configuration service provider (CSP)
What is a configuration service provider (CSP)?
A configuration service provider (CSP) is a component of Windows client operating systems that shows IT professionals device configuration choices and allows them to apply the settings across multiple Windows OSes.
IT can use CSPs to configure device-specific settings such as assigning file access permissions and determining application preferences on an organization-wide level. As a result, CSPs are essential for IT professionals to ensure that each device's configurations meet the organization's standards for performance, security and more before they distribute devices to users.
What is the purpose of a configuration service provider
IT can use CSPs as part of its mobile device management (MDM) process to ensure users' configurations are set to the proper standards to meet security requirements. Unified device configuration can also ease IT's management burden by setting a universal configuration blueprints.
CSPs allow IT to configure numerous device components, including cursory elements, such as wallpapers, language, and time zone, to more essential elements, including granting native tool access permissions for the Action Center, limiting application access and determining which settings a user can edit.
Further, IT can use CSPs as templates for certain user groups. For example, users in the sales department could have one configuration for their devices, while executives could have a different configuration -- each according to their priority and organizational needs. This process can save IT from manually inputting each configuration for every new device.
How organizations use configuration service providers
Many tools and applications such as Windows Configuration Designer provide an interface that IT professionals can use to set customized CSPs and deploy them appropriately.
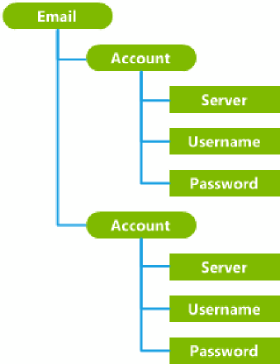
There are plenty of CSPs IT can choose from to determine a variety of settings, including EnterpriseDataProtection CSP, which IT can use to configure Windows Information Protection, and Wi-Fi CSP, which IT can use to add or delete Wi-Fi networks.
IT can also deploy CSPs through custom commands in a lockdown XML file which uses the XML metalanguage to determine how other code operates. In this case, IT would write commands for the CSP code to customize the CSP's function beyond its basic capabilities.







