
JRB - Fotolia
Can I control the Windows 10 user interface?
You can control the Control Panel, Shared Folders, Start menu and other components in Windows 10 using Group Policy settings.
With Group Policy settings, IT administrators can take granular control of the Windows 10 user interface.
With Group Policy settings, admins can enable or disable individual user interface elements. Admins can turn these elements on or off, and sometimes they can restrict how users can interact with certain elements. For example, IT can use Group Policy to stop users from enabling, disabling or renaming network connections.
Group Policy settings related to the GUI are accessible within Windows 10's local security policy. Open the Local Security Policy by entering the GPEDIT.MSC command at the Windows Run prompt, then navigate through the console tree to User Configuration > Administrative Templates.
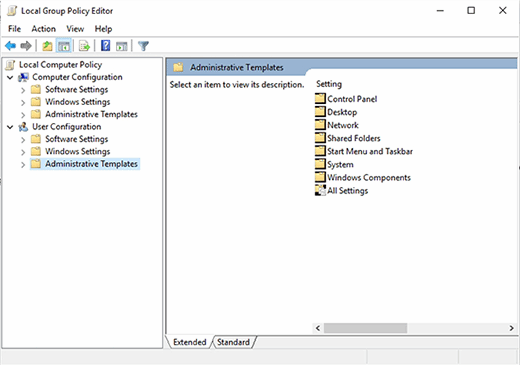
The Administrative Templates container includes a number of sub-containers. IT can use some of these sub-containers to customize the user interface. For example, the Control Panel container includes a series of options that can lock down the Windows Control Panel. It is worth noting that the Control Panel container includes a number of sub-containers that are related to individual Control Panel functions. Some of these sub-containers include Add or Remove Programs, Display, Personalization, Printers, Programs and Regional and Language options.
There are also containers for Desktop, Network, Shared Folders, Start Menu and Taskbar, System and Windows Components. The Windows Components section allows administrators to lock down individual Windows applets such as Internet Explorer or Desktop Gadgets.







