What is HIPAA (Health Insurance Portability and Accountability Act)?
HIPAA (Health Insurance Portability and Accountability Act) is United States legislation that provides national standards to prevent protected health information (PHI) from being disclosed without the patient's consent or knowledge. The law has become even more consequential in recent years due to the sharp rise in cyberattacks, data breaches and ransomware incidents targeting healthcare providers and insurers.
Signed into law by President Bill Clinton on Aug. 21, 1996, HIPAA overrides state laws regarding the protection of medical information unless a state law is deemed more stringent. The legislation has had wide-reaching impacts on the healthcare industry, from electronic billing to secure patient data exchange.
What is the purpose of HIPAA?
The main purpose of HIPAA has evolved over time. Also known as Public Law 104-191, HIPAA was originally conceived with two overarching objectives:
- To help people maintain uninterrupted health insurance coverage when they lose or change jobs. This included preventing health insurance companies from denying coverage based on preexisting conditions and requiring them to provide continuous coverage.
- To combat healthcare fraud, abuse and waste in health insurance and healthcare delivery. This component of HIPAA sought to balance the increased cost burden on insurers now required to provide continuous coverage.
Today, the purpose of HIPAA is grounded much more in the privacy protections laid out in the HIPAA Privacy Rule, which first went into effect in 2003.
HIPAA has several other goals as well:
- Standardizing the electronic transmission of administrative and financial data.
- Improving access to long-term care services and health insurance.
- Providing guidelines for pretax medical spending.
- Enhancing the efficiency of the healthcare system through digital standardization.
What are the 5 main components of HIPAA?
HIPAA contains five components, known as titles in the law's parlance:
Title I: HIPAA Health Insurance Reform
Protects health insurance coverage for individuals who lose or change jobs. It also prohibits group health plans from denying coverage due to preexisting conditions or from setting lifetime coverage limits.
Title II: HIPAA Administrative Simplification
Directs the U.S. Department of Health and Human Services (HHS) to establish national standards for processing electronic healthcare transactions and mandates data privacy and security rules for handling PHI.
Title III: HIPAA Tax-Related Health Provisions
Includes tax-related provisions for medical care and provides guidance on pretax medical savings accounts.
Title IV: Application and Enforcement of Group Health Plan Requirements
Clarifies insurance reform measures, especially around coverage continuity and preexisting conditions.
Title V: Revenue Offsets
Includes provisions on company-owned life insurance and guidelines concerning individuals who lose U.S. citizenship for tax purposes.
Among these, Title II is most often associated with HIPAA compliance and includes several critical requirements:
- National Provider Identifier (NPI) Standard. NPI requires all healthcare providers and organizations to use a unique 10-digit identification number.
- Transactions and Code Sets Standard. Mandates uniformity in electronic data interchange (EDI) to streamline insurance claims.
- HIPAA Privacy Rule. Establishes guidelines for the use and disclosure of individuals' health information.
- HIPAA Security Rule. Specifies standards for securing electronic PHI (ePHI).
- HIPAA Enforcement Rule. Outlines procedures for investigating HIPAA violations and imposing penalties.
The Office for Civil Rights (OCR) at HHS enforces these rules, conducts audits and investigations, and imposes penalties for noncompliance.
HIPAA Privacy Rule
The HIPAA Privacy Rule, officially called the Standards for Privacy of Individually Identifiable Health Information, sets national standards to protect individuals' medical records and other personal health information.
Issued by HHS, the Privacy Rule limits who can access and share PHI and requires healthcare providers to give patients an accounting of PHI disclosures. It also guarantees individuals the right to the following:
- Access their medical records upon request.
- Request corrections to their records.
- Receive a list of disclosures of their PHI.
The Privacy Rule applies to HIPAA-covered entities, which include healthcare providers, health plans and healthcare clearinghouses, as well as business associates (BAs) that handle PHI on their behalf.
What are HIPAA-covered entities?
HIPAA only applies to covered entities and their business associates. Covered entities are those that directly handle PHI, and they fall into three categories:
- Healthcare providers. Includes doctors, clinics, dentists, psychologists, pharmacies, nursing homes and chiropractors.
