Amazon GuardDuty
Amazon GuardDuty is a managed cloud security monitoring service that detects behavior or threats that can compromise Amazon Web Services (AWS) accounts, resources or workloads.
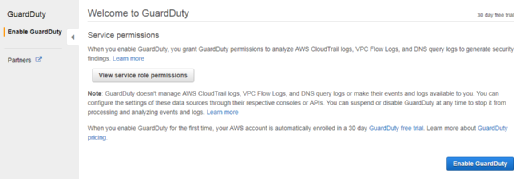
As a managed cloud-hosted service, Amazon GuardDuty does not require an IT team to deploy, manage and scale additional security software. Instead, an administrator or security analyst enables GuardDuty via the AWS Management Console, and the service immediately begins to analyze his or her cloud environment. However, some of the more advanced threat detection capabilities require one to two weeks to establish normal baselines for comparison.
How GuardDuty works
Amazon GuardDuty continuously analyzes cloud events in AWS CloudTrail, Amazon Virtual Private Cloud (VPC) Flow Logs and domain name system (DNS) logs for possible malicious activity.
The service uses built-in threat intelligence, anomaly detection and machine learning capabilities developed by the AWS security team to perform analysis in near real time.
GuardDuty detects three primary types of threats on the AWS cloud:
- Attacker reconnaissance: These types of threats include failed login patterns, unusual API activity and port scanning;
- Compromised resources: This category of threats includes cryptojacking, unusual spikes in network traffic and temporary access to Elastic Compute Cloud (EC2) instances by an external IP address; and
- Compromised accounts: Examples of these threats include API calls from an odd location, attempts to disable CloudTrail and unusual instance or infrastructure deployments.
While an admin can supply GuardDuty with his or her own list of "safe" IP addresses, the service does not otherwise support customized detection rules. An admin can, however, respond to each GuardDuty finding with thumbs-up or thumbs-down responses to provide feedback for future detections.
Amazon GuardDuty compiles and delivers security findings to the Management Console in a JSON format, which enables an admin or automated workflow to take action. For example, Amazon CloudWatch Events can accept findings from GuardDuty, then trigger an AWS Lambda function to modify security configurations. The GuardDuty console and APIs retain security findings for 90 days.
GuardDuty management, costs
Amazon GuardDuty works independently from cloud resources, which means it has no performance impact on running systems. Additionally, GuardDuty uses service-linked roles through AWS Identity and Access Management, which means an admin doesn't have to manage or modify S3 bucket policies or log collection, as they would with permissions for individuals.
An AWS customer pays for GuardDuty based on the quantity of AWS CloudTrail Events and volume of VPC Flow Logs and DNS logs the service analyzes. AWS provides a free trial.
Amazon Macie, another machine learning-enabled security service, differs from GuardDuty in that it focuses on data classification and protection.