Hybrid cloud connectivity best practices and considerations
Private and public clouds stress networks in different ways and don't always play well together. Here's what to know to set up a cost-effective hybrid cloud network architecture.
Whether it's a LAN that supports a private or public cloud or the vast global WAN that supports a hybrid cloud, network connectivity moves the vast amounts of data that enable cloud resources and services. Cloud architects must evaluate the capabilities, configurations and corresponding costs of LAN and WAN connectivity to ensure adequate, reliable and cost-effective hybrid cloud strategy and deployment.
Key elements of hybrid cloud connectivity
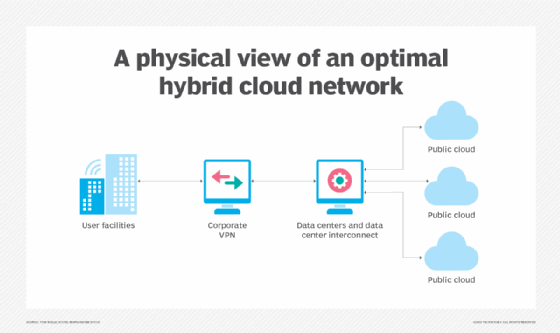
There are three principal areas of concern in hybrid cloud connectivity: LAN, WAN and the public cloud provider.
LAN
An existing private corporate network is rarely enough to support a private cloud over the long term. Cloud resources must be available on demand, but IT teams can't easily predict usage patterns and load levels in a private (in-house) cloud model. LAN network bottlenecks can emerge as users carve out resources.
The good news is that a private cloud rarely impacts the entire LAN. Rather, the LAN infrastructure associated with private cloud servers, storage and software stack is most impacted. From a physical standpoint, the portion of a LAN committed to a private cloud must be evaluated and upgraded to support scalability and flexibility. That portion might include deploying redundant switches, multiple WAN gateways and ample LAN bandwidth to handle peak workload demands. Strategic traffic monitoring should help identify bottlenecks and justify upgrades or architectural changes to the LAN -- all well within the control of the organization that owns its private cloud.
WAN
The easiest way to connect a private cloud to one or more public clouds is through the internet. Although ISPs offer tremendous bandwidth at manageable prices, the open internet is subject to disruptions and congestion. In addition, it can expose unencrypted network traffic to security threats.
To address these issues, keep an application and its data in the same place, whether that's in the public cloud or on premises. Also, consider the value of a dedicated WAN connection between a private cloud and the public cloud provider, sometimes called a dedicated interconnect. AWS, Microsoft and Google each support dedicated connection services, which are available through major regional telecom providers. Regardless of WAN connectivity, hybrid clouds should implement comprehensive encryption for all data at rest and in flight to ensure business data on a network is secure against more abundant and increasingly sophisticated threats.
Public cloud
Although an organization can't augment or change a cloud provider's LAN, it's still crucial to consider the implementation of provider-side cloud services.
Services and actions in the public cloud, such as creating virtual private clouds (VPCs) and subnets, are often incorporated into the cloud user's automated policies and workflows. When a business provisions the resources and services of a public cloud, for example, those activities are frequently part of the user's automation and orchestration efforts. As a result, the public cloud is effectively treated as an extension of the private cloud. It's critical to develop and maintain this consistency for smooth and secure workflows and interoperability between private and public clouds in a hybrid cloud environment.
Further, consider the public cloud provider's reliability and uptime as part of any site reliability or hybrid cloud engineering effort. A hybrid cloud only works when both the private and public clouds are operational. Downtime on either side through hardware failures, misconfigurations or other factors disrupts the hybrid cloud.
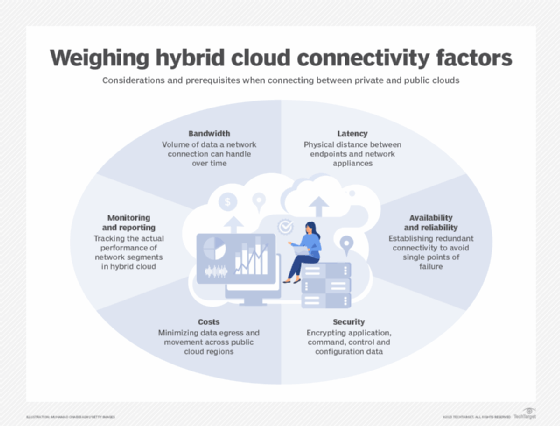
Hybrid cloud connectivity considerations and prerequisites
To establish and maintain a connection between a private and public cloud, it's important to understand network requirements relating to data volume, speed, security and performance. Consider the following six key parameters.
