
fotohansel - Fotolia
Why microservices and IoT apps are perfect together
The development of IoT apps certainly presents its fair share of challenges, but the benefits that microservices bring might be an antidote to those struggles.
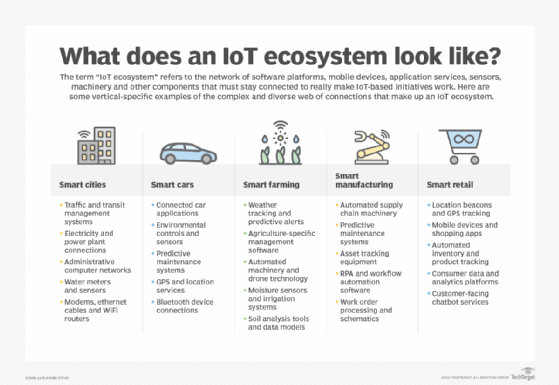
Over the past decade, the internet of things has grown exponentially. The hyperconnectivity paradigm has already found a home in many real-world scenarios, such as city planning, transportation, health, automobiles and agriculture. For many businesses, it is no longer an aspirational technology goal, but an operational necessity.
However, the sheer scale and complexity of the connected systems associated with IoT make it difficult to develop, integrate and scale applications in a way that is manageable or secure. This is where the design principles and advantages associated with microservices architectures can step in to bolster an organization's IoT initiative. By capitalizing on the benefits of things like containerization, modularity, independent deployment and loose coupling, software teams can navigate IoT app development with much more confidence.
While it won't solve all the problems associated with IoT, let's review the major ways that combining microservices and IoT can provide much-needed support.
4 ways microservices and IoT can work together
Businesses that decide to invest in IoT will immediately have a slew of issues to face. Software teams will need to connect a whole new collection of endpoint devices, application servers, databases and AI-based analytics tools. Often, this also involves integrating these technologies with legacy software and development processes.
Here are some of the core considerations business must keep in mind when they commit themselves to adopting this type of application technology, and where the combination of microservices and IoT comes into play:
- Connectivity. IoT depends on a complex network of devices linked to cloud-based applications, databases, software platforms and communication points. To that end, containerized microservices are lightweight, scalable and deployable on premises or in the cloud, providing the modularity needed for ubiquitous communication.
- Security. Organizations need to manage and mitigate the risk factors associated with the physical device breaches and sensitive data exchanges associated with IoT. Due to the loose coupling found in a microservices architecture, services become less attractive doorways into larger systems and can be patched with security updates quickly.
- Flexibility. The ability to quickly adapt application functionality and provide ever-growing support for evolving technologies is a must, especially given the rate that IoT has evolved over the past few years. The adaptive nature of a microservices architecture enables you to quickly introduce new services or replace old services without disrupting the application.
- Data integrity. IoT absolutely relies on an organization's ability to design a sensible and reliable plan when it comes to collecting and processing critical data, especially when that data lives in legacy systems. While specific microservices that need significant computing can be moved to the public cloud, those that need faster response times or more security can readily deploy services locally.
The components of microservices-based IoT
A microservices-based IoT system will connect to multiple, varied edge locations, such as home computers, office networks, GPS devices, robotic manufacturing lines and more. One of the biggest benefits of a microservices architecture is its ability to readily integrate with distributed application service types, device platforms, programming languages, coding frameworks and functional libraries.
Here are some of the common components you'll find in a microservices-based IoT software system:
- The physical endpoints that will need to connect with software systems, such as sensors, automated machinery and mobile devices.
- An API gateway that acts as a single entry point and broker for all external client/server requests, service messages and API calls.
- A cloud-based infrastructure that houses compute, storage and analytics in the cloud -- you can scale up or scale down your resources as needed.
- Customized security tokens that handle authentication, authorization and other processes related to properly allowing access to services.
- Various messaging protocols that facilitate the communication and data exchanges that occur between different software systems, such as HTTP, XML, JSON and gRPC.
- Robust application monitoring tools responsible for identifying failures and capable of refreshing problematic services.








