What is IoT security?
IoT security is the technology segment focused on safeguarding connected devices and networks in the internet of things. IoT involves adding internet connectivity to a system of interrelated computing devices, mechanical and digital machines, objects, animals and people.
Each thing has a unique identifier and the ability to automatically transfer data over a network. However, enabling devices to connect to the internet opens them up to serious vulnerabilities if they aren't properly protected.
The term IoT is broad, and as this technology evolves, the term continues to broaden. From watches to thermostats to video game consoles, nearly every technological device can interact with the internet, or other devices, in some capacity.
IoT security is a significant aspect of IoT and has resulted in a variety of methodologies falling under that umbrella. Application programming interface (API) security, public key infrastructure (PKI) authentication and network perimeter security are just a few of the methods IT organizations use to combat the growing threat of cybercrime and cyberterrorism rooted in vulnerable IoT devices.
This is even more important for consumer IoT ecosystems, where users typically aren't cybersecurity experts and can be more vulnerable to cyberattacks. When investing in IoT systems and devices, such as in a smart home, consumers must make a concerted effort to implement robust security measures to prevent cybersecurity breaches and to mitigate attacks if they occur.
Why is IoT security important?
Due to the unique characteristics of IoT devices and the vast amount of data they handle, a constant threat of cyberattacks exists. Numerous examples of high-profile incidents, where a common IoT device was used to infiltrate and attack a larger network, demonstrate the need for more comprehensive IoT security. The following are key reasons why IoT security is important:
- Attack surface. As more IoT systems and devices connect to the internet, the potential surface area cybercriminals can attack continues to grow, creating more opportunities for breaches and disruptions.
- Critical infrastructures. IoT technology enhances functionality and the ability to learn and improve infrastructure functions. As a result, it's being used more in critical infrastructure, such as power grids and water, sewer and transportation systems -- increasing the likelihood of security breaches.
- Data protection and privacy. It's not uncommon for IoT systems and devices to capture, process and transmit sensitive data, such as personally identifiable information (PII). This makes them high-value targets for cybercriminals.
- Compliance. IoT systems and devices support various compliance requirements, particularly data privacy ones.
- Business impact. Cyberattacks impairing mission-critical IoT assets could result in loss of productivity, financial damage, reputational damage and legal liability.
The ever-looming possibility of vulnerabilities, data breaches, ransomware attacks and other risks associated with IoT device use underscores the need for strong IoT security. IoT security is vital for enterprises, as it includes a range of techniques, strategies, protocols and actions that aim to mitigate the increasing IoT vulnerabilities of modern businesses. It is also essential for consumer IoT applications, such as smart homes.
Examples of IoT security threats
The more ways devices connect to each other, the more opportunities threat actors have to intercept them. HTTP and APIs are just two of the channels IoT devices rely on that hackers can intercept.
The IoT umbrella doesn't only include internet-based devices, either. Appliances that use Bluetooth technology also count as IoT devices and require IoT security. The following are examples of IoT security threats and vulnerabilities:
- Inadequate authentication. Without strong authentication measures, especially with passwords and role-based authentication, IoT devices and systems are vulnerable to malware attacks. Multifactor authentication (MFA) helps alleviate device vulnerability.
- Lack of encryption. IoT systems and devices must have security that prevents the processing and transmission of sensitive data formatted as plain text. Data at rest and in motion must be encrypted.
- Lack of patching and updating. IoT systems and devices that use older firmware and application code increase system vulnerability. Users must keep security software current with vendor updates and patches.
- Unsafe access controls. Strong passwords and MFA strengthen access controls. Additional steps, such as properly configuring access permissions and using role-based authentication, also strengthen access security.
- Risky network perimeter. IoT systems and devices must have secure network access, such as strong firewalls. Networks should be checked to identify unsafe ports and unnecessary services.
- Cyberattacks using artificial intelligence. While AI is an important resource for IoT security, hackers can also use it to automate and scale attacks on IoT ecosystems. AI-based cybersecurity systems should be considered as part of a defense-in-depth security structure.
- Distributed-denial-of-service, spoofing and botnet attacks. DDoS attacks send out a flood of data that overwhelms a device, rendering it unstable or shutting it down. Spoofing attacks impersonate legitimate IoT devices, sending false data or commands. Compromised IoT systems can be turned into botnets that can launch DDoS attacks.
- Replayed data. Cybercriminals can hack into a system and capture legitimate data packets that can be stored and then replayed to launch unauthorized access. This attack is found in smart locks and industrial controls. The anti-replay protocol addresses this issue.
