Windows Sysinternals
What is Windows Sysinternals?
Windows Sysinternals is a collection of 70 freeware utilities that Microsoft offers IT administrators and developers to help them monitor, manage, diagnose and troubleshoot Windows systems and their applications. Microsoft has also started porting some of the Sysinternals tools to the Linux platform, although the number of tools is still limited.
Each Sysinternals utility is an executable file that users can run on demand without needing to install a program on their systems. Microsoft provides utilities for x86, x64 and Arm64 Windows platforms, as well as for systems running Nano Server. Users have several options for acquiring and running these tools:
- Download the individual utilities or one of the full suites from the Microsoft Sysinternals site or from the Sysinternals Live site.
- Run the utilities directly from the Sysinternals Live site without downloading the files. For example, you can use the following command to run the AccessChk utility at a command prompt: \\live.sysinternals.com\tools\handle.
- Download the suite from the Microsoft Store. The suite is installed as an MSIX bundle that includes separate packages for x86, x64 and Arm64 systems.
- For the ported Linux tools, download the source code from GitHub. Microsoft has ported only a few Sysinternals tools to Linux.
Sysinternals generally doesn't include utilities that can't be used for troubleshooting, such as BlueScreen Screen Saver. Also, some of the original utilities are no longer available as standalone tools because their functionality has been incorporated into other Sysinternals tools. For example, the features in RegMon and FileMon were rolled into the Process Monitor utility.
Microsoft also offers Sysinternals tools for Nano Server, a lightweight version of Windows Server. Because Nano Server does not run 32-bit applications, Microsoft developed 64-bit versions of more than 40 Sysinternals utilities so they'd be compatible with Nano Server. The utilities, which include "64" at the end of their file names, also work with other 64-bit Windows systems.
Sysinternals categories
Microsoft divides the Sysinternals utilities into the following six categories:
- File and disk. This category provides utilities that monitor file usage and disk status. For example, it includes DiskMon for capturing hard disk activity, SDelete for securely overwriting sensitive files and Disk Usage for viewing disk usage by directory.
- Networking. This category offers utilities for troubleshooting and monitoring connections on desktop and server systems. Two of the more popular tools are TCPView, which checks TCP and User Datagram Protocol (UDP) endpoints, and PsTools, a set of command-line utilities for listing and running processes on local and remote systems.
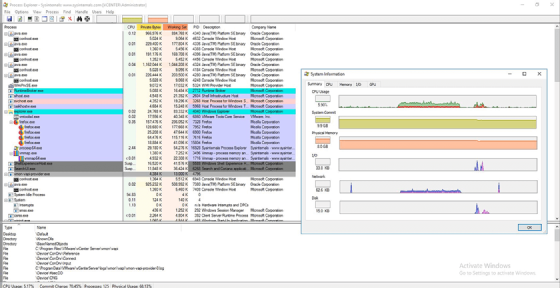
- Process. This category includes utilities for monitoring and troubleshooting running applications. One popular utility is Process Explorer, which monitors the files, registry keys and other objects that a process has open. Another popular tool is Process Monitor, a tool that shows real-time activity in the file system, registry and processes.
- Security. This category offers security-based utilities such as LogonSessions, which lists the active logon sessions, and Autoruns, which shows the applications that start automatically when the system boots.
- System information. This category includes utilities that display general information about a workstation or server. For example, the Coreinfo utility shows the mappings between logical and physical processors, and the Handle utility lists which files are open by which processes.
- Miscellaneous. Utilities in this category do not fit into other categories and have limited diagnostic or troubleshooting capabilities. One of the more popular tools is BgInfo, which creates a background image that shows key features of the system's configuration, such as the IP address and computer name.
History of Sysinternals
The original Sysinternals tools were developed by Mark Russinovich and Bryce Cogswell. In 1996, they launched a website named NTInternals, which hosted the Sysinternals freeware utilities and related articles. The first utility they released, NTFSDOS, enabled a Microsoft Disk Operating System machine to read New Technology (NT) File System volumes.
In the same year, Russinovich and Cogswell founded Winternals, a company whose goal was to develop advanced Windows technologies. Out of this effort came a range of software products, including Protection Manager, Defrag Manager, Administrator's Pak and Recovery Manager. The company also continued to refine the Sysinternals tools.
In 1998, Russinovich and Cogswell renamed the NTInternals site to Sysinternals. This came after Microsoft's legal department requested that Winternals change the name, citing the similarity between the name NTInternals and the Windows NT operating system (OS).
In July 2006, Microsoft acquired Winternals and Sysinternals, and Cogswell and Russinovich joined the company. Cogswell retired from Microsoft in 2010 and no longer contributes to the Sysinternals tools. Russinovich -- currently chief technology officer of the Microsoft Azure cloud platform -- continues to participate in Sysinternals.
Microsoft still owns the Sysinternals utilities and offers them for free through the Microsoft site. The company does not limit the number of times that someone can download or use the software. However, Microsoft does not offer any type of distribution license, which means that third-party entities are not permitted to distribute the utilities in their software or through their websites. Microsoft currently has no plans to remove or change the availability of the Sysinternals tools.

RootkitRevealer uncovers hidden tools
In 2005, Sysinternals received widespread exposure when Russinovich wrote a blog that explained how he found a rootkit on one of his computers when testing the RootkitRevealer tool in Sysinternals. The utility -- since discontinued -- produced a report of all the files and registry entries hidden from the system's application programming interfaces.
RootkitRevealer detected a rootkit that originated from a Sony BMG audio compact disc, which installed a digital rights management (DRM) program that modified the OS to prevent a user from copying the CD.
Bowing to public pressure after the blog's release, Sony BMG recalled products with the rootkit and released an uninstaller to remove it. The company also settled class-action lawsuits related to the rootkit with the Federal Trade Commission, several states and the Electronic Frontier Foundation.
Additional reference guide available
Russinovich and Aaron Margosis co-authored a Sysinternals companion book called Troubleshooting with the Windows Sysinternals Tools, which provides in-depth details about working with the various utilities, along with tips and tricks for using them.
Use the Sysinternals Sysmon tool to check DNS queries and these Windows troubleshooting tools to improve virtual machine performance. Check out IT automation scripts that take little effort and save a lot of work. Learn about PowerShell and how to use it. Explore 16 PowerShell commands for network troubleshooting and top PowerShell commands you must know in general.







