
What is identity sprawl and how can it be managed?
With identity-based attacks on the rise, organizations need to prioritize identity management. Learn about identity sprawl, why it's a risk and how it can be managed.
Do your employees have different usernames and passwords for their computers, file-sharing apps and Zoom accounts? If the answer is yes, your organization is suffering from identity sprawl.
Identity sprawl occurs when users have numerous accounts and identities managed by multiple systems that are not synchronized.
Unfortunately, identity sprawl puts enterprises at high risk of identity-based attacks. A 2022 survey from Identity Defined Security Alliance revealed 84% of respondents had experienced an identity-related breach in the past year.
In addition, Verizon's "2022 Data Breach Investigations Report" found 61% of all breaches involved exploited credentials -- a troubling statistic considering the prevalence of identity sprawl today.
Why is identity sprawl a challenge?
Identity sprawl isn't a new problem, but the issue has grown substantially since the adoption of remote and hybrid work models. A 2021 survey from Dimensional Research, sponsored by One Identity, found 84% of respondents had more than double the number of user identities than 10 years ago, with 51% reporting they used more than 25 different systems for identity management.
When organizations relied solely on desktops protected by traditional perimeter defenses, network admins typically used Active Directory (AD) to manage passwords and usernames.
As the perimeter dissolved with employees working remotely and as more online services, such as Skype, Dropbox, Zoom, Slack and Salesforce, were introduced, organizations suddenly had employees using multiple usernames and passwords. And, as the number of identities per employee grew, so did the number of systems managing them. Admins struggled to synchronize or integrate the new systems with existing central directory services. As a result, many organizations were left with a vicious and widening circle of user identities and identity management tools and had no central source to hold accurate and complete user profiles and privileges.
Cloud-based applications and services exacerbated the issue. Often used in hybrid and remote work models, these apps and services often not only require users to have separate identities, but they typically have their own user provisioning processes and systems to manage identities.
A hodgepodge of management systems slows down user provisioning and leads to ghost accounts, inconsistencies in user privileges, and challenges enforcing security and compliance policies. Users managing multiple accounts can also succumb to password fatigue, causing them to reuse the same passwords for different applications and services.
How to manage identity sprawl
A unified approach to identity management is needed to reduce identity sprawl and close potential avenues of attack. However, organizations often struggle with identity management due to varying requirements from different departments and the limitations in identity management products. It's rare for an organization to address all four access management disciplines holistically:
- AD management and security
- privileged access management (PAM)
- Identity governance
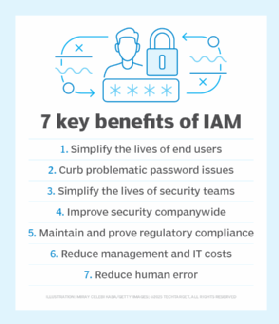
- identity and access management (IAM)
Unfortunately, no single on-premises or as-a-service IAM platform or directory service can solve identity sprawl completely nor unify all disparate identity systems. Companies, therefore, still tend to deploy multiple systems.
A few options to consider adopting are identity consolidation, certain PAM platforms, identity orchestration and IAM centralization.
Identity consolidation
Identity consolidation -- the discarding and replacement of existing identity management systems -- may seem an obvious way forward. It should only be done, however, after a careful review of the purpose behind the system's initial deployment. Was it deployed because it offered multifactor authentication or highly resilient directory services? Discarding such features could be an expensive step backward as such features will need to be replaced by another tool or may require costly reworking of unsupported applications and services.
PAM
Another solution is to use a PAM platform with multidirectory brokering capabilities. This enables organizations to authenticate users against any identity directory, such as AD, Okta, Ping or Identity as a Service.
Identity orchestration
An alternate approach is identity orchestration. This adds an abstraction layer that applications can use to integrate with the enterprise's various identity systems without having to change any application code. Identity orchestration replicates identities and policies across identity systems by retrieving identity data from various identity stores and routing login requests to the correct identity provider.
Identity orchestration aims to unify incompatible identity systems' APIs, data models and access policies into a consistent identity Fabric. Orchestration requires time and resources, but it reduces administrative overhead and simplifies the enforcement of consistent access and privilege policies across an organization's IT ecosystem.
IAM centralization
The best long-term approach to get identity sprawl under control is to create a single source of truth by centralizing the identities of all users, devices and applications. PAM and IAM teams need to create global profiles of every identity, correlating and cross-checking the attributes and privileges across every source of identity data, and ensure their privileges match their roles. This is a big challenge as the data has different formats and schemas. An even bigger challenge, however, is to then replicate or synchronize this central image with each identity silo.
Effective identity management secures IT environments and prevents future increases in duplicate machine and human identities -- an essential step in preventing cybercriminals from using credentials to gain a foothold in a network. Identity management also helps the IT department incorporate new technologies without causing identity sprawl in the future.








