
James Thew - Fotolia
A breakdown of core AWS identity services
Given the wide range of organizations that use AWS to power their applications, it's important to understand the options AWS offers to manage access to application components.
Identity and access management are critical components to keep applications secure, and AWS offers a range of tools and services. With these services, IT teams can avoid the otherwise time-consuming nature of implementing an effective and secure way to control access to various components.
Choosing the right AWS identity service depends on various factors that are specific to applications and the teams behind them. These factors include development frameworks, migration requirements, organizational size and structure, interactions with external services or user repositories and cross-account dependencies.
Let's explore the different AWS identity, access and authentication services available and how to select the right options for your organization.
Identity and authentication management
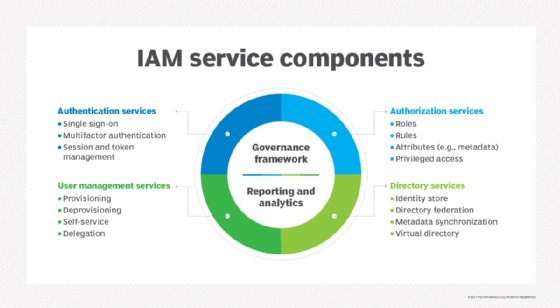
AWS Identity and Access Management (IAM) is the foundational authentication service in AWS. IAM provides detailed access to AWS resources through IAM users, groups, roles and polices, which enable application owners to grant access to specific AWS API operations and resources. IAM controls how users gain access to AWS resources through the supported software development kits (SDKs), AWS Management Console and command line interface (CLI).
However, there are additional identity and authentication services available that target more specific areas.
Amazon Cognito
Amazon Cognito is a popular AWS authentication service that is primarily geared toward application-level access, but also supports the low-level AWS resource access that IAM delivers. Cognito features managed user repositories -- known as user pools -- where application owners store and configure the users that will have access to applications. Developers can configure rules for usernames and passwords as well as integrations with third-party identity providers, such as Facebook and Google.
Developers can integrate Cognito user pools and identity pools to manage AWS permissions for access to resources inside an application. Application owners can easily import users into a user pool, which is a suitable feature for migrations into AWS. Cognito integrates well with the AWS Amplify framework, which provides a number of libraries to simplify how application code interacts with Cognito.
AWS Directory Service
AWS Directory Service is a managed Microsoft Active Directory hosted in AWS. The service supports authentication for different components, such as Amazon EC2 and Amazon Relational Database Service instances, typically within the context of Microsoft Windows environments. This service integrates well with on-premises user credentials repositories to grant access to AWS-based resources or even the AWS Management Console. It can also grant AWS-hosted applications access to on-premises systems. This makes it a suitable option for authentication across hybrid cloud, on-premises or multi-cloud environments.
Access management
For most applications, it's a best practice to create multiple AWS accounts to have a healthy separation between development or pre-production environments and production or customer-facing ones. When it comes to large companies with multiple departments and teams, it's critical to have multiple AWS accounts in order to control budgets and applications that are relevant only to specific teams.
However, with so many accounts, IT teams need to control access. Fortunately, AWS offers various access management tools.
AWS Resource Access Manager
For organizations that need to share common AWS resources across multiple accounts, it can be a challenge to handle permissions and access for these common resources. AWS Resource Access Manager (RAM) helps manage these scenarios. For example, AWS RAM enables IT professionals to launch an EC2 instance in a centrally managed subnet in a different account.
Through integration with AWS Organizations, AWS RAM makes components available across multiple AWS accounts. Account managers choose the resources to share and which accounts to share them with. On the other end, once a resource is shared, application components can be accessed via the usual methods, such as the AWS Management Console, APIs, SDKs or the CLI.
Keep in mind that not all AWS resource types are eligible to be shared using AWS RAM. Currently, there is only a relatively small subset of services and components that can be shared using AWS RAM.
AWS Organizations
AWS Organizations is a central management service for multiple AWS accounts. With this AWS identity service, application owners can manage users and access to AWS resources within an organization. Managers can create and apply policies across multiple accounts and also limit the services that are available to specific accounts within the organization. A master account manages the permissions and child accounts cannot override these permissions, which limits the impact of potential security breaches.
AWS Organizations enables grouping of multiple AWS accounts, where each account has separate application environments and functions within an organization. For example, there can be accounts dedicated to specific areas, such as backups, logging and user management, in addition to application deployment stages.
AWS Single Sign-On
AWS Single Sign-On (SSO) enables access to applications hosted in AWS or external applications, such as Salesforce and Office 365. AWS SSO can also connect to Microsoft Active Directory, including on premises, Okta Universal Directory and Azure Active Directory. This AWS identity service interacts with AWS Organizations to configure which AWS accounts users have access to and their respective permissions.
While AWS Organizations takes care of the overall permissions management within multiple accounts, SSO handles user management by assigning each user permissions managed in AWS Organizations. Account managers configure which users have access to which AWS accounts and their respective permissions in a centralized management portal. This means users don't need to have a separate login for each AWS account they have access to and can potentially use their existing corporate credentials.
AWS Control Tower
AWS Control Tower integrates with AWS Organizations, but the focus of this services is to provision and manage multiple AWS accounts. It delivers tools to centrally monitor and manage the activity that takes place in a multi-account AWS environment. Control tower enables organizations to create separate AWS accounts to store live audit logs or archives.
This AWS identity service also enables IT teams to centrally create new accounts. Control Tower assigns an AWS account as the Management account -- which will have visibility over multiple AWS accounts. While Control Tower delivers centralized visibility and ability to create new accounts, AWS Organizations manages permissions within those multiple accounts.





