Askhat - stock.adobe.com
4 best practices for big data security in cloud computing
When dealing with vast amounts of data in the cloud, enterprises need to be proactive with security. Don't wait for a threat to happen; apply these best practices first.
Any big data project will involve a significant amount of data which can include sensitive or personally identifiable content. Tackling big data security in cloud computing requires various best practices.
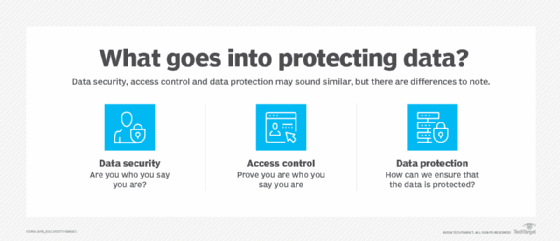
Every business that stores data must be concerned with issues that can impact the following:
- Data security. Is the data set protected against snooping or theft? What happens to the business if any data leaks to unauthorized concerns?
- Data integrity. Is the data set protected against alteration or deletion? What happens to the business if any data is changed, causing an unexpected or inaccurate result of a big data analysis?
- Data processing. Is the data set protected within the computing infrastructure? Can any part of the computing infrastructure be hacked to potentially expose data or results?
All these considerations can affect the organization's security, business governance and regulatory compliance postures. Public cloud security is a shared responsibility, which requires that cloud users take measures to ensure any big data deployment is properly secured, configured and deployed.
Secure big data in the cloud
There are several common best practices for big data security in cloud computing. Follow these tips to help secure data sets and big data infrastructures.
1. Pay attention to the architecture
Design the big data compute and services infrastructure with care. Understand how data and network traffic flow in the infrastructure and limit the number of places that hackers might attack. Document the infrastructure and enforce its configuration through established public cloud tools, such as AWS Config and Azure App Configuration.
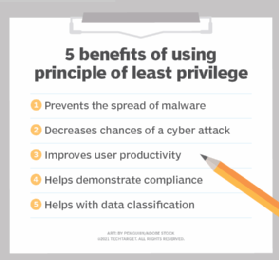
2. Implement least privilege tactics
Employ full authentication and authorization for all data and compute access -- never use applications, tools or services that lack authentication or authorization capabilities. Always use least privilege tactics to restrict access to data and resources. IT teams can apply these to the group level or the individual level as needed.
3. Encrypt data
Encrypt data both at rest and in flight. Even if an unauthorized individual manages to access a data set, the encrypted data would be unusable. Encrypting data in flight and using common techniques such as Transport Layer Security or Secure Sockets Layer prevents data snooping or alteration. IT teams can encrypt data at rest before storage, within the database, at the disks or even a combination of tactics that meet business requirements.
4. Monitor the environment
Craft a cloud monitoring strategy to keep track of the storage and compute environment. Native cloud monitoring tools, like Amazon CloudWatch, Azure Monitor and Google Cloud Operations suite, can collect monitoring and operational data to build logs and oversee metrics and events. Use dashboards and audit logs to spot malicious activity within the cloud deployment. Additionally, with cyber security threats on the rise as more enterprises move to the cloud, take advantage of other provider tools, such as intrusion detection and prevention systems, to spot hackers at work.