As Black Hat 2019 quickly approaches, I couldn’t help but think back to the tail-end of my previous life attending industry conferences as an analyst covering network security. By 2014, you couldn’t get a conversation with a user on the show floor if you were a firewall vendor that didn’t offer robust application control. Palo Alto Networks had successfully shifted the industry focus to application layer inspection and next-generation firewalls had all but been accepted as the default standard for network protection. This transition addressed the fundamental shift in internet usage affecting the way we live and work. Traditional Layer 3 and 4 scanning could not provide the visibility and control over Layer 7 traffic required to protect the modern enterprise. Of course, at the time it was the need for control over applications like Facebook, Twitter, and YouTube driving the change. But it clearly foreshadowed the upcoming transition to cloud application usage.
Fast-forward to 2019: worrying about control over the applications I mentioned above seems somewhat trite by comparison. Today you’d be hard-pressed to find an enterprise without:
- Business-critical data and applications residing in multiple cloud environments.
- Users leveraging unapproved cloud applications without IT knowledge.
- Remote and branch office workers trying to directly access the internet in order to utilize both approved and shadow IT resources.
In short, it’s difficult to point to an organization without an incredibly dynamic and complex environment.
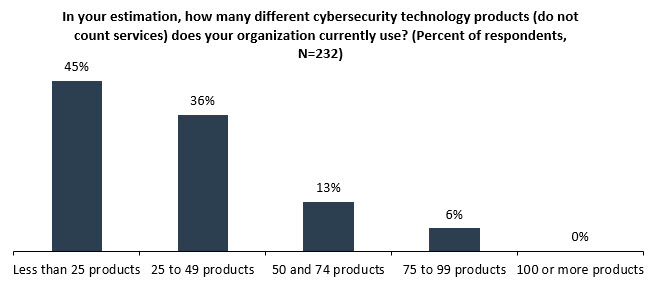
All the while, security teams do their best to make sure that users have the correct access to the resources they need to do their jobs, while still maintaining a strong security posture. Over time this has created a sprawl of point products designed to deal with specific aspects of all the use cases above. As a point of reference, ESG research has found that 55% of organizations with at least 500 employees have more than 25 different cybersecurity products.
Just a quick list of network security technologies starts to paint a daunting picture:
- Secure web gateways to enable safe and monitored user access to the web.
- Cloud access security brokers to discover unsanctioned apps and provide governance over sanctioned cloud resources.
- Data loss prevention to secure corporate data.
- DNS protection for content filtering and malware protection.
- Next-generation firewalls to enforce policy and inspect content at the perimeter.
- Software-defined perimeter and “zero-trust” technologies to safely broker user access to applications.
Because of this complexity, one of the key themes I’ll be researching and writing about in the coming months will be the requirement for further integration across point tools. As part of that work, ESG will be building out its coverage of an emerging market we’ve identified as elastic cloud gateways, or ECGs. At a high-level, ECGs provide network security for the cloud era by integrating a lot of the functionality described above into a cloud-delivered gateway built on a cloud-native microservices platform. These are multi-mode solutions that provide elasticity around both services and consumption to better align security with how organizations are leveraging cloud resources overall. When deployed effectively, ECGs will help organizations converge tools to drive consistent policy, create operational efficiencies, and ultimately, help reduce the attack surface.
Specific to Black Hat, consolidation and the continued blurring of network and cloud security will be the major themes I’ll look for next week. Additionally, I expect to hear a lot about software-defined perimeter (SDP) as more and more real-world use cases come into play. And finally, I think the growth of network traffic analytics (NTA) as part of a robust threat detection and response solution set will be a common refrain as well. I’m expecting it to be an insightful week!