Counter threats with these top SecOps software options
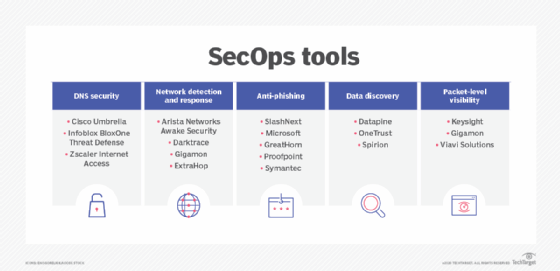
SecOps tools offer many capabilities to address common threats enterprises face, including domain name services, network detection and response, and anti-phishing.
SecOps teams need to harness a different mix of tools to bulk up defense strategies and more effectively buttress the three pillars of SecOps: protect, detect and respond. Even a small weakness in enterprise security can lead to big problems, and standard perimeter defenses, like firewalls and VPNs, no longer shield against more modern and sophisticated security threats.
Many product types have emerged, building upon the traditional ones, which can help keep hackers out while reducing the dwell time of those threats that do infiltrate the system. Some of these tool categories, like domain name services and anti-phishing, primarily focus on security, while others -- among them ecosystem- and packet-level visibility -- provide benefits more ancillary to SecOps.
SecOps challenges and SecOps software evolve constantly. While enterprises should not abandon legacy products, it is essential to think about newer software and systems that can better secure a modern environment.
DNS security
DNS translates the common website names users type into their browsers into the actual IP addresses of those resources. As a result, DNS requests are commonplace. Because they are essential, they're not blocked by network firewalls.
Hackers often take advantage of this loophole, actively exploiting the DNS protocol to compromise and attack company resources. A favorite tactic is to "piggyback" rogue data onto otherwise legitimate DNS requests and responses. As a result, the systems processing those DNS requests -- as well as the firewalls -- overlook the malicious data, opening up a channel for attacks to occur in the process.
Malware that infiltrates a user's computer can use DNS to circumvent the firewall, ultimately exfiltrating sensitive data. It can also reroute legitimate DNS requests to malicious DNS servers, thus ushering in additional malware.
To neutralize these attacks, DNS security platforms parse all the data from each DNS request and response packet and then look for "extra" data unrelated to the DNS request and match this to a threat intelligence database -- a process that's similar to intrusion prevention systems'. DNS security platforms also maintain lists of rogue DNS servers that are known to be controlled by hackers or contain malicious code.
Leading DNS security products include Cisco Umbrella, Infoblox BloxOne Threat Defense and Zscaler Internet Access.
Network detection and response
Among other features, firewalls protect businesses by blocking unused ports. Intrusion protection systems inspect packet signatures for malware. But hackers have found ways to penetrate these systems.
In turn, network detection and response (NDR) tools have emerged to provide extra protection against these next-generation attacks.
NDR tools are especially effective in detecting low and slow attacks. Low and slow attacks occur over time through malware that has penetrated the firewall, often through BYOD laptops or IoT devices, like sensors or security cameras.
While low and slow attacks share the common goal of taking over systems or exfiltrating data, their execution depends on "blending" malicious traffic with real traffic to make detection more difficult. As a result, admins must monitor network traffic over time to detect these kinds of attacks. NDR counteracts these attacks by using AI to analyze typical traffic and building models of what is normal; the software then detects the minor aberrations inherent in low and slow attacks and ultimately alerts SecOps teams.
Leading NDR vendors include Arista Networks' Awake Security, Darktrace, Gigamon and ExtraHop.
Anti-phishing
Employees' clicking on a phishing, or spoofed, URL is one of the most common ways for malware to enter an enterprise's network, either through harmful code or the collection of stolen credentials. Phishing is nothing new, but attacks have grown more elaborate, with techniques such as whaling and spear phishing used to penetrate network defenses.
With more sophisticated attacks, enterprises need more sophisticated protection.
One way to do that is to use security software capable of performing intensive analysis. These products use big data to analyze not just the email itself, but the relationship of the sender and the sender's company to determine if previous communication had occurred and how much risk the sender represents. By viewing the communications and relationship in context, these products can provide a more detailed and accurate assessment of email-based threats.
Biometrics is another technique. Here, the software "learns" a user's typing rhythm and verifies a user's identify before any emails can be sent.
Email is not the only vehicle for phishing. These attacks can also arrive in the form of clickable URLs through common applications like Facebook and LinkedIn, motivating security vendors like SlashNext to protect at the browser level rather than the inbox level.
Leading anti-phishing vendors include SlashNext, Microsoft, GreatHorn, Proofpoint and the Symantec unit of Broadcom.
Data discovery
To successfully protect computer data, admins must know its location. Data discovery tools help admins determine where sensitive data resides. Data discovery can be challenging, reflecting the complexity underlying most organizations' data storage strategies. At a minimum, admins must determine where sensitive data is stored -- in server files, databases or both. While data discovery platforms can scan server folders, databases are another matter. Databases have specific structures and specific APIs required to access their data, and thus, data discovery products have to be tailored accordingly. Customers need to use a tool that expressly offers support for the database products their company uses.
Pinpointing where the data is physically stored is another challenge. More and more organizations are moving to a hybrid storage model where some file servers and database servers reside physically on the premises of the business and others reside in cloud services such as AWS or Microsoft Azure. In such hybrid environments, users must take additional steps and support additional APIs to ensure access to cloud-based data resources.
With successful data discovery capabilities, SecOps teams can do the following:
- consolidate information in fewer places for easier protection;
- provide additional security for servers holding sensitive data; and
- implement packet capture for all sessions accessing that data.
Granted, few SecOps teams have responsibility for the actual data or its server location. Armed with the knowledge of where data resides, though, the SecOps team can help guide the application teams in providing the most secure environment for that information.
Vendors in this space include Datapine, OneTrust and Spirion, with many more to choose from depending on the organization's specific discovery requirements.
Packet-level visibility
Full packet capture and storage are the most effective tools for real-time remediation and after-the-fact analysis. While real-time stats and metadata are useful, they cannot tell the full story or enable the SecOps investigation team to learn the full extent of an attack or data exfiltration incident.
Admins need a combination of devices to store and analyze packet data. They can also use a packet broker to tap different segments of the network, filter and deduplicate traffic as required, and send the output network traffic to a storage system for real-time and historical analysis.
This task gets more challenging as 40 Gbps and 100 Gbps links become commonplace in the data center. As more data flows through the network, the capturing system -- and associated storage devices -- must be able to keep pace.
Vendors in this space include Keysight, Gigamon and Viavi Solutions.
Tying it all together
A successful SecOps strategy depends on having the information you need -- when you need it. To that end, it's essential that critical data can be shared among all the components and elements that make up your security perimeter.
Prospective buyers should consider if threat intelligence capabilities from one security vendor feed into other, third-party security devices, as well as determine if APIs can be used to make dynamic protection adjustments in their environments. Ultimately, buyers must understand how security elements from different vendors work together to make their environments more secure.







