
Getty Images
How the FBI took down the Cyclops Blink botnet
The FBI's operation copied and removed Cyclops Blink's malware from victims' systems that were used as command and control devices, severing Sandworm's control of the botnet.
The U.S. Justice Department announced Wednesday that the FBI led a "court-authorized operation" last month to disrupt the Cyclops Blink botnet.
Cyclops Blink is a botnet attributed to Sandworm, a Russian nation-state threat group previously credited with the VPNFilter botnet, as well as the destructive NotPetya attacks in 2017 and the BlackEnergy Trojan used in Ukrainian critical infrastructure attacks in 2016.
The disruptive operation was announced via a U.S. Department of Justice (DOJ) press release and a press conference led by Attorney General Merrick Garland, Deputy Attorney General Lisa Monaco and FBI Director Christopher Wray. The operation was a joint effort between law enforcement and WatchGuard.
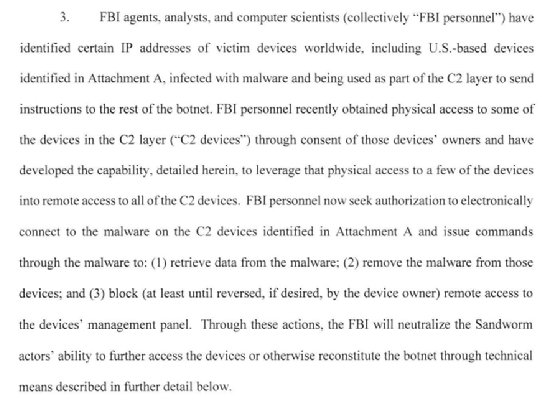
According to partially redacted court documents, the FBI copied and removed malware from vulnerable, internet-facing devices Sandworm was exploiting for command and control (C2) of the Cyclops Blink botnet.
"Although the operation did not involve access to the Sandworm malware on the thousands of underlying victim devices worldwide, referred to as 'bots,' the disabling of the C2 mechanism severed those bots from the Sandworm C2 devices' control," the press release read.
Cyclops Blink was first revealed in February when the U.K. and U.S. governments warned that WatchGuard firewall appliances were under attack; Asus routers were noted as targets soon after. According to the warrant, the FBI had identified "hundreds of victim bots in the United States" prior to the February advisory.
The DOJ explained that while early efforts and guidance from WatchGuard and Asus were effective in remediating thousands of compromised devices, "a majority of the originally compromised devices remained infected." The FBI found "a drop of only approximately 39% in the number of previously identified infected bots worldwide as of March 18, 2022," according to the warrant.
Following the court's authorization of a new disruptive operation on March 18, the FBI "was successful in copying and removing the malware from all remaining identified C2 devices." Specifically, investigators found C2 devices at 26 IP addresses, with 13 of the addresses being inside the U.S.
The FBI then issued a series of commands to those C2 devices that confirmed the presence of the malware executable on the device; remotely logged the serial number of the infected device; retrieved files containing the lists of the C2 IP addresses stored; removed the malware from the device and changed its firewall rules to prevent Sandworm threat actors from reestablishing control.
The FBI noted in the warrant that issuing the commands "does not allow the FBI to search, view, or retrieve a victim device owner's content or data."
While the operation had "immediate effect" in disrupting Sandworm's control over thousands of bot devices, the DOJ said these devices could remain vulnerable to Sandworm unless owners take steps to remediate the infections.
During the press conference, Wray described the move as an "aggressive effort" to pursue Russian cyber threats.
"The Russian government has shown that it has no qualms about conducting this kind of criminal activity, and they continue to pose an imminent threat," he said. "This global botnet disruption, in conjunction with the other actions discussed today, reflects an aggressive effort by the FBI and our partners to go on offense against Russian cyber threats wherever they appear."
Last April, the FBI announced it had removed thousands of web shells from Microsoft Exchange servers vulnerable to ProxyLogon. Notably, they did so without first informing or asking consent from server owners.
The warrant for the Cyclops Blink operation explained that the FBI gained physical access to "some" of the C2 devices through consent of the device owners and, at the time, planned to use said access to remotely access all other C2 devices. It is unknown based on the warrant how many C2 devices the FBI had identified.
The FBI has not responded to TechTarget's request for comment at press time.
Alexander Culafi is a writer, journalist and podcaster based in Boston.






