Technology a double-edged sword for U.S. election security
Technologies were weaponized to undermine the 2020 U.S. presidential election, but IT systems have also helped to identify fraud and verify results in a hotly contested election.
For better or worse, technology played a massive role in the 2020 U.S. election system.
Digital messaging tools that enterprises rely on to communicate with customers were easily deployed for dirty politics. Deepfake videos and misinformation spread like wildfire across social media to a captive audience of voters who clocked more screen time during COVID-19 lockdowns.
While technology served as a blunt instrument to crack the foundation of America's democracy, IT systems are also the way election officials uncover fraud and validate outcomes in a contested election.
Voting machines, infrastructure
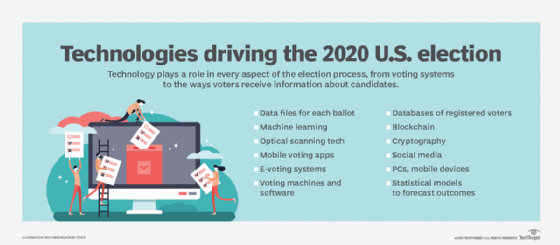
Election technology infrastructure is made up of databases of registered voters, data files for each ballot, servers, storage and networks. There are individual precinct voting machines and software, cybersecurity products, equipment to process absentee and early voting ballots, and statistical models to forecast outcomes.
Mