
Getty Images/iStockphoto
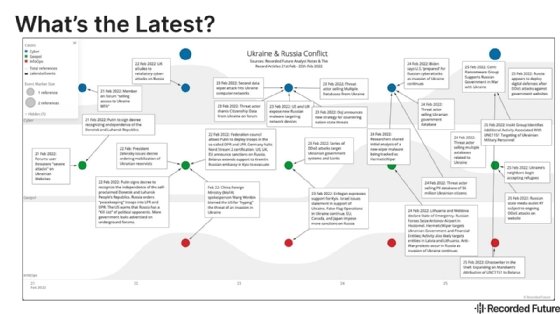
Recorded Future: Russia may retaliate with cyber attacks
Recorded Future warned U.S. and European organizations could be hit by 'spillover attacks' or intentional retaliatory strikes from Russia following its invasion of Ukraine.
Retaliatory cyber attacks against Western organizations that support Russian sanctions are a real possibility, according to Recorded Future.
During a briefing on Monday about Russia's full-scale invasion of Ukraine, Craig Terron and Brian Liston, threat analysts with Recorded Future's Insikt Group, discussed potential threats and attributions, as well as mitigation recommendations. Reports and data analyzed so far, including an increase in activity before the invasion, "suggest that Russia and Western governments are in a standoff waiting to see who conducts a cyber attack first," according to Terron.
Advanced persistent threat (APT) groups like Belarusian government-linked UNC1151, as well as the prolific ransomware gang Conti, potentially offer Russia a way to retaliate.
Prior to the invasion, Russian law enforcement announced the arrests of REvil ransomware members and the shutdown of SkyFraud, a forum used to sell stolen credit cards. Now Terron said Russia "no longer" possesses that same incentive to crack down, especially on ransomware groups.
"Similar to Russia's use of private military companies, pushing cybercriminal groups targeting the Western organizations is in line with the Russian strategic goals, while providing the Russian government with an opportunity to deny involvement in the attacks," Terron said during the webinar.
One example he cited was the likeliness that the Russian government "operated from, trained individuals in, leveraged infrastructure located in or conducted joint operations with Belarusian entities engaged in UNC1151 activity."
During the invasion, Insikt Group analysts observed UNC1151 infrastructure targeting Ukrainian military personnel. One specific threat organizations should be aware of is the data wiper malware dubbed HermeticWiper.
One day prior to the full-scale invasion of Ukraine, reports surfaced that the wiper malware was installed on hundreds of machines in Ukraine, with some victims being compromised as early as November of last year. While analysis of the malware's timestamp showed it may have been prepared two or three months ago, Terron said that could have been manipulated.
Based on the timing of the attacks, which was one day before the invasion, as well as similar attack patterns using coordinated DDoS and wiper malware, Insikt Group assessed that "it is likely these attacks were conducted by Russian state-sponsored or state nexus threat groups."
"It's plausible that these attacks will unintentionally impact organizations in other countries, such as with HermeticWiper and other Russian-state sponsored destructive malware attacks that are spun out of control, including NotPetya and Bad Rabbit in 2017," Terron said during the webinar.
Though cyber retaliation from Russia is a possibility, Terron noted the "significantly well-coordinated response from the West" that included sanctions and removing selected Russian banks from SWIFT (Society for Worldwide Interbank Financial Telecommunication) network. Insikt Group told SearchSecurity it's plausible that Russia expulsion from SWIFT could result in attacks on the system, but they have no indications of that at this point in time.
"Given the breadth of sanctions levied thus far against Russia, though, SWIFT is just one of a multitude of potential targets for a cyber response for Moscow," Insikt Group said in an email to SearchSecurity.
In addition to possible cyber attacks, Liston warned of disinformation campaigns. After the invasion, Insikt Group observed deepfake videos being spread online; Liston said he believes it is likely that Russian propaganda will continue to spread with the intention to "create confusion and uncertainty about the progress of its invasion." He noted several recent instances of social media accounts posing as Ukrainian politicians or military figures.
"We really anticipate, and this is very likely, that Russia will have to interfere in the domestic and political affairs, NATO and EU countries, both in retaliation for the West's response to the invasion and then the broader hope of promoting political leaders and government coalitions," Liston said.
Recorded Future CEO Christopher Ahlberg briefly discussed the combined use of these tactics during his introduction to the webinar Monday.
"We at Recorded Future stated for a long time that the future of war is a convergence of kinetic, cyber and information operations. We are observing that right now," Ahlberg said during the webinar.
Mitigation steps
Primary attack vectors that Insikt Group observed before and during Russian's invasion of Ukraine include DDoS attacks, website defacements, fraudulent message and destructive malware attacks.
While strong cyberhygiene is essential across all industries, Liston emphasized its importance in the media and technology fields and recommended multifactor authentication as well as complex passwords.
Terron cited several factors "to mitigate the risk of spillover attacks," including implementing incident response plans for HermeticWiper and WhisperGate, another recent data wiper. He also advised that organizations keep up to date with government advisories such as the recent alert on the Russian-based APT Sandworm and its use of a new malicious malware.
On Saturday, CISA issued another joint advisory with guidance on both HermeticWiper and WhisperGate, which the agency described as "destructive malware that has been used to target organizations in Ukraine."
Protecting against ransomware attacks is also important, Terron said, including backup maintenance and data network segmentation.
"Organizations should dedicate resources to understanding which Russian entities and individuals have been sanctioned and to ensure full compliance with those sanctions," Terron said.







