
Getty Images
Corvus: Ransomware costs, ransom payments declining
Cyber insurance provider Corvus examined how the cost of ransomware attacks declined over the past year and a half and what it means for different industries moving forward.
Ransomware costs and ransom payments are both trending downward, according to cyber insurance provider Corvus.
In its Risk Insights Index report for the first quarter of 2022, Corvus presented data from the past year and a half of ransomware and the trends that have emerged. While the company did acknowledge some large spikes in the third quarter of 2021, the report shows that overall, ransomware costs are falling.
Corvus' report, which was published this week, includes results from a policyholder survey as well as data from the company's proprietary security scanner. The report found that the overall cost of a ransomware attack fell dramatically from more than $2 million in the third quarter of 2020 to just over $500,000 in the fourth quarter of 2021.
The report's "Ransomware Trends" section presents several key figures, starting with ransomware-related claims by quarter.
Corvus saw two spikes in the number of claims made in March and July 2021. In March the number of policies with ransomware claims was nearly 0.4% of the total number of claims, while in July it was a little over 0.3%.
The report explained that these two increases were due in large part to major threat events that led to downstream breaches and ransomware attacks, specifically the ProxyLogon Microsoft Exchange Server vulnerability and the ransomware attacks stemming from the Kaseya breach.
The rest of the months, however, had much lower rates of policies with ransomware claims, with nine of the 12 months recording rates of 0.2% or lower.
Corvus said that while there were more claims in March and July, the average cost of ransomware attacks was still dropping.
"It's worth noting, however, that the increased frequency of claims we see linked to these events isn't necessarily paired with an increase in severity of claims (losses incurred)," the report said. "In the months we saw spikes in claims related to Microsoft Exchange, average severity of claims declined. Likewise, Kaseya-related claims were also seen to be less severe, with smaller losses incurred. While these vendor-related incidents can increase the frequency of downstream attacks, severity does not always follow with frequency."
Corvus CISO Jason Rebholz said his company has been reacting and adapting to different kinds of cyberthreats.
"When a zero-day vulnerability like ProxyLogon or Log4Shell emerges, Corvus sends all impacted policyholders a proactive alert that provides targeted guidance on how to mitigate the risk," Rebholz told Searchsecurity. "Our underwriting process then adapts to scan each environment and assess whether they are potentially vulnerable to the zero-day. Additional information is also collected to then understand remediation actions that have been taken before potential policyholders are given an insurance policy."
Ransom payments dropping
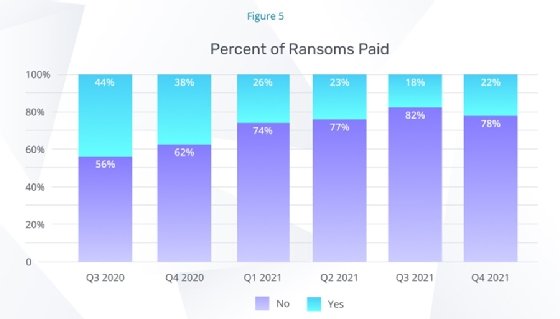
When it came to how victims responded to ransomware attacks, Corvus found that the percentage of ransoms that were paid declined steadily over the last year and a half.
According to the report, 44% of ransoms were paid in Q3 of 2020, but that figure steadily declined to settle in the low 20s, where it finished at 22% for Q4 of 2021.
Rebholz said tighter requirements by insurance carriers like Corvus could be causing the downward trend in the rate that ransoms are paid.
"Organizations pay ransoms when they do not have working backups. Corvus requires its policyholders to implement resilient backup solutions to combat the impact of ransomware," Rebholz said. "Resilient backup solutions shift leverage back to the ransomware victims, who are now better enabled to quickly recover their systems and restore business operations."
Even when ransoms were paid, the Corvus report showed that the average dollar amount was relatively low in 2021. While there was a surge in Q3 with the average payment reaching nearly $300,000, every other quarter sat below $200,000.
Ransomware costs by industry
One of the final trends of the report compared ransomware costs across industries and how those figures have changed since Q3 of 2020. The industries listed are education and social services, healthcare, manufacturing, professional services and "other."
While the ransomware costs for the professional services industries increased, the costs for the education and social services and manufacturing industries have steadily declined.
In Q3 of 2020, the average cost of ransomware in the education and social services industry was over $1,000,000, and it dropped to about $100,000 a year later. In manufacturing, costs fell from around $400,000 on average to less than $100,000.
On the other side, Lauren Winchester, vice president of risk and response at Corvus, told SearchSecurity why professional services are getting hit so hard.
"Professional services firms are regularly targeted by attackers, because, by the nature of their business, they are a point of aggregation -- you hit one, you impact many," Winchester said in an email. "Threat actors are also aware that reputation and trust are paramount in the relationship between professional service firms and their clients, so if attacks threaten that relationship, the malicious actors may be able to extort money (and grab more sensitive data) more easily than from other industries."
For the education and social services sector, Winchester attributed the drop in ransomware costs to policy requirements and improved security controls.
"The education and social services sector was an early target for ransomware attackers, as seen in many headlines about school systems and government agencies being targeted in 2019/2020, but as we can see that's fallen off significantly for Corvus claims, in part because underwriters required better controls in order to offer a policy," Winchester said.
In addition to past trends, the report also looks at potential emerging trends in 2022. For example, Corvus sees the war in Ukraine affecting the ransomware landscape, as well as other factors.
While Corvus said it release a more in-depth review later, some of the factors included a decrease in attacks following the REvil arrests, a decrease in activity from Ukraine-based ransomware actors and infighting between ransomware groups slowing down their overall productivity.





