
zagandesign - Fotolia
WUfB vs. WSUS: Which handles Windows updates better?
Trying to get a handle on Windows updates can frustrate even the most seasoned administrators. Which of these two patch management tools fit best in your environment?
Windows Server Update Services has been around for a long time and is the tool many administrators rely on to manage Windows updates. Windows Update for Business is a relatively new technology that does the same job but takes a different approach. Is one a better fit for your organization than the other?
Microsoft released Windows Server Update Services (WSUS) in 2005 to supersede Software Update Services (SUS). WSUS is still fully supported and many companies rely on it. WSUS helps maintain order: Instead of having all the Windows clients go to the internet and download the updates, you have one or more WSUS servers that centralize the job and give you control on which updates to release to the clients.
System Center Configuration Manager (SCCM) -- also known as ConfigMgr and recently rebranded as Microsoft Endpoint Configuration Manager -- came along and offered even more control over Windows updates. SCCM ingests the updates downloaded via WSUS and uses its own client to deploy them, using the workflow and rules defined in ConfigMgr.
WSUS helps automate the busywork of Windows patching
For a long time, many admins used WSUS in a mostly automated fashion. They either allowed all updates as they arrived or they allowed the critical and security updates straight away and held off on the rest for testing. Some admins would read up on every single update, deploy to a test group and then roll out to the main fleet. Later, they would push the patches to legacy and more delicate devices. This is a manual and time-intensive process to follow, especially at a time when Microsoft releases several updates at different times of the month.
IT admins will occasionally get bit by buggy Microsoft updates on Windows devices. These issues range from minor annoyances to the dreaded blue screen of death. While we're seeing better stability from the monthly updates, administrators have less control over the patching process. Microsoft switched to a cumulative update model in late 2016 that removed the ability to pick and choose which updates to install by releasing multiple patches into a single large update.
To further complicate the update process, Microsoft releases two feature updates for Windows 10 each year -- one in the spring and another in the fall -- that introduce new features. These feature updates also include all preceding quality updates, which are the monthly security updates and bug corrections.
How Windows Update for Business works
Windows Update for Business (WUfB) is just a few registry settings on a PC to provide a few extra rules for the client to connect to the public Windows Update service.
You control those registry settings with a management tool, such as Intune or Group Policy, or through other methods to modify registry settings, including a script. The controls WUfB provides are fairly minimal, but that might be enough for some administrators who prefer not to handle Windows Updates on a regular basis.
WUfB is free for managing all premium editions of Windows 10.
Run the WUfB vs. WSUS comparison
When it comes to patching Windows machines, should you stick with WSUS -- and Endpoint Manager for updates, which requires WSUS -- or should you move to WUfB?
If you're trying to go to the cloud as much as possible -- that includes using cloud-based management tools such as Intune -- then the choice is WUfB, unless you decide to run WSUS on an Azure VM. Let's explore both sides and explore why you may want to stick with your current WSUS setup or decide to jump to WUfB and shut down those servers.
What's possible in WUfB?
WUfB has four main settings in Group Policy. Let's take a closer look at each setting and explain what each offers to control the deployment of updates. For more details about working with WUfB and Group Policy, take a look at Microsoft's documentation.
Select when preview builds and feature updates are received
These settings select one of four update rings for the Windows 10 clients:
- Preview Build - Fast. This setting delivers builds with the latest features not yet available to the public with the option to report bugs and request improvements to Microsoft.
- Preview Build - Slow. This setting delivers builds with the latest features at a slower speed than the Fast ring and includes fixes to issues in earlier builds.
- Release Preview. This setting delivers official Windows builds before they are publicly available.
- Semi-Annual Channel. This setting releases Windows builds when they are available to the public.