- Health plans. Includes private health insurance companies and public programs such as Medicare, Medicaid and military/veterans' health programs.
- Healthcare clearinghouses. Organizations that standardize health data transactions, such as billing services and community health information systems.
To determine if an organization is a covered entity or BA, HHS offers an online decision tool.
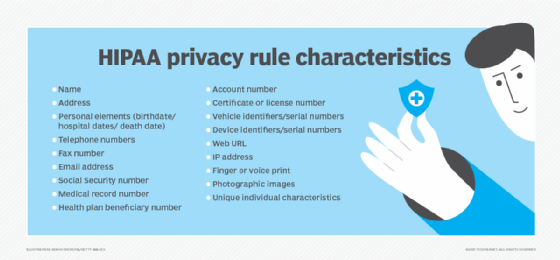
What information is protected under HIPAA?
The HIPAA Privacy Rule protects all individually identifiable health information held or transmitted by a covered entity or BA. This information can exist in various formats:
- Paper records.
- Digital files.
- Verbal communications.
The law specifies 18 identifiers, including the following:
- Names, addresses, birth dates and Social Security numbers.
- Health status (past, present or future).
- Treatment and diagnostic information.
- Payment information related to healthcare.
PHI does not include the following:
- Employment or educational records not directly tied to healthcare.
- Deidentified health data with no reasonable way to identify the individual.
An example of PHI is a hospital discharge summary with a patient's name. An example of non-PHI could be heart rate data from a smartwatch not linked to a healthcare provider.
HIPAA administrative requirements
Covered entities must meet several administrative requirements under the Privacy Rule:
- Appoint a privacy official responsible for HIPAA policies and compliance.
- Train all staff (including employees, volunteers and contractors) on privacy procedures.
- Implement administrative, technical and physical safeguards for PHI.
- Provide a process for individuals to submit privacy complaints.
- Mitigate any harmful effects from privacy violations.
HIPAA-permitted uses and disclosures
PHI can be used or disclosed under two conditions:
- The use or disclosure is explicitly allowed or required by the HIPAA Privacy Rule.
- The individual has provided written authorization.
Some permitted disclosures include the following circumstances:
- Treatment, payment and healthcare operations.
- Public health activities (e.g., reporting disease outbreaks).
- Judicial and law enforcement proceedings.
- National security or intelligence activities.
In emergencies (such as the COVID-19 pandemic), temporary HIPAA rule modifications might allow broader data sharing.
HIPAA Privacy Rule penalties
Penalties for violating HIPAA depend on the severity of the infraction:
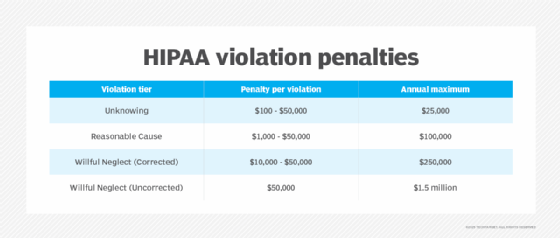
Criminal penalties:
- Up to one year in prison and $50,000 for knowingly obtaining or disclosing PHI.
- Up to five years if done under false pretenses.
- Up to 10 years and $250,000 if done for personal gain or malicious harm.
Organizations can reduce risk through comprehensive HIPAA compliance training. Although HHS does not offer official certifications, third-party vendors and in-house programs can help demonstrate compliance readiness.
HIPAA Security Rule
The HIPAA Security Rule, or the Security Standards for the Protection of Electronic Protected Health Information, establishes safeguards for securing ePHI. Based on guidance from NIST, the rule has two main objectives:
- Protect ePHI from breaches, unauthorized access and tampering.
- Promote secure systems for storing and transmitting data.
Key implementation steps include the following actions:
- Conducting risk assessments.
- Implementing encryption and backup procedures.
- Setting up access controls and audit logs.
- Restricting physical access to workstations and data storage devices.
