5 key enterprise SOC team roles and responsibilities
Review the key players in the 2020 SOC and their specific responsibilities, as well as best practices to ensure effective teamwork for a secure organization.
A security operations center, or SOC, is more than just a physical or virtual location that collects, analyzes and acts upon data. It requires an organizational structure that is not only well funded, but also works harmoniously so it can function effectively to continuously monitor and analyze enterprise security procedures, as well as defend against security breaches and actively isolate and mitigate security risks.
Today's SOCs play a critical role in any enterprise. This has to do with more than cybersecurity alone -- it has to do with the business entirely.
The operations in the security operations center starts with measurement. Everything must be measured. If everything isn't measured, it is probably not even worth doing. Remember, security is a service provider to the business -- for example, onboarding a new tool, creating a metric or dashboarding those metrics. Providing a constant feedback loop that enables forecasting and provides retrospective insight into tools that may not be providing value yet is a financial drain as it goes into the annual renewal budget cycle by default.
5 SOC roles and their responsibilities
There are five key technical roles in a well-run SOC: incident responder, security investigator, advanced security analyst, SOC manager and security engineer/architect.
1. Incident responder
As the SOC's first responder, the incident responder is responsible for configuring and monitoring security tools, as well as using these tools to identify threats. The job, which maps to the Tier 1 level in the SOC, involves looking into the hundreds of alerts received daily to triage, classify and prioritize them. Once this is done, the information is ultimately handed off to the security investigator.
2. Security investigator
Using sophisticated allies, such as threat intelligence, the security investigator's job is to identify affected hosts and devices and then evaluate running and terminated processes. This usually also involves deeper investigation to identify sources of attack, lateral movement analysis, methodologies used and duration of residence of the attack vector in the environment. Security investigators, which map to Tier 2, are also responsible for crafting and deploying mitigation and eradication strategies.
3. Advanced security analyst
The advanced security analyst, who is in Tier 3, is the most experienced of the SOC crew. These analysts usually work in the background to identify unknown vulnerabilities, review past threats and mitigations, and assess vendor health and product vulnerabilities. They make recommendations to change products, processes and tools.
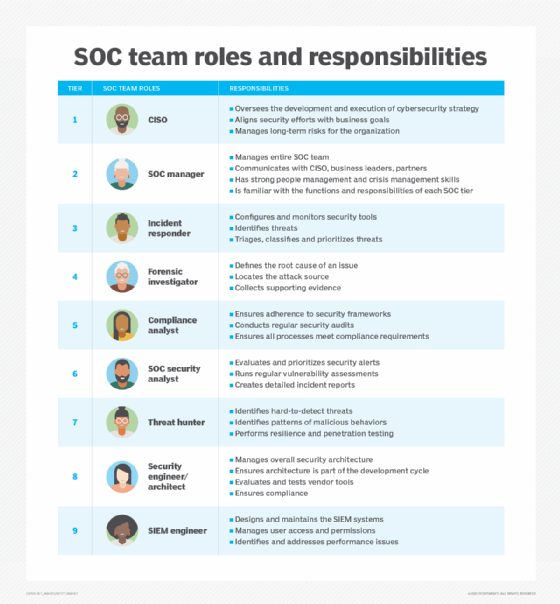
4. SOC manager
This role encompasses managing the entire SOC team. Referred to as Tier 4, SOC managers have an intimate understanding of all SOC tiers. In addition, communication with the CISO, other business leaders, partners, and audit and compliance heads is mandatory. Strong people management and crisis management skills are also needed.
5. Security engineer/architect
Security engineers and architects are responsible for the enterprise's overall security architecture and ensure this architecture is part of the development cycle. They evaluate and test monitoring and analysis tools from vendors. Sometimes, this role also includes security compliance, which involves documenting, adhering to and constantly updating security practices against industry and internal frameworks.
Depending on size and vertical, some SOCs may have additional team members, such as compliance auditors, threat hunters or forensic investigators.
3 best practices for a successful SOC teams
The SOC will continue to play an ever-critical part in enterprise cybersecurity strategies. Creating and appointing the appropriate roles and investing in -- as well as jettisoning -- tools and processes are of the utmost importance. SOC teams must constantly be willing to reevaluate priorities and best practices to create and maintain a secure company.
To ensure the different SOC roles operate in cohesion and with maximum efficiency, there are three best practices that should be followed.
1. Automate, automate, automate
With the explosion of devices and the need for metric collection to identify lurking threats, the days of an incident responder looking at logs manually is long gone. AI-based tools help analysts identify patterns and find high-priority issues. This automation enables the SOC roles to operate efficiently and enables efficient handover from one tier to another. Automation also helps make reporting and documentation -- a common time sink for SOCs -- more efficient.
2. Go beyond the four walls -- or virtual walls -- of a SOC
By pairing DevOps engineers in the enterprise with incident responders and security investigators, for example, both can learn from each other. DevOps can share their deep IT expertise and state-of-the-art software craft to help educate their SOC peers. In return, DevOps engineers can learn about threat identification, response and mitigation from SOC team members, which can help them build more secure products.
3. Consider outsourcing
Some or all SOC operations can be outsourced to a third party, especially for industries where hiring and retaining cybersecurity talent is an ongoing challenge. Given the influx of IoT, hyperinstrumentation and sophisticated forms of newer attacks coupled with the long tail of existing threats, the need for a SOC efficient enough to predict, detect, prevent and triage attacks is going to be paramount. However, depending on the industry -- hyperregulated ones, such as finance, or national security-related ones, such as defense, for instance -- outsourcing may not be feasible.








