What is application migration? Examples and best practices
Application migration is the process of moving an application program from one environment to another. Organizations migrate applications for various reasons, including to reduce costs, improve performance, increase scalability and enhance security and compliance.
Migrating to modern platforms allows companies to use technologies such as AI and machine learning to automate tasks and optimize resources. Migration examples include moving from an on-premises enterprise server to a cloud provider's environment or from one cloud environment to another.
Migrating an application can be complicated because there are often differences between the original and target environments. In addition, applications -- even cloud applications -- are not typically designed to be portable. Applications created on various cloud development platforms, such as Microsoft Azure and Google App Engine, are usually designed to run on the platforms on which they were developed. Other elements, such as operating systems (OSes), management tools, the networking architecture, the storage system and the virtual machine (VM) configuration, can all differ from those in the environment in which the application was developed or deployed. A successful application migration might require middleware products to bridge any gaps between technologies.
Why migrate applications?
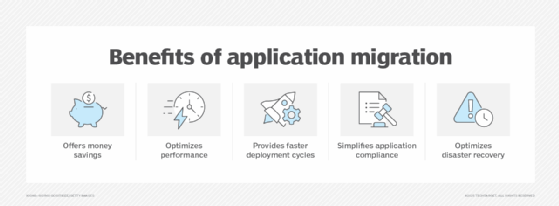
As mentioned above, there are several good reasons to move applications from one environment to another, for practical, economic or strategic reasons. These can include the following:
- Save money. Moving applications from an on-premises environment to the cloud or a hybrid environment reduces infrastructure and associated maintenance costs, as well as personnel requirements.
- Improve performance. In environments with optimized architecture, application speed and reliability are often improved, and dynamically scaling the application to accommodate fluctuating workloads is often possible.
- Better business response. Modernized environments generally accommodate Agile development, making possible faster deployment cycles that lessen time to market. Extending application access worldwide is also easier and less expensive in a cloud environment.
- Compliance. Migrating applications into a cloud environment that is already compliant with data sovereignty laws simplifies application compliance.
- Disaster recovery. High-availability cloud architectures generally provide multi-region failover, simplifying disaster recovery.
Application migration examples
The following are several common scenarios within which application migrations occur:
- On-premises-to-cloud. The migration of applications from in-house infrastructure to public or private cloud environments is an almost inevitable stage of any organization's digital transformation. Legacy customer relationship management and enterprise resource planning systems, for instance, are already in place in most companies and can be better managed and scaled in Azure, Amazon Web Services (AWS) or some other cloud hosting environment.
- Cloud-to-cloud. Increasingly, companies that have already moved applications to a cloud environment find that they can reduce costs or achieve better integration in a different cloud environment; similarly, it is possible to avoid vendor lock-in by deploying applications across multiple clouds, such as AWS and Google Cloud, for instance.
- VM migration. For improved scalability, it can be useful to migrate VMware workloads from an on-premises environment to VMware Cloud on AWS.
- Database migration. Migrating a legacy database from an on-premises environment to a cloud-based relational database service such as Amazon Relational Database Service or PostgreSQL can reduce storage costs while improving access and maintainability, and can offer opportunities for convenient retooling and rearchitecting.
- Hybrid integrations. It can be desirable to keep highly sensitive applications, such as financial applications, hosted on-premises, while integrating those applications with cloud-based analytics platforms, for enhanced data utility and ease of access.
6 application migration strategies
There are several strategies for migrating applications, including the following:
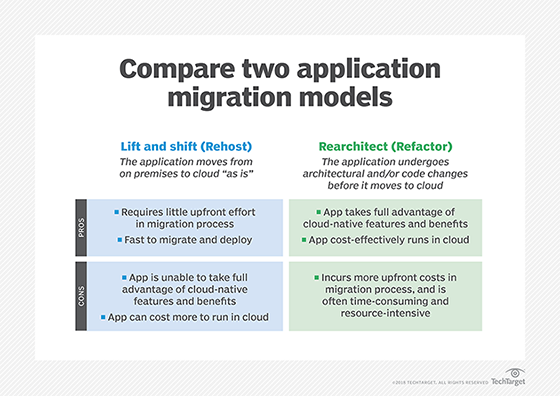
Rehosting
Also known as lift-and-shift, this method moves the application without making any changes, essentially replicating the existing infrastructure in a new environment.
Pros: Lift-and-shift migrations tend to be faster than other methods and are convenient when time does not allow for rearchitecting applications or their data sources. They also tend to be more cost-effective in the short term, when legacy applications do not require any immediate changes, and usually cause minimal disruption to the business.
Cons: The long-term costs of this can be higher than those of other options because this approach does not take advantage of cost savings from the cloud model. They can create bottlenecks for the same reason, failing to exploit cloud-centric optimizations in ways that might compromise the user experience.
Refactoring
Also known as rearchitecting, this strategy requires an application to undergo significant changes so that it will scale within a cloud environment.
Pros: When applications are rearchitected for a new home in the cloud, they can be optimized to take advantage of the features offered by that environment, such as auto-scaling, high availability and managed services. Dynamic scaling yields long-term cost efficiencies, technical debt is reduced, and security and compliance are more easily maintained.
Cons: The up-front costs of rearchitecting for migration are usually high, lengthening time-to-market and increasing project risk. Business disruption is likely.
Replatforming
Sometimes called lift-tinker-shift, this method involves minor tweaks to an application so it can benefit from cloud architecture. It can involve upgrading, containerizing or changing the OSes.
Pros: Though it is not as clean as lift-and-shift, replatforming is generally faster and cheaper than refactoring or rebuilding. Its optimizations yield cost savings over time and improved performance for less effort.
