Hyper-V networking: The three virtual switches that fuel connectivity
In this Hyper-V networking primer, learn about the three virtual switches behind Microsoft virtualization connectivity.
Editor's note: This article is the first of a two-part series explaining the basics of Hyper-V networking -- the networking behind Microsoft Hyper-V environments. In part two, we examine Hyper-V logical networks.
virtual networks have the unique role of connecting pools of virtual servers and linking virtual environments to underlying physical networks. In a Microsoft Hyper-V environment, network pros establish and manage virtual network connectivity through the Hyper-V Manager.
Using the Hyper-V Manager, networkers configure and manage extensible virtual switches, which are central to virtual networking.
The most important thing to understand about Hyper-V virtual networking is that physical network adapters are not shared directly with virtual machines (VMs) as they would be with physical servers. When an administrator designates a network adapter for use with Hyper-V, the hypervisor creates a virtual switch and then binds it to a physical network adapter. All of that adapter's communications pass through the virtual switch.
All communications from the host operating system pass through the virtual switch. The physical network adapter is exposed through the host operating system just as it would have been prior to the creation of the virtual switch. However, Hyper-V changes the network adapter's configuration. In fact, Windows removes all host operating system bindings from the physical network adapter and links the adapter to the Hyper-V Extensible Virtual Switch, as shown in Figure A.
 Figure A
Figure A
There is also a virtual network adapter called the vEthernet adapter. This adapter is displayed in the control panel alongside the physical network connections. If the host operating system requires a static IP address or any special bindings, those configurations must be applied to the virtual network adapter rather than to the physical network adapter.
Three distinct virtual switch types in Hyper-V networking
When you open the Hyper-V Virtual Switch Manager and choose the New Virtual Switch option, you can create three different types of virtual switches (as shown in Figure B). Not all of these switches are bound to physical adapters.
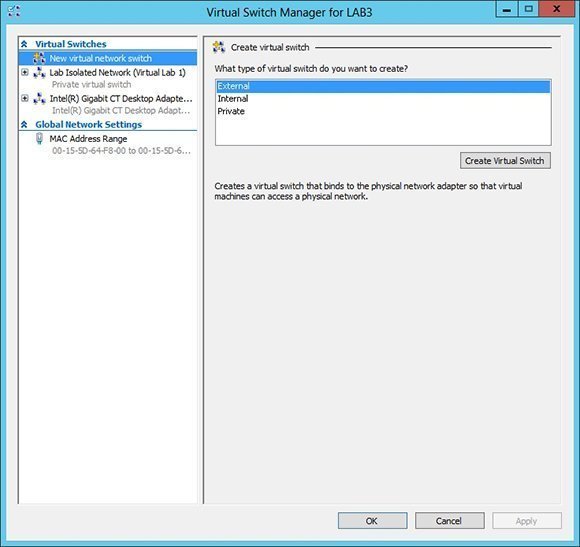 Figure B
Figure B
The first type is an external virtual switch, which is just a basic virtual switch that provides connectivity to the physical network.
The second type is an internal virtual switch, which does not connect to the physical network. It works with network segments that are isolated to the host server. Communications can occur between any VMs that are connected to the virtual switch. A virtual switch is also bound to the host server even though it does not correspond to a physical device. This allows the host operating system to communicate with VMs across the virtual network.
The third type is a private virtual switch, which is very similar to an internal virtual switch, except that it does not provide any connectivity to the host operating system. A private virtual network can be used only to facilitate communications between virtual machines running on the host server.
Internal and private virtual networks are most commonly used in the creation of backbone segments for virtual servers. Doing so is good for security because server backbone traffic never traverses the physical network. These switches also improve network efficiency because some of the communications between virtual servers are removed from the physical network.
Internal networks are also sometimes used by virtual firewalls as a way of preventing a VM from being directly exposed to the physical network. Rather than providing virtual servers with external virtual network connections, virtual servers are bound to an internal virtual network. A firewall VM routes packets between the external network and the internal network.
Hyper-V virtual switches also support the use of virtual LAN (VLAN) identifiers. Technically, VLANs are not necessary in virtual network environments. Functions like those of a VLAN can be more efficiently achieved through modern mechanisms, such as software-defined networking. Even so, Microsoft provides VLAN capabilities as a way of helping organizations that are using VLANs on their physical networks to more easily transition to the use of Hyper-V.
About the author:
Brien Posey is a seven-time Microsoft MVP with two decades of IT experience. Before becoming a freelance technical writer, Brien worked as a CIO for a national chain of hospitals and healthcare facilities. He has also served as a network administrator for some of the nation's largest insurance companies and for the Department of Defense at Fort Knox.