- Resource limitations. Not all IoT devices have the computing power to integrate sophisticated firewalls or antivirus software. Users must evaluate prospective purchases to ensure that the product can deliver adequate cybersecurity protection.
- Inadequate physical device security. IoT devices and system units should be located in physically secure areas, as opposed to public or remote locations. Hackers and vandals can damage devices, steal data and install malware.
How to protect IoT systems and devices
Enterprises can use the following tools and technologies to improve their data protection protocols and security posture:
- Introduce IoT security during development. Most IoT security risks and issues can be overcome with better preparation, particularly during the research and development process at the start of any consumer, enterprise or industrial IoT (IIoT) device development. Enabling security by default is critical, along with providing the most recent operating systems and using secure hardware.
- Use PKI and digital certificates. PKI can secure client-server connections between multiple networked devices. Using a two-key asymmetric cryptosystem, PKI facilitates the encryption and decryption of private messages and interactions using digital certificates. These systems help to protect the cleartext information that users input into websites to complete private transactions. E-commerce wouldn't be able to operate without the security of PKI.
- Ensure network security. Networks provide a huge opportunity for threat actors to remotely control IoT devices. Because networks involve both digital and physical components, on-premises IoT security should address both types of access points. Protecting an IoT network includes ensuring port security, disabling port forwarding and never opening ports when not needed; using antimalware, firewalls, intrusion detection systems and intrusion prevention systems; blocking unauthorized Internet Protocol (IP) addresses; and ensuring systems are patched and up to date.
- Prioritize API security. APIs are the backbone of most sophisticated websites. For example, they let travel agencies aggregate flight information from multiple airlines into one location. Unfortunately, hackers can compromise these channels of communication, making API security necessary for protecting the integrity of data being sent from IoT devices to back-end systems and ensuring only authorized devices, developers and apps communicate with APIs. T-Mobile's 2018 data breach exposed the consequences of poor API security: Due to a leaky API, the mobile giant exposed the personal data of more than 2 million customers, including billing ZIP codes, phone numbers and account numbers.
Other IoT security methods and best practices
The following is a list of activities that should be part of every organization's IoT security efforts:
- Network access control. NAC can help identify and inventory IoT devices connecting to a network. This provides a baseline for tracking and monitoring devices.
- Segmentation. IoT devices that need to connect directly to the internet should be segmented into their own networks and have restricted access to the enterprise network. Network segments should monitor for anomalous activity, taking action if an issue is detected.
- Security gateways. Acting as an intermediary between IoT devices and the network, security gateways have more processing power, memory and capabilities than the IoT devices themselves, which lets them add features such as firewalls to ensure hackers can't gain access to the IoT devices they connect.
- Patch management and continuous software updates. It's critical to provide a way to update devices and software either over network connections or through automation. Having a coordinated disclosure of vulnerabilities is also important for updating devices as soon as possible. Consider end-of-life strategies as well.
- Training. IoT and operational system security are new to many existing security teams. Security staff must keep up to date with new or unknown systems, learn new architectures and programming languages, and be ready for new security challenges. C-level and cybersecurity teams should receive regular cybersecurity training to keep up with modern threats and security measures.
- Team integration. Along with training, integrating disparate and regularly siloed teams can be useful. For example, having programming developers work with security specialists can help ensure the proper controls are added to devices during the development phase.
- Consumer education. Consumers must be made aware of the dangers of IoT systems and provided steps to stay secure, such as updating default credentials and applying software updates. Consumers can also play a role in requiring device manufacturers to create secure devices by refusing to use those that don't meet high-security standards.
- Enforcement and automation of zero-trust policies. The zero-trust model dictates that all users -- whether inside or outside the organization's network -- must be verified, authorized and continually evaluated for security configuration and posture before being given access to applications and data. Automating zero-trust policies and enforcing them can mitigate security threats against IoT devices.
- Multifactor authentication. MFA adds an extra layer of security by requiring more than one form of identification when requesting access to a device or network. By enforcing MFA policies, both enterprises and home users can improve the security of IoT devices.
- Machine learning. ML technology can be used to secure IoT devices by automating the management and scanning of devices throughout the entire network. Since every device connected to the network is scanned, it stops assaults automatically before IT teams are alerted.