Cons: As with lift-and-shift, replatforming might not exploit the full benefits of the cloud platform into which the application is migrated. It requires extensive planning upfront to make sure that the application's dependencies are accounted for, and it is often just a stopgap measure that must be followed by later refactoring or rebuilding.
Rebuilding
During this process, developers rewrite or rengineer an application specifically for the cloud. This option is also called a forklift replacement of the whole application.
Pros: A rebuilt application can fully exploit modern cloud-native architecture, taking advantage of microservices and containers. Rebuilding applications eliminates technical debt and offers an opportunity to more fully align legacy applications with current business needs and processes.
Cons: Rearchitecting or rebuilding an application requires greater commitment from development and operations and carries a high upfront cost. As with refactoring, it increases risk and can create operational disruptions in the business.
Retiring or replacing
In some instances, it is in the best interest of an organization to decommission the application or choose a new one.
Pros: Retiring or sunsetting an application eliminates its costs with one stroke and reduces technical debt; the business is forced to review its processes, yielding workflow improvements. Replacing an application, which is often called drop-and-shop, is a rapid modernization move, and the business's adaptation often leads to an increased standardization in processes and practices. In both cases, digital transformation is enabled.
Cons: When applications are retired, the workforce that is comfortable with them often resists; hidden dependencies often surface, increasing risk and disrupting the business. With drop-and-shop, there is less flexibility in adapting data formats and structures, which often increases the migration cost. In both cases, there will often be retraining overhead.
Application migration best practices
To help ensure a successful application migration, organizations should follow these best practices:
- Perform an assessment. The foundation of any migration project is an assessment of an enterprise's application portfolio, including any legacy systems or applications. Users must also understand the ecosystem surrounding the applications, including the configurations of the physical and virtual servers, network topology, current support and data dependencies, security and compliance.
- Involve the business as soon as possible. Make sure that all the relevant business units take part in planning the migration and are aware of how it might affect them and existing business processes. Clear communication is key.
- Map out a migration strategy. Identify the business reasons and use cases for migrating to the cloud. Decide whether to migrate in phases or maybe start with the least business-critical workloads to gain experience and then move to more mission-critical applications.
- Develop a cloud governance framework. This should consist of clear, policy-based rules to help the organization prepare for secure cloud adoption, including structures, roles, responsibilities, plans, objectives and a decision framework.
- Train staff as soon as possible. Set up a series of training sessions to get employees across different teams and business units up to speed on cloud concepts.
- Manage software licensing properly. Document all enterprise applications, closely studying their licensing as it relates to cloud computing. If necessary, check with vendors to determine if existing licenses can be updated so the applications can be used in the cloud.
- Implement automation. To enhance the overall efficiency of the migration and minimize disruption to the business, organizations should automate repetitive patterns where possible. This will accelerate the migration process, reduce risk and save money. The phased cloud migration approach and automation can work together; specifically, organizations should identify repeated patterns over time that can be automated in future migration phases.
- Test, test and retest. An enterprise without a proper testing plan will not have a successful migration. Start talking about testing on the first day of the assessment.
Challenges of a cloud migration
While there are several benefits to migrating applications to the cloud -- including improved operational efficiency, faster deployment times and lower costs -- organizations still face the following challenges:
- Lacking a defined strategy. For successful cloud adoption and implementation, organizations need an end-to-end migration plan that doesn't include any shortcuts. As some data centers and applications will be more difficult to migrate than others, a one-size-fits-all strategy won't work.
- Business continuity risks. Many businesses require that some critical applications have near-zero downtime, making live, no-disruption migration of those applications technically daunting.
- Security and compliance. When moving to the cloud, enterprises must ensure that the data they move to the cloud is secure and that they comply with all the relevant industry and government regulations.
- Systems integration. Often, applications migrating to the cloud must maintain integrations with on-premises systems, adding to the migration's complexity. Application programming interface compatibility and workflow must also be considered.
- Failing to properly calculate costs. Organizations must accurately evaluate the costs of their migrations and operations in advance to help them save money. Some things to take into consideration include capital and operational expenditures, as well as the cost of the migration.
- Skills gap. One of the main obstacles to moving applications to the cloud is finding people who have the skills to manage a migration effectively. Enterprises that don't have the resources to hire cloud migration talent should cultivate these skills internally or look for vendors that offer dedicated people to support successful migrations. These individuals can also help train organizations' employees in the necessary cloud skills.
Application migration tools
There are numerous application migration services and tools on the market, including the following:
- AWS. Amazon offers a variety of cloud migration services, such as AWS Database Migration Service and AWS Migration Hub. Most services are free for AWS customers. However, the tools only support AWS.
- Azure. Microsoft offers free Azure migration tools, including Azure Migrate, to assess and migrate workloads, and free Azure Cost Management to optimize costs for organizations moving to its Azure public cloud computing platform. However, Microsoft doesn't support any other cloud vendors.
- Google Cloud. Google offers various migration tools, such as Migration Center, a unified platform for migration and modernization. It also includes open source and container migration options.
- PlateSpin Migrate. This third-party option offers a comprehensive and highly scalable cloud migration product that supports multiple clouds and includes advanced security features, such as role-based permissions
- RiverMeadow SaaS. This multi-cloud platform is designed for automating workload replication, migration and modernization.
- VMware HCX (Hybrid Cloud Extension). This service is designed for large-scale VM migration between VMware-based environments, either on-premises-to-cloud or cloud-to-cloud.
When migrating data from on-premises to the cloud, there are two data transfer methods -- online and offline. Learn how each method works and weigh the pros and cons.