The rule applies to all covered entities and BAs managing electronic data and is enforced by the OCR. It is closely aligned with federal Meaningful Use and Promoting Interoperability programs.
Where does HIPAA apply in telehealth and digital health?
The expansion of telehealth and digital health technologies has introduced new complexities in maintaining HIPAA compliance. Covered entities and business associates must ensure that all tools used for virtual care delivery -- including video conferencing platforms, mobile apps and patient portals -- meet HIPAA standards.
These are some of the key considerations for HIPAA compliance in digital health:
- End-to-end encryption. All communications must be encrypted to prevent unauthorized access to ePHI.
- Business Associate Agreements (BAAs). Providers must have BAAs in place with technology vendors that store or transmit PHI.
- Secure patient authentication. Systems should require multifactor authentication to verify identity.
- Audit trails. Platforms must provide access logs and audit features to monitor data access and modification.
During public health emergencies such as the COVID-19 pandemic, HHS provided temporary enforcement discretion -- allowing use of certain non-HIPAA-compliant platforms (e.g., FaceTime, Zoom) without penalties, provided providers acted in good faith. However, these flexibilities were tied to emergency declarations and are not permanent.
HIPAA Omnibus Rule
Finalized in 2013, the HIPAA Omnibus Rule updated HIPAA and implemented provisions from the HITECH Act. Notable changes include the following:
- Extending HIPAA requirements to business associates and subcontractors.
- Strengthening rules for breach notifications and privacy protections.
- Adding safeguards for genetic information -- as part of Genetic Information Nondiscrimination Act (GINA) compliance.
- Limiting the use of PHI in marketing, fundraising and data sales.
- Increasing patient rights to restrict disclosures and access their own data in digital formats.
- Enhancing enforcement measures, including higher penalty tiers.
What are HIPAA business associates and their contract requirements?
A business associate is any person or organization that performs services for a HIPAA-covered entity and requires access to PHI.
Here are some examples of BAs:
- Third-party claims processors.
- Medical transcription services.
- Cloud storage providers.
- Consultants or auditors with access to patient records.
- Mobile app developers under contract with providers.
A Business Associate Agreement is required between the covered entity and the BA. This legal document must do the following:
- Define permitted uses of PHI.
- Require compliance with HIPAA safeguards.
- Mandate breach notification procedures.
- Include terms for termination and reporting noncompliance.
Subcontractors of BAs must also adhere to HIPAA rules under the same conditions.
HIPAA compliance checklist for organizations
To streamline their compliance strategy, healthcare organizations and vendors can follow a HIPAA compliance checklist. This ensures that policies, technologies and training programs are aligned with regulatory requirements.
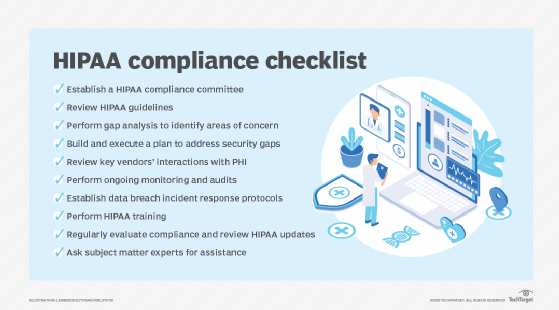
Key components of a HIPAA compliance checklist include the following activities:
- Conduct a risk assessment to identify vulnerabilities in handling PHI and ePHI.
- Appoint a HIPAA privacy and security officer to oversee compliance efforts.
- Create written HIPAA policies and procedures, including privacy practices, breach response plans and patient rights documentation.
- Provide employee training on HIPAA rules and company policies.
- Execute BAAs with all business associates and vendors.
- Implement security controls, such as firewalls, encryption, secure logins and physical safeguards.
- Monitor for breaches and maintain audit logs to support investigations.
- Regularly review and update security and privacy practices in response to changes in technology or regulations.
Following a checklist ensures that HIPAA isn't just a one-time project but an ongoing program of risk management and organizational accountability.
Balancing AI deployments with HIPAA compliance poses risks. Learn how to navigate major compliance risks associated with AI and HIPAA.





