jamdesign - stock.adobe.com
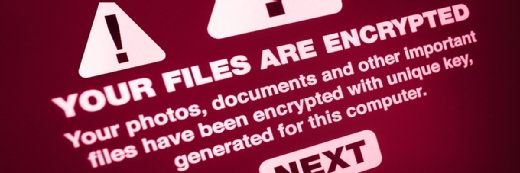
ExaGrid revealed as latest Conti ransomware casualty
The data backup vendor appears to have paid a $2.6 million ransom after Conti threat actors breached its corporate network and stole internal documents.
Data backup specialist ExaGrid has been left a bit lighter in the pocket thanks to the work of the Conti ransomware crew.
Communications seen by TechTarget sister publication LeMagIT show that ExaGrid was infected by the Conti crew back in early May and, in order to reclaim access to encrypted data, paid a ransom of 50.75 Bitcoins or approximately $2.6 million. According to LeMagIT, the stolen data included 800 GB worth of data, including employee records, nondisclosure agreements and tax documents. This included SQL Server images and other storage archives.
"As you already know, we infiltrated your network and stayed in it for more than a month (enough to study all of your documentation)," the cybercriminals wrote. "[We] encrypted your file servers, SQL servers, downloaded all important information with a total weight of more than 800GB."
Fortunately for ExaGrid, the $2.6 million payment was a significant downgrade from the $7.48 million the ransomware operators had originally demanded. Communications between the two parties show an extended back and forth in May as ExaGrid staff sought to lower the hackers' asking price. The two sides eventually reached a middle ground after negotiations hovered in the $3 million range.
Less flattering to ExaGrid, which manufactures backup appliances, was the revelation that the company had to ask for a second copy of the decryption tool after the first was deleted by accident. LeMagIT managed to obtain a plea from ExaGrid to the hackers after their team had mistakenly deleted the very expensive decryption software. The extortionists were, at least, very prompt in providing a backup and handed over the requested software within a day.
ExaGrid did not respond to a request for comment.
Falling victim to ransomware is particularly damaging for ExaGrid as the company primarily makes its name by blocking malware attacks. In December 2020, ExaGrid boasted about a number of industry awards related to its ransomware recovery offering.
At the time, ExaGrid claimed to have "the only backup storage system on the market to offer a non-network-facing tier with immutable objects and delayed deletes for ransomware recovery solution." The statement apparently did not stop the ransomware actors in this attack.
Conti attacks continue
The Conti squad, meanwhile, continues its crime spree. The ransomware crew made headlines last month by drawing an alert from the FBI after hitting hundreds of U.S. companies and causing a prolonged outage of Ireland's Health Service Executive (HSE).
The hackers notably spend long periods of time staking out their victims without being detected, allowing for extensive recon. In both the ExaGrid case and the Ireland HSE attack, the intruders seem to have spent weeks scoping out the most valuable data before making their presence known with data encryption.
Ransomware attacks have become a national security issue, thanks to incidents such as last month's infection of Colonial Pipeline's IT systems. The pipeline company shut down its fuel operations, which created a small crisis for parts of the U.S. as multiple states panicked over a potential fuel shortage. It was eventually revealed that Colonial paid a $5 million ransom to the DarkSide ransomware crew in hopes of retrieving its data.
The U.S. government responded by setting new guidelines and reporting requirements for companies that suffer network breaches and ransomware attacks.






