Researcher unveils smart lock hack for fingerprint theft
An academic researcher demonstrated how IoT smart locks could become tools for attackers to covertly steal fingerprints and potentially access more sensitive personal data.
Consumer smart locks could easily be compromised to allow attackers to steal the fingerprint patterns of targeted users, according to new research.
A paper published this week from James Cook University Singapore described how an attacker could use off-the-shelf hardware and a bit of hacking know-how to covertly harvest fingerprints via a smart lock hack technique called droplock.
The weakness, according to author and senior cybersecurity lecturer Steven Kerrison, lies in the limitations of the hardware used by IoT smart locks. Unlike smartphones or tablets, which store fingerprint details and other biometric data inside encrypted hardware enclaves, low-end IoT devices like commercial smart locks lack dedicated secure storage.
"These devices generally feature less powerful processors, cheaper sensors and do not provide the same level of security as a smartphone," Kerrison wrote in the paper. "This is usually deemed acceptable based on the value of the product itself, or what the sensor is meant to protect."
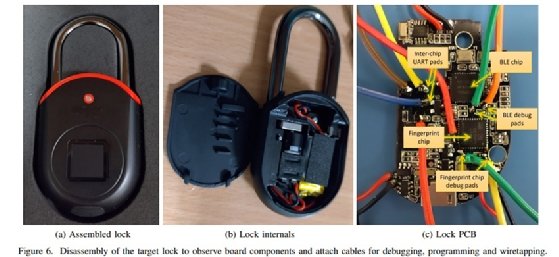
To demonstrate the weakness, Kerrison constructed a proof-of-concept device that could connect with a smart lock over Wi-Fi and -- using either an exploit or an exposed debug interface -- modify the lock's firmware with instructions to collect and upload fingerprint data. Alternatively, the lock could be disassembled and wired directly to the controller via on-board debugging pads.
Either way, the result is a lock that, when activated within range of the attacker's controller, would be able to give data on the target's fingerprint that could then be used against other biometric hardware.
In discussing the findings with TechTarget Editorial, Kerrison noted that any sort of real-world attack would likely be carried out against a predetermined target over a set period of time, rather than a scattershot mass harvesting of credentials.
In that case, the attacker would need to be within somewhat close proximity to the lock, such as standard Bluetooth range, to be able to collect the fingerprints when the lock is activated. Once the print data is collected, it could then be used over time to access other devices that use more robust security measures.
"The attacker needs to have a receiving device quite close to the lock -- just a few meters -- during the attack for the fingerprint to be transferred reliably, so that means the attack has to be more targeted than, say, leaving USB sticks lying around and waiting for people to plug them in to deliver malware into a network," Kerrison explained. "That means a viable attack is more likely to be against a specific victim or group of victims, rather than random, and the assets accessible with the biometrics would have to be worth going to that amount of effort."
While the attacks outlined in the paper were limited to IoT-enabled padlocks, Kerrison believes that the underlying weaknesses in biometrics storage will extend into other devices that protect even more valuable items and data.
"I started with smart padlocks because of their portability and how they lend themselves to the droplock idea," Kerrison said. "However, I am very confident that other devices, such as smart door locks, will be vulnerable. The question then is whether the attack is worth performing with such devices."