Caution: There are many ways to lose SaaS data
As the number of organizations using SaaS apps grows, data loss becomes a larger concern. Unfortunately, there appears to be a lot of confusion about where that loss stems from.
SaaS use is on the rise, but many organizations make dangerous assumptions about who is truly responsible for backing up the data in their SaaS applications.
In a recent blog, I referred to this concept as the "big SaaS disconnect." Below, I will specifically cover what our research has taught us about the main reasons behind SaaS data loss.
TechTarget's Enterprise Strategy Group released a report in February 2023 called "Data Protection for SaaS." A majority (53%) of respondents admitted that they have lost SaaS data. I suspect that the number is actually much higher, simply because we know that many organizations don’t have a good handle of their SaaS data protection.
Explanations for data loss may vary
If we "double-click" on the causes of data loss, we can see the disconnect more clearly and get a good gauge of the root causes to address in order to de-risk the organization and mitigate data loss.
In our February 2023 survey, we asked IT professionals what the most common causes were for data loss or corruption of SaaS-based applications. Respondents could select multiple answers, so think of the results as a popularity contest.
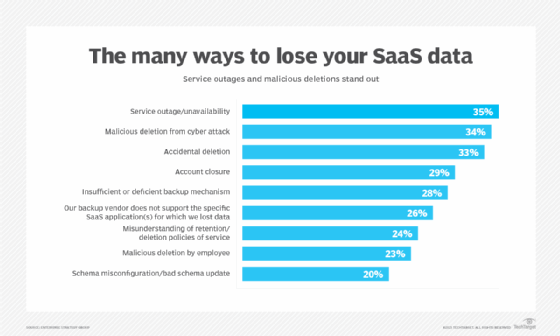
The most popular reason IT professionals cited was the SaaS service itself being the cause of the data loss. I suspect that many people confuse unavailability of the service with data loss, but these are different conversations. Many reasons could contribute to a SaaS application being unavailable, but it does not necessarily mean that your data is gone. If there’s no power in your house, it does not mean that the furniture is gone.
Additional data points in our survey confirm that, overall, many respondents are confused about what availability really means. The question is this: If the service becomes unavailable, what do you do to keep your business running? Do you have a fail-over option? Do you capture transactions in another system temporarily?
There are very few third-party vendors that offer SaaS high availability in the market today. This is a gap in the market that also represents a great opportunity for vendors and service providers.
User confusion might be the biggest SaaS roadblock
As can be seen in our research, 24% reported data loss due to misunderstanding data retention and deletion policies. Another sign of the potential confusion is the fact that 29% reported losing data to an account closure. Let me be blunt: Do you really think a SaaS vendor is going to keep your data for free after you close your account?
Organizations really need to understand what their service-level agreements (SLAs) are for their mission-critical SaaS applications and processes. Thinking about your own environment, do you really know what they are?
Also, with complex data integrations and automation often at play, things can go wrong. Service glitches can create a domino effect of logical data errors. While there are variations depending on the SaaS application, a bad schema update or a misconfiguration can easily delete valuable data. And it may not be possible to get it back.
Don't overlook the ransomware threat
One additional worrisome finding is that the second most cited reason is malicious deletions from ransomware. SaaS applications are not immune to ransomware. What if someone gained access to your credentials and started deleting data, or altering it? You may not be able to roll back unless you have a backup copy.
There is no magical immunity to ransomware in your SaaS applications. On the bright side, SaaS vendors have invested a lot of resources and technology into their security infrastructure, but there’s only so much they can do. Remember: It’s your data and your responsibility to control who has access to it. Beyond cyber attacks, deletion can also happen due to disgruntled employees. There’s nothing new here, but it is a significant problem, with 23% of organizations reporting malicious deletions by employees.
There is still much work to be done around backup processes: Twenty-eight percent of IT professionals we surveyed told us that their backup mechanisms are insufficient, and 26% indicated that their backup vendor does not support the specific SaaS application for which they lost data.
This last point is key. Think about your typical workday: How many SaaS applications do you actually use regularly or almost all the time? Are they backed up? If not for mission-critical reasons, they should be, at a minimum, for compliance or governance reasons.
To stay on top of SaaS data protection, I would propose the following recommendations to both end users and vendors:
- End users must consider and classify all their applications and their interdependence in order to confirm desired recovery SLAs and identify gaps.
- Backup and recovery vendors must cover more workloads, faster. Adding one or two SaaS workloads per year seems unlikely to be enough to satisfy the market.