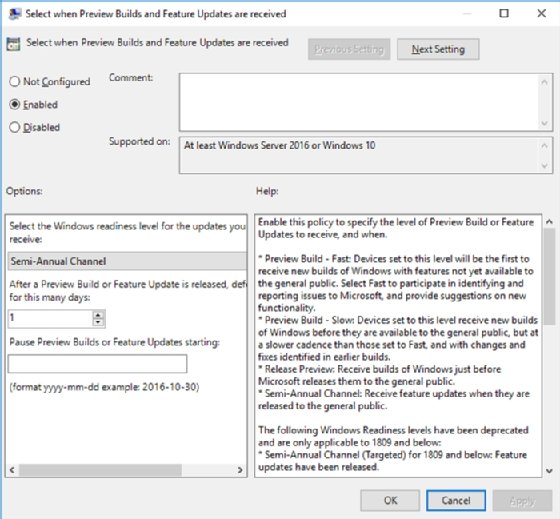
You have the option to defer a feature update for up to one year. This practice can help your organization avoid issues with the build by not being on the cutting edge and letting other organizations find bugs and report them to Microsoft. Pushing back the release date to your clients by several days could be just what you need to avoid unnecessary troubleshooting work until Microsoft rolls out fixes.
Another option allows you to pause the deployment of preview builds. You enter a date and, for 35 days from that date, no clients will install preview builds or feature updates. This can be handy when a bad update has been released and you want to put a freeze on it. By the time the 35 days are up, Microsoft should have sorted things out and clients can try to perform the install again, unless you have changed the date.
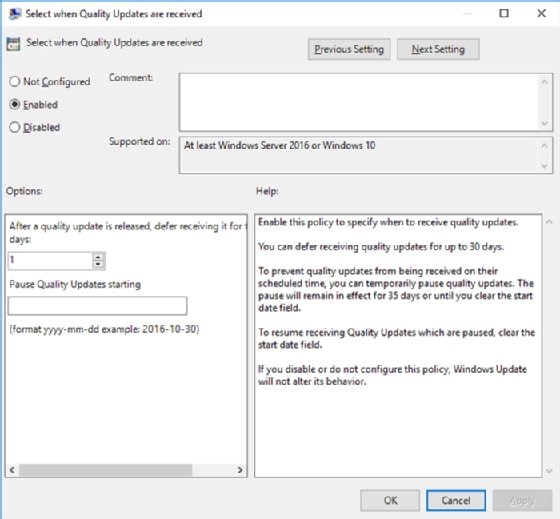
Select when clients receive quality updates
Just like the previous option but related to quality updates, this section offers the option to defer the clients from receiving a quality update for up to 30 days before the clients download and install the update. You can also choose to put a start date to pause the delivery of quality updates for 35 days or until you clear the start date.
Manage preview builds
This menu gives you the option to disable or enable preview builds with a few more granular controls.
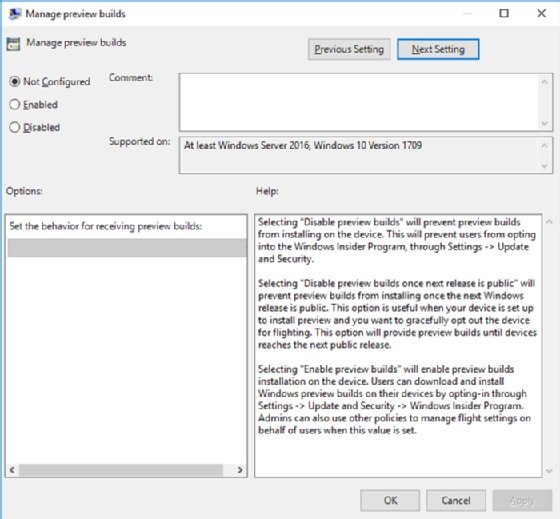
You can stop users from entering the Windows Insider program when you select disable preview builds.
You can choose to disable preview builds when Microsoft releases a public build. This is a nice way to wind back from an already-allowed preview build. Some people may leave this off entirely or allow it for certain IT staff who may need early access to Windows 10 preview builds for testing purposes.
The Enabled option gives users the rights to install preview builds on their machines.