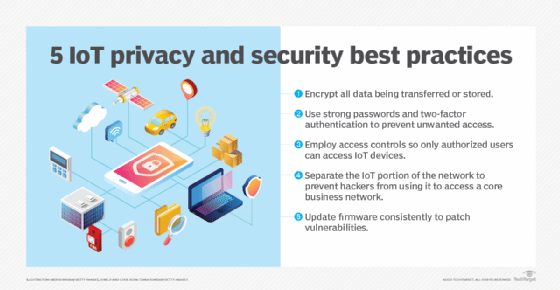
The following is a brief list of IoT security best practices:
- Revise and replace outdated security credentials with strong passwords and MFA.
- Update and patch firmware and applications as often as possible, following vendor guidelines; consider using automatic updates.
- Monitor device logs to detect suspicious activity, such as sign-ins, access to various resources and changes in security policies.
- Enable data encryption for data at rest and in transit. This is especially important for third-party services, such as the cloud.
- Keep an accurate and current device inventory. It's essential to keep track of authorized devices and identify suspicious ones.
- Test IoT device security using penetration tests and other predictive analyses. This helps identify vulnerabilities and improve security.
- Build security into IoT ecosystems and institute a schedule of regular system reviews and tests.
- Establish a culture of security for IoT ecosystems, using strong passwords that are regularly changed.
- Provide security awareness and training to users.
Which IoT devices are most vulnerable to security breaches?
Because they're connected to the internet, all IoT systems and devices face the risk of attack. The following is a list of systems and devices typically found in these ecosystems.
Consumer environments and smart homes
- Smart watches.
- Smart door locks.
- Smart thermostats.
- Smart garage doors.
- Home security systems.
- Lighting systems.
- Smart appliances, such as stoves, refrigerators and coffee makers.
- Smart baby monitors.
- Smart pet tracking.
Commercial ecosystems
- Building access control systems.
- Smart building management systems.
- Smart elevators.
- Smart monitoring systems, using CCTV and motion detectors.
- Smart heating, ventilation and cooling systems.
- Smart door locking systems.
- Specialized medical equipment.
- Video cameras.
- Smart printers.
- Various sensors.
Which industries are most vulnerable to IoT security threats?
IoT security hacks can happen anywhere -- from a smart home to a manufacturing plant to a connected car. The severity of the attack depends on the system, the data collected and the information it contains.
For example, an attack disabling the brakes of a connected car or hacking a connected health device, such as an insulin pump, can be life-threatening. Likewise, an attack on a refrigeration system housing medicine that's monitored by an IoT system can ruin the viability of a medication if temperatures fluctuate. Similarly, an attack on critical infrastructure, such as an oil well, energy grid or water supply, can be disastrous.
Other attacks, however, can't be underestimated. For example, an attack against smart door locks could potentially let a burglar enter a home. Or, in other security breaches, an attacker could pass malware through a connected system to scrape PII, wreaking havoc for those affected.
Generally speaking, industries that are most vulnerable to IoT security threats include, but aren't limited to, the following:
- Retail companies.
- Trucking industry.
- Consumer electronics.
- Utilities and critical infrastructure.
- Healthcare.
- Education.
- Government agencies.
- Financial institutions.
- Energy and utility companies.
Notable IoT security breaches and IoT hacks
Security experts have warned of the potential risk of large numbers of insecure devices connected to the internet since the IoT concept first originated in the late 1990s. Many attacks subsequently have made headlines, including refrigerators and TVs being used to send spam, as well as hackers infiltrating baby monitors and talking to children. Many IoT hacks don't target the devices themselves; rather, they use IoT devices as an entry point into the larger network.
The following are some notable IoT security incidents:
- Stuxnet. In 2010, researchers revealed that the Stuxnet virus was used to physically damage Iranian centrifuges, with attacks starting in 2006 but the primary attack occurring in 2009. Considered one of the earliest examples of an IoT attack, Stuxnet targeted supervisory control and data acquisition systems in industrial control systems, using malware to infect instructions sent by programmable logic controllers. Attacks on industrial networks have continued, with malware such as CrashOverride -- also known as Industroyer -- Triton and VPNFilter targeting vulnerable operational technology and IIoT systems.
- TRENDnet. In 2012, a backdoor coding error permitted public access to live feeds from home IP-based streaming security cameras. The Federal Trade Commission forced the company to improve its webcam security practices.
- IoT botnet. In December 2013, a researcher at enterprise security firm Proofpoint Inc. discovered the first IoT botnet. According to the researcher, more than 25% of the botnet was made up of devices other than computers, including smart TVs, baby monitors and household appliances.
- Jeep. In 2015, security researchers Charlie Miller and Chris Valasek executed a wireless hack on a Jeep, changing the radio station on the car's media center, turning its windshield wipers and air conditioner on, and stopping the accelerator from working. They said they could also kill the engine, engage the brakes and disable the brakes altogether. Miller and Valasek were able to infiltrate the car's network through Chrysler's in-vehicle connectivity system, Uconnect.