1. Bandwidth
Bandwidth is typically the most common parameter in connectivity. Ideally, it represents the volume of data a network connection can handle over time, usually measured in gigabits per second. Consequently, an enterprise's WAN bandwidth needs for a hybrid cloud are influenced by the amount of traffic that must flow between private and public clouds.
Data-intensive workloads and multiple applications that simultaneously share available bandwidth can drive higher traffic volumes. Generally, it's best to start an enterprise hybrid cloud with a modest, low-cost bandwidth connection and scale up as needed.
Additional bandwidth alone may not be enough for adequate service because a single WAN connection poses a potential single point of failure for the hybrid cloud. Some hybrid cloud users may opt for multiple WAN connections teamed together and load-balanced to handle higher bandwidths while still providing redundancy.
2. Latency
Latency represents the measurable delay from when a packet is sent to when it's received. As latency increases, the apparent responsiveness of an application decreases, which is undesirable for user satisfaction and time-sensitive tasks, such as IoT data processing.
The main factors that influence latency are the physical distance between endpoints and all the switches, routers, gateways and other network appliances that interact with a packet. To reduce the latency of a hybrid cloud connection, minimize the distance between clouds. For example, connect the private cloud to the closest public cloud region, and employ a dedicated connection that minimizes the amount of networking gear between sites.
3. Availability and reliability
If the network connection is down, a hybrid cloud is at best impaired, but more likely, whatever is on the public cloud is unavailable -- data and applications. A single point of failure introduces risk, and a single connection between a private and public cloud can't provide 100% availability. For example, 99.95% availability equates to 21.91 minutes of downtime per month.
It's important to evaluate the availability and reliability of the connections, as well as the guaranteed uptime in the provider's cloud service-level agreement. To enhance availability, establish redundant connectivity to avoid single points of failure. Redundant, or teamed, WAN connectivity is a common tactic to improve hybrid cloud availability and manage bandwidth. But in-house LAN architectures also may benefit from redundant networking architectures. (The cloud provider's internal LAN architecture can't be altered by public cloud users.)
4. Security
Although security is not a physical network characteristic, its role in network traffic must be evaluated. As a general rule, encrypt application data both at rest and in transit, and always encrypt command, control and configuration data. Use common technologies, such as Secure Sockets Layer/Transport Security Layer, to prevent snooping and interception. Try to locate data in the same place as the application to minimize data transfers between private and public cloud infrastructures. Organizations that opt for open internet connectivity can often benefit from other security technologies, like VPNs or direct peering.
5. Costs
A dedicated connection through a major regional ISP, such as Verizon or AT&T, can be expensive. Costs can also surge for high-bandwidth connections, especially redundant connections. Network costs can make hybrid cloud cost-prohibitive. Data ingress, for example, is basically free with most cloud providers, but data egress can prove expensive, depending on the amount of data access and volume of data that's moved. Architect the applications to minimize data egress and movement across public cloud regions.
6. Monitoring and reporting
Implement monitoring and reporting to track LAN and WAN performance metrics, such as bandwidth and latency. Understanding the performance of network segments involved in hybrid cloud can help identify and troubleshoot problems and justify service or design upgrades as the hybrid cloud's requirements change over time.
Hybrid cloud connectivity best practices
No two hybrid cloud architectures are the same. Each implementation depends on an enterprise's specific needs and budget. Still, these best practices can set up hybrid cloud connectivity without breaking the bank:
- Understand the data. Only move the minimum amount of an application's data into the cloud. Identify the correct data, secure it for flight across the network and ensure ongoing adherence to regulatory compliance requirements. Maintain encryption, and verify the data is physically retained in suitable public cloud regions. Other data should remain within the local data center and LAN.
