Getty Images/iStockphoto
Understanding the FTP PORT command
FTP uses control and data channels, each using a separate TCP port. Port 21 is for the control channel, and port 20 is for the data channel. Learn how these two channels are used.
You may already know that, when FTP commands cross the wire, they use TCP port 21 by default. You may also know that port 20 is assigned to the FTP data channel by default. For further reference, see the ftp-data entry in the Service Name and Transport Protocol Port Number Registry on the Internet Assigned Numbers Authority, or IANA, website.
Even though port 20 is assigned to the FTP data channel, most FTP data sessions don't use port 20, unfortunately. Individual control and data channels are used to separate control commands from large file transfers. Let's look at how FTP works and the purpose of the PORT command.
What is the FTP PORT command?
FTP communications use two TCP port number values: one for commands -- port 21 by default -- and one for data transfer. This is where the PORT command comes into play.
The PORT command is sent by an FTP client to establish a secondary connection (address and port) for data to travel over. In some FTP implementations port 20 is used for data, but that is the exception rather than the rule.
An FTP client sends a PORT command to the FTP server to identify what port the client will be listening on for the data channel connection. Upon receipt of the PORT command, the server establishes a new TCP connection to the client using that TCP port value. This is illustrated in this active FTP diagram.
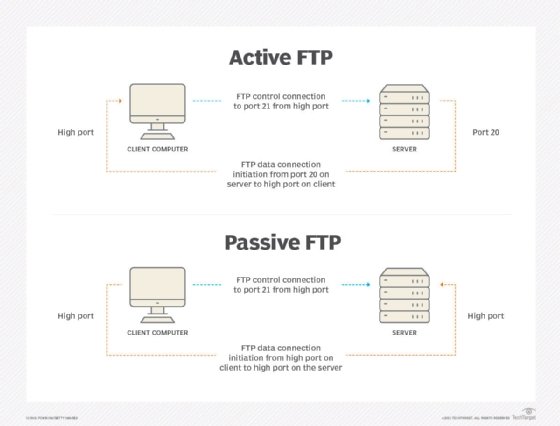
Typically, in a packet trace of active mode FTP, you'll see the data channel originating from server port 20 to a dynamic client port number. IANA states that this range should be between 49152 through 65535, but most likely, you'll see your application using a port just above 1024 -- the area that used to be the dynamic port number area.
You may see numerous PORT commands issued during a single FTP session -- a new data channel must be established to transfer directory listings and perform file GET and PUT operations.
Active mode FTP does have a problem. It doesn't work when the client is behind a firewall or when network address translation (NAT) is used on the client's network. Passive mode FTP was created to solve this problem. It relies on the client sending a PASV command to the server over the control channel. The server response includes a high port number that the client should use to open the data connection -- see the passive FTP diagram above.
Mixed IPv4 and IPv6 networks require the use of extended passive mode commands EPRT and EPSV to instruct the client and server to support both address types as described in RFC 2428.
Other FTP commands and response codes
Many other FTP commands can create a directory, remove a directory, list files in a directory, remove a file, set file type (ASCII/binary) and copy files.
The responses to the FTP commands are numeric response codes that mean different things. About 50 codes exist in the following ranges:
- 100-199 represent "command received, processing underway."
- 200-299 indicate success, perhaps with other conditions.
- 300-399 report success and that the server is waiting for additional data.
- 400-499 and 500-599 signify errors.
FTP security
The FTP default data transport mechanism does not provide any security -- all commands and data are sent unencrypted. RFC 2228, FTP Security Extensions, defines extensions to provide secure authentication, as well as control and data channel encryption, known as FTP Secure, or FTPS. Three commands support this secure mode:
- AUTH TLS negotiates a Transport Layer Security (TLS) connection on the control channel.
- PBSZ 0 sets the encryption buffer size and set to zero for TLS.
- PROT P enables TLS encryption of the data channel.
An alternative Secure FTP is based on the Secure Shell security mechanism.
In summary, the PORT command is used in FTP to communicate the TCP port number to use for the data transfer channel. In active mode FTP, the client uses the PORT command to tell the server which high-numbered port the client will use for the data channel, and the server opens a connection to that port. In passive mode, the PASV command is sent by the client, and the server responds with the high-numbered port on which it will accept the data connection. The result supports operation of FTP with firewalls and NAT. Further enhancements to FTP support IPv6 and improved security.