
Getty Images/iStockphoto
Ransomware actors increasingly demand payment in Monero
Though Bitcoin is still the cryptocurrency standard in ransomware payment demands, Monero has gained prominence due to its more private, less traceable technology.
More and more threat actors are demanding to be paid in Monero following ransomware attacks, according to infosec experts who work in the ransomware response process.
Monero, also known as XMR, was originally released in 2014 as a privacy-focused cryptocurrency. While Bitcoin is a more public and traceable coin, Monero is known as an anonymity-enhanced cryptocurrency (AEC) or "privacy coin" that utilizes various technologies to obscure transactions and prevent users from being identified.
The currency has a sizable development community with a strong base of privacy advocates and cypherpunks, and Monero's official website describes the coin as "confidential" and "censorship-resistant." However, because of the technological benefits, Monero has been used increasingly in illicit transactions on the dark web.
Many major dark web markets now accept Monero along with Bitcoin, and one of the most popular in recent years, the now-defunct White House Market, transitioned into an XMR-only market in late 2020. And according to experts, more threat actors are demanding Monero after ransomware attacks as well.
Jason Rebholz, CISO at Boston-based cyber insurance company Corvus, said he's seen threat actors pressure victims into paying in Monero.
"Bitcoin remains the prominent cryptocurrency leveraged during ransomware negotiations. We are seeing an emerging trend where ransomware actors first demand payment in Monero at a discounted ransom amount," he said. "When ransomware negotiators push back to pay in Bitcoin due to the anonymity concerns with Monero, the ransomware actors inflate the ransom by as much as 20%."
In one example of this, DarkSide, the gang behind last year's Colonial Pipeline attack, accepted both Monero and Bitcoin but charged more for the latter because of traceability reasons. REvil, which gained prominence for last year's supply-chain attack against Kaseya, switched to accepting only Monero in 2021.
Guillermo Christensen, a partner with law firm Ice Miller who specializes in cybersecurity incidents such as ransomware, said he's seen this inflation range from 5% to 20%. And while Bitcoin is still the dominant cryptocurrency used in ransomware demands, he estimated roughly 5% to 10% of threat actors are demanding XMR.
"Monero has definitely entered the awareness of the threat actors as a better way to handle payments. I think some of it is driven by the way the FBI managed to intercept one of the wallets involved in the Colonial Pipeline attack, but I also think threat actors are getting much more sophisticated," Christensen said.
"If you go back, even like a year, year and a half ago, I don't know if [threat actors] knew or realized that the traceability of Bitcoin was so strong, but they really didn't care because they were able to operate with a great deal of effectiveness in an environment. Nobody's really chasing the currency; nobody's chasing the wallets," he said. "As soon as that became something they had to worry about, they immediately responded."
Catherine Lyle, head of claims & attorney at cyber insurance firm Coalition, echoed that it has become more common over time for threat actors to demand ransoms in privacy coins, but gave a significantly lower estimate than Christensen.
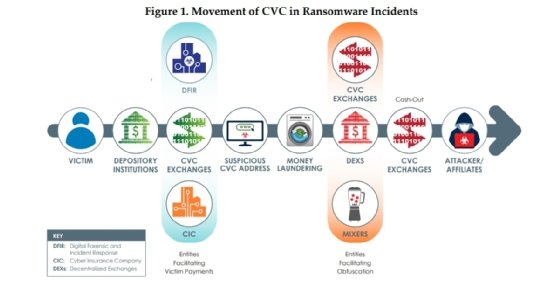
"In 2021, it became increasingly common for threat actors to request payment in AECs such as Monero," she said. "This corresponds with the trend of threat actors avoiding tracking via 'chain hopping,' not reusing wallet addresses and migrating from centralized exchanges. Despite these efforts and the increasing use of Monero, the rate of requests for ransom payment in Monero is still low -- maybe one in 100 attackers. Threat actors seem to understand that compliance with U.S.-based exchanges, many of which have delisted Monero, matters, and they simply want to be paid."
Lyle added that Coalition "will not pay [the ransom] on matters where threat actors are only willing to accept anonymity-enhanced cryptocurrencies like Monero."
Regulators have paid additional attention to AECs like Monero as privacy coins have become increasingly prolific. The IRS, for example, awarded Chainalysis and Integra $500,000 contracts in 2020 to develop Monero tracing tools, with an additional $125,000 on the table if either succeeded. The U.S. Treasury's Financial Crimes Enforcement Network (FinCEN) has also repeatedly mentioned AECs in its advisories and documentation.
As of this writing, the current value of Monero is approximately $200 USD per coin.
Alexander Culafi is a writer, journalist and podcaster based in Boston.







