Getty Images/iStockphoto
IBM FlashSystem adds storage as a service, attack protection
IBM introduces new consumption-based Storage as a Service for FlashSystem based on performance, capacity and contract term; and adds Safeguarded Copy to guard against cyberattacks.
IBM turned its FlashSystem focus to two hot areas in enterprise storage with new as-a-service options that let customers add on-premises infrastructure the way they do in the public cloud and data protection capabilities to guard against cyberattacks.
The new IBM Storage as a Service, due in September, will let customers procure and pay for on-premises FlashSystem infrastructure based on the performance, capacity, connectivity, encryption and service commitment terms they choose, from one to five years. Customers would pay only for the storage they use, shifting from a Capex to an Opex financing model.
"There's an element of everybody's doing storage as a service, so we'd better do it too," admitted Chris Saul, program director of product marketing for IBM Storage. "But we're not doing it in a vacuum. We are doing it because customers are asking us for it, and we have validated that the storage-as-a-service offering that we've built is the sort of thing they're looking for."
On the security front, in August, FlashSystem customers will gain the option to use Safeguarded Copy software that IBM previously made available in its DS8000 systems to protect data against ransomware and cyberattacks. IBM said the technology would let customers schedule up to 15,000 point-in-time snapshots that are logically air-gapped into secure pools on the storage system. Safeguarded Copy will be free with FlashSystem storage.
Service goes beyond Opex model
IBM has sold FlashSystem through the traditional Capex model and, since 2017, via a consumption-based IBM Storage Utility option. But the new Storage as a Service option will go beyond the Opex financing model and place IBM in control of the configuration, installation, tuning, maintenance and support of FlashSystem.
IBM Storage as a Service includes the company's Storage Insights Pro cloud-based monitoring tool, software support and remote system updates, round-the-clock response time within four hours on hardware, a personalized concierge service and a technical account manager for problem resolution. IBM said it would monitor capacity growth to see if a customer needs more storage, do periodic technology refreshes and recycle old equipment at the end of the contract.
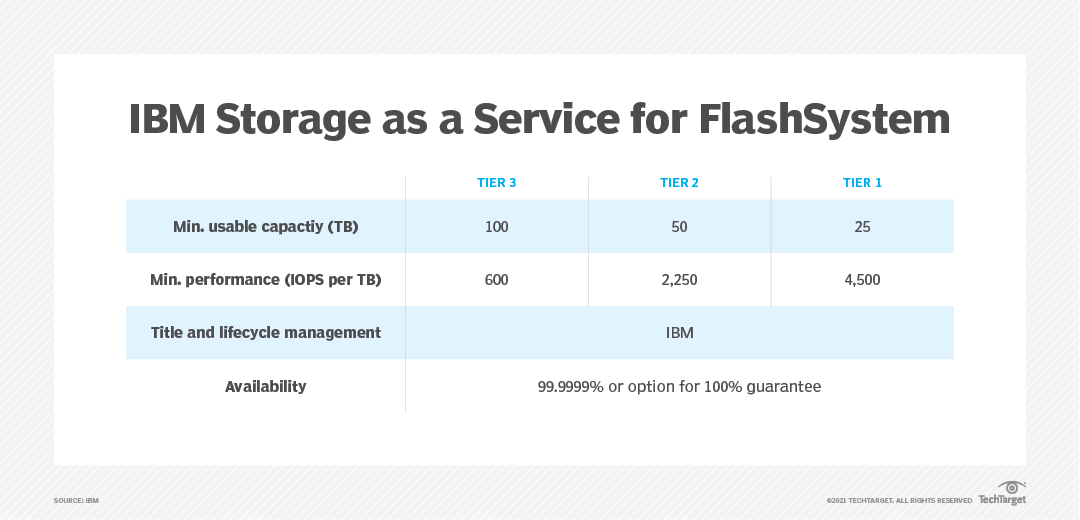
Customers can choose one of three FlashSystem service tiers, with options for 100% guaranteed or 99.9999% availability. The minimum usable capacity for Tier 1 is 25 TB, with performance at 4,500 IOPS per TB. Tier 2 starts at 50 TB and 2,250 IOPS per TB, and the Tier 3 minimum is 100 TB at 600 IOPS per TB.
Saul said IBM delivers an additional 50% of storage capacity at the outset to allow for growth. Whenever a customer hits 75% of the storage capacity, IBM automatically sends new storage to restore the 50% extra capacity figure, he said. Saul estimated a customer would need 10 minutes to start up the additional storage.