Select the target feature update version
In this section, you choose a target for the feature update version, such as 1909, 2004 or 2010 -- also known as 20H2 -- to upgrade the client machine to a newer, major Windows 10 release. If you need to control this delivery, then you can enter a target version, which is the only version of Windows 10 that will install. This means if the client is on 1903 and the WUfB feature update setting is 1909, then the client will not get newer versions if they are available via Windows Updates.
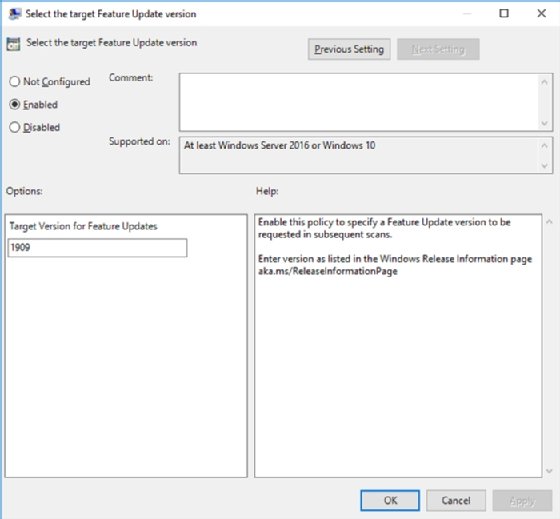
From these settings, you can configure different policies for different PCs, such as setting up pilot PCs that get updates first to be the canary in the coal mine and catch any problems introduced by an update. You can also control when PCs get upgraded to the next feature update and build another pilot group before going further with upgrades to other clients.
WUfB vs. WSUS: Difference with the update process
Windows 10 has a feature called delivery optimization that gives PCs on the local network a way to share updates. There used to be a strong argument for WSUS, which downloads all the updates once and then distributes them locally, saving a lot of internet bandwidth. Delivery optimization approximates this feature if you use WUfB. You can check how well this feature performs on each PC under the delivery optimization's activity monitor section, which shows statistics for sharing and receiving updates via the internet versus PCs on the local network.
One other feature that Microsoft has via Windows Updates is safeguard holds. If Microsoft detects an issue with a new feature update, it places a hold to block the deployment of the feature update until it can resolve the issue. For WUfB customers, this is seamless. However, WSUS customers need to be aware of these outstanding issues and make the determination to deploy the update or prevent it. Microsoft often knows about these problems before you do, so it's up to you if you want this level of control or if you want Microsoft to handle it.
For some organizations, WSUS might win out
WSUS has a few tricks that WUfB doesn't. For example, it's relatively easy to set an update to uninstall if the version supports it, which makes it simple to remove a troublesome update. This isn't possible in WUfB; instead, you need to use PowerShell to remove the offending update, then trigger it across your fleet.
WSUS also prevents computers from connecting over the internet to Microsoft for updates. For a bandwidth-sensitive site, this gives you more reliability by using a single download path for updates on a schedule you configure to avoid any interruptions.
If you're an admin who still wants or needs to go over every update in detail and release when you're ready, WSUS is for you. With WUfB, your control is limited; you can hold off on updates but not stop them outright like you can with WSUS.
This level of control comes at a price where you need a server or even multiple server workloads running WSUS, which adds to your administrative overhead, whereas WUfB is a series of settings.
In this WUfB vs. WSUS exercise, there is no right or wrong choice, because each patch management tool serves a different purpose. WUfB aligns closely with the deployment options of Office 365 updates and its rings, so if you're already using or looking at this technology, what WUfB brings won't be new to you. You can even have WSUS and WUfB running concurrently with a few registry settings. If you want to try WUfB in a pilot group for a few months, it is easy to set up with very little work.
WUfB offers a lower touch management option that comes without resources required and at no cost. You can set updates to trickle out as slowly as you like. WSUS will still provide that greater control -- and for those still wanting to use Endpoint Manager, it's a necessity -- around update deployment and management.








