform provides two VPN options: AWS Site-to-Site VPN and AWS Client VPN.
- AWS Site-to-Site VPN. Creates a secure, encrypted connection between an on-premises facility and an Amazon VPC environment as well as AWS Transit Gateway. There is an Accelerated Site-to-Site VPN option, which works AWS Global Accelerator, that improves VPN connection performance.
- AWS Client VPN. Enables employees to securely access a company's resources -- both on AWS and within on-premises networks -- remotely. The Client VPN is a fully managed, elastic VPN service that covers provisioning and capacity as well as scales automatically.
AWS Transit Gateway
AWS Transit Gateway connects Amazon VPCs and on-premises networks across multiple accounts through a central hub. Every new connection is made once as the tool acts as a highly scalable cloud router. It is useful for organizations with hybrid cloud architectures. It supports dynamic and static Layer 3 routing between Amazon VPCs and VPN.
AWS users can centrally monitor their network with the Transit Gateway Network Manager, which provides events and metrics to monitor the entire network -- both cloud and on premises. AWS Transit Gateway Connect enables native integration of SD-WAN appliances into AWS.
This networking service also offers an inter-region peering feature to connect networks and share resources in different AWS regions as well as multicast features.
AWS Global Accelerator
This networking offering improves application availability and performance for globally distributed end users. AWS Global accelerator provides a static public IP address that works as a single fixed entry point and is associated to a regional endpoint. The static IP address accepts incoming traffic onto AWS' global network from the closest edge location. Global Accelerator then directs network traffic to an endpoint on the most efficient path based on geographical location, application health and routing policies set by the developer. In the event of any issues, Global Accelerator automatically redirects traffic to healthy endpoints.
AWS PrivateLink
PrivateLink provides a secure, private connection between Amazon VPCs and other resources that run on AWS or on-premises applications. It establishes a private IP address with an elastic network interface in the subnet and provides a connection that protects data from public internet exposure.
PrivateLink integrates with AWS Direct Connect to provide a secure interface for on-premises applications. By blocking public exposure, PrivateLink helps mitigate certain network security threats such as brute force and distributed denial-of-service attacks.
AWS App Mesh
AWS App Mesh provides application-level networking and enables services to communicate across several types of compute infrastructure. App Mesh uses Envoy, an open source service mesh proxy that runs alongside an enterprise's microservice containers.
By standardizing services communication, AWS App Mesh streamlines operations, configures traffic flows, identifies application issues and enhances network security. Users can monitor, control and debug communications between services. It also determines where errors are occurring and will reroute traffic based off these failures. This takes the pressure off organizations to manually build monitoring and control code every time a failure occurs.
AWS Cloud Map
AWS Cloud Map, a cloud resource discovery service, creates custom names for application resources and automatically updates the resources' locations. The service maintains the updated location of resources that are dynamically changing through endpoints that are statically coded into your application. In turn, this increases application availability. Additionally, development teams will no longer have to store, track and update resource names and location information as AWS Cloud Map provides a single registry for application services.