The initial FlashSystem deployment could take two to two-and-a-half weeks from order to installation, or roughly the same time required for a capital purchase, according to Eric Herzog, the company's chief marketing officer and vice president of global storage channels.
IBM Storage as a Service is due to roll out in North America and Europe in September and later expand to other regions -- the same approach IBM took with its Storage Utility rollout. Pricing varies based on the length of commitment, tier of storage and capacity.
Cost comparisons
Saul claimed IBM Storage as a Service would cost less per TB per month than comparable tiers of AWS Elastic Block Storage and be "extremely competitive" with the storage-as-a-service options from competitors such as Dell and Pure Storage. He would not offer price comparisons between similar configurations of Opex-based FlashSystem as-a-service and Capex-based FlashSystem purchases over the same time frame.
Paul Nashawaty, a senior analyst at Enterprise Strategy Group (ESG), which is a division of TechTarget, said shifting budgets from Capex to Opex can be desirable for many organizations but is not necessarily the best approach for all businesses. "Taking into consideration the data center costs and the IT staff to manage it is a factor," he said.
But Nashawaty said the storage-as-a-service model is growing in popularity. Close to 50% of the 668 global IT and business professionals that responded to a recent ESG survey said they prefer a consumption-based model where they pay for data center infrastructure based on hardware utilization as a variable monthly subscription, he said.
"The adoption of higher-end workloads at the edge may be a logical [place] for the storage as a service," Nashawaty said. Having the ability to "burst" using an as-a-service model might be especially attractive for organizations such as healthcare providers and retailers, he added. "The ability to have a managed service, and not have the IT staff focused on resource refresh, is attractive to clients," Nashawaty said.
How Safeguarded Copy works
Whether purchasing FlashSystem through a traditional Capex model or the new Opex service approach, customers will have access to the Safeguarded Copy technology to protect their data against ransomware attacks. The immutable data copies are inaccessible to unauthorized users and cannot be connected to servers, Saul said.
"The copies are created using conventional snapshot technology -- which is almost instant. The restore uses the same technology, so we can restore data after an event very quickly," Saul claimed. "We've seen people where recovery has taken them days or even weeks, and with Safeguarded Copy, our objective is to bring that down to minutes or perhaps hours."
Customers can set policies for the frequency of the immutable snapshots and the retention period. Saul said the fastest default setting is one copy every six hours, with a retention period of seven days. IBM's Safeguarded Copy also lets customers establish separate privileges for administrators to guard against internal threats posed by disgruntled employees.
Krista Macomber, a senior analyst at Evaluator Group, said one common way bad actors circumvent the immutability of data copies is by gaining administrative access to shorten retention periods or tamper with the storage system's clock. She stressed the importance of IT organizations exercising role-based control over who can access data copies.
"Immutability is an important piece of ransomware protection because it can inhibit the malicious actor from encrypting or deleting data, but it shouldn't be the entire ransomware protection strategy," Macomber said.
IBM integrated Safeguarded Copy with its separately licensed Security QRadar security information and event management software to enable customers to trigger a Safeguarded Copy snapshot at the first sign of a threat, such as an individual attempting multiple logons or an employee entering the data center in the middle of the night, Saul said.
Customers also have the option to purchase IBM's Copy Services Manager to configure, manage and monitor data copy functions and identify the most recent good copy of the data for restoration purposes.
"The problem with malware is that it can get into your data center, and it can be making changes to data, and you don't know that it's making changes," Saul said. "So, the best practice with Safeguarded Copy or any approach is periodically to mount one of these copies that you've made and validate that the copy is good. The storage system can't do that itself, because it can't tell the difference between malware updates to the data and regular conventional application updates to the data."
IBM also offers customers a no-charge IBM Cyber Resilience Assessment, based on the National Institute of Standards and Technology Cybersecurity Framework, to assist customers in identifying potential trouble spots and to provide corrective recommendations.
Carol Sliwa is a TechTarget senior writer covering storage arrays and drives, flash and memory technologies, and enterprise architecture.
Johnny Yu covers enterprise data protection news for TechTarget's Storage sites SearchDataBackup and SearchDisasterRecovery. Before joining TechTarget in June 2018, he wrote for USA Today's consumer product review site Reviewed.com.