- Understand security and governance. Hybrid clouds are subject to regulatory compliance and business governance factors. Not all data can be stored in all public cloud locations, depending on the sensitivity of the data and the industry. Network management demands attention to issues such as data sovereignty and business continuance.
- Recognize network limitations. Huge data transfers into the public cloud are typically free, but they can place a huge strain on finite LAN and WAN bandwidth. Dedicated WAN connectivity can avoid the congestion that sometimes plagues public internet connectivity, but even that option is often inadequate. Consider a cloud service, such as AWS Snowball or Microsoft Azure Data Box, to physically transfer large volumes of data to the company's public cloud provider.
- Consider application elasticity. While cloud bursting is difficult to implement due to fundamental differences in public and private cloud architectures and services, application elasticity is still a common hybrid cloud use case. Redirecting additional application traffic from a private to public cloud can demand additional network bandwidth and heighten latency concerns. Implement network resources and services to support concurrent application instances, data sets and load balancing between environments.
- Architect the network for scalability. It's easy to connect a LAN to a WAN. But even a single network bottleneck, such as having only one on-premises network gateway, poses challenges in scalability and reliability. When implementing hybrid cloud connectivity, architect redundancy and scalability into the design to avoid single points of failure wherever possible.
- Use common configuration policies. Automation drives the configuration of VPNs, VPCs, subnets and other network resources. But resources in the private cloud are typically spun up and managed differently than in the public cloud. Doing so can involve different policy engines and workflows to manage the same types of activities on either side of the hybrid cloud. To mitigate these issues, use common network policies and workflows to reduce errors and accelerate responses. Many IT vendors offer services that bring a level of parity across environments, including companies with on-premises enterprise roots, such as VMware and Red Hat. AWS, Microsoft and Google also have services that extend their public cloud management tools on premises.
- Measure and test. Just as applications are monitored, use tools to monitor network performance and availability to support hybrid cloud management and enable remedial action or long-term capacity planning based on metrics or alerts. Obtaining a good view of the LAN and public cloud environment might require a small arsenal of tools, including log management, application performance management, network performance management and other open source tools, to piece together an end-to-end view of the hybrid cloud network.
Tools and options for hybrid cloud connectivity
Among the fundamental considerations for hybrid clouds are establishing the connection, selecting a common platform and managing the connected hybrid cloud environment:
- Connections. It's a simple matter to connect a private network to the internet and use public cloud services to create a hybrid cloud. But the potential challenges of public internet connectivity have spawned the availability of dedicated connections. Most major telecom service providers can implement dedicated WAN connections. Alternatively, public cloud providers offer dedicated connection services, such as Google Cloud Dedicated Interconnect, AWS Direct Connect, Azure ExpressRoute, Oracle Cloud Infrastructure FastConnect and IBM Cloud Direct Link.
- Platforms. Given the potential differences between public and private cloud architectures, cloud providers now offer "unified environments" based on well-established technologies, such as Kubernetes and VMware Cloud Foundation. Cloud providers also favor the use of common technology stacks that enable public cloud environments to be replicated within an on-premises infrastructure, such as AWS Outposts, Azure Arc, Azure Stack, Platform9 Managed OpenStack and Google Cloud Anthos. In effect, businesses that adopt such common platforms also adopt the public cloud provider's infrastructure within the private cloud to establish a uniform hybrid cloud environment with common services.
- Tools. Hybrid cloud management also requires the use of tools to monitor and manage private and public components, including networks and services. Many public cloud tools interoperate with private cloud environments, such as Amazon CloudWatch, AWS CloudTrail, Google Cloud Console and Azure management tools. There are also many third-party tools, including CloudBolt, Cloudian, Cloudify, ManageIQ, Morpheus, Flexera Cloud Management Platform, IBM Turbonomic and Apptio Cloudability, as well as management features incorporated into major stacks, such as OpenStack and Apache CloudStack.
Organizations must evaluate and select the connectivity, platforms and tools that are best suited to the needs of their business and long-term hybrid cloud strategy.
Stephen J. Bigelow, senior technology editor at TechTarget, has more than 20 years of technical writing experience in the PC and technology industry.