Locking down Internet Explorer settings with Group Policy in IE 11
New Internet Explorer settings can tighten enterprise security, but only if Group Policy is properly enabled in IE 11 and you have Windows 8.
The Web browser wars of the past are over. There's a good chance that your enterprise has standardized on Microsoft Internet Explorer. Even with its incompatibilities and nuances, Internet Explorer is highly manageable. Group Policy Objects provide a relatively simple (and free) means to lock down what is arguably your most vulnerable piece of business software.
If you're already using Internet Explorer or if IE version 11 is on your radar – which is likely if you're a Windows 7 shop or plan to move to Windows 8.1 -- a few new generic Group Policy Objects (GPOs) can affect the following Internet Explorer settings:
- Turn off loading websites and content in the background to optimize performance;
- Allow Microsoft services to provide enhanced suggestions as to the user types in the Address bar; and
- Allow Internet Explorer to use the SPDY/3 network protocol.
In addition, you may benefit from several security-focused GPOs for IE 11:
Don't run antimalware programs against ActiveX controls
This Group Policy setting determines whether IE 11 performs malware checks against ActiveX controls. There are actually two settings: one for the Internet and Restricted zones, and one for the Intranet, Trusted and Local Machine zones.
If enabled, IE 11 won't check with antimalware software to see if it's safe to create an instance of the ActiveX control in question. Disabled, this policy setting tells IE 11 to always check with antimalware software to see if it's safe to create an instance of the ActiveX control. I can't imagine not checking, but your situation is unique, so you'll want to test to see what works best.
Turn on 64-bit tab processes when running in Enhanced Protected Mode on 64-bit versions of Windows
Disabled by default, this setting determines whether IE 11 uses 64-bit processes (for better security) or 32-bit processes (for better compatibility) when running in Enhanced Protected Mode on 64-bit versions of Windows. I suspect most enterprises will be running 64-bit Windows. Whether or not you use Enhanced Protected Mode will likely vary depending on your application and security needs.
Prevent the deletion of IE tracking data
This setting prevents users from deleting IE's ActiveX Filtering, Tracking Protection and Do Not Track exceptions for visited websites. There will likely be times where you'll want this information to be removed, or you may want to prevent such deletion. Think this through, and discuss with your security committee to determine what's best for your organization.
Always send Do Not Track header
Enabled by default, this setting tells the browser to not track the user over all HTTP and HTTPS requests. Unless you're using performing your own metrics using this information, leave this one on.
Microsoft also provides specific details on all new Internet Explorer Group Policy settings. As always, new IE 11 settings can be updated to take effect immediately through the management console or by simply running gpupdate at the workstation's command prompt.
The one thing you have to be careful with is that certain Internet Explorer settings can still be changed or disabled by the local user. This underscores the need for written policies, endpoint security controls that monitor for system changes, and an ongoing dose of security awareness and training.
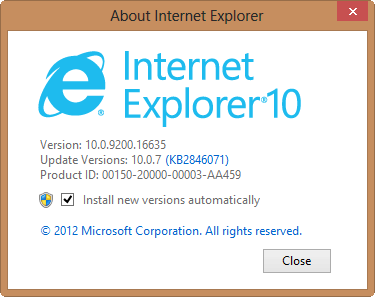
Finally, if you're not ready for IE 11 on your Windows 7 machines, Microsoft has the Internet Explorer 11 Blocker Toolkit. If you're running Windows 8, even if you have the option checked to Install new versions automatically (the default) as shown in the enclosed screenshot, you won't get IE 11.
Instead, in order to get Internet Explorer 11, you'll need to upgrade to Windows 8.1, as Microsoft proudly displays on its IE download page. If you're still running Windows Server 2003, here are the GPO administrative templates for managing IE 11.