- Mirai. This is one of the largest IoT botnets to date. It first attacked journalist Brian Krebs' website and French web host OVH in September 2016; the attacks clocked in at 630 gigabits per second and 1.1 terabits per second, respectively. The following month, domain name system service provider Dyn's network was targeted, making a number of websites, including Amazon, Netflix, Twitter and The New York Times, unavailable for hours. The attacks infiltrated the network through consumer IoT devices, including IP cameras and routers. A number of Mirai variants have since emerged, including Hajime, Hide 'N Seek, Masuta, PureMasuta, Wicked and Okiru.
- St. Jude. In a January 2017 notice, the Food and Drug Administration warned that the embedded systems in radio frequency-enabled St. Jude Medical implantable cardiac devices -- including pacemakers, defibrillators and resynchronization devices -- could be vulnerable to security intrusions and attacks.
- Ring. Hackers gained access to Ring home security system cameras in 2019 using old and weak passwords.
- Big-IP boxes. In July 2020, Trend Micro discovered an IoT Mirai botnet downloader that was adaptable to new malware variants, which would help deliver malicious payloads to exposed Big-IP boxes. The samples found also exploited recently disclosed or unpatched vulnerabilities in common IoT devices and software.
- Verkada. In March 2021, security camera startup Verkada had 150,000 of its live camera feeds hacked by a group of Swiss hackers. These cameras monitored activity inside schools, prisons, hospitals and private company facilities, such as Tesla.
- Remote code execution vulnerabilities. In late 2022, hackers began exploiting a series of 13 IoT vulnerabilities related to remote code execution. They installed a modified version of the Mirai malware on compromised devices, giving them unauthorized control over the affected systems.
- Akuvox. In March 2023, Akuvox's smart intercom was found to have zero-day flaws that allowed remote eavesdropping and surveillance.
- Trusted Platform Module. Also in March 2023, vulnerabilities related to buffer overflow were found in the Trusted Platform Module 2.0 protocol, putting billions of IoT devices at risk.
IoT security standards and legislation
Many IoT security frameworks and standards have been developed. These provide tools and checklists to help companies create and deploy secure IoT devices. The following are some primary IoT security standards, regulations and frameworks.
International standards
- International Organization for Standardization (ISO)/International Electrotechnical Commission (IEC) 27400:2022. This standard provides guidance on IoT security and privacy risks, principles and controls.
- ISO/IEC 27001:2022. This is a global standard for information security management systems that can be used in IoT environments.
- IEC 62443 series. These standards address cybersecurity for industrial automation and control systems, especially for industrial IoT.
- European Telecommunications Standards Institute EN 303 645:2024. This European standard covers consumer IoT device security.
European Union regulations
- Cyber Resilience Act. This regulation addresses the implementation of cybersecurity on AI-based products.
- Radio Equipment Directive. This radio equipment regulatory framework addresses cybersecurity safeguards for wireless devices.
- General Data Protection Regulation. Commonly known as GDPR, this regulation protects the collection and processing of personal data on IoT devices.
- Network and Information Security Directive 2. This directive, also known as NIS2, provides guidance on cybersecurity for numerous digital systems, including IoT.
U.S. regulations
- Cyber Trust Mark. This is a voluntary labeling program developed by the Federal Communications Commission to help consumers identify secure IoT products.
- IoT Cybersecurity Improvement Act of 2020. This legislation establishes cybersecurity standards for IoT devices.
- Executive Order 14028. This 2021 executive order, "Improving the Nation's Cybersecurity," advocated for stronger cybersecurity standards across federal systems, including IoT.
- California IoT Cybersecurity Law SB-327. This law requires manufacturers to implement reasonable security features in consumer IoT devices.
Security frameworks
- National Institute for Standards and Technology SP 800-213 (2021). This Special Publication, IoT Device Cybersecurity Guidance for the Federal Government, provides detailed guidance for security on IoT devices.
- IoT Security Assurance Framework. This framework, also known as IoTSF, provides guidance for ensuring the security of IoT devices and systems throughout their lifecycle.
- Open Worldwide Application Security Project IoT Top 10. The nonprofit foundation OWASP lists security risks associated with IoT development.
- Industrial Internet Security Framework. This provides guidance on risks and security for IIoT systems.
IoT endpoints have emerged as major targets for cybercriminals. Discover the top IoT security threats and how to prioritize them.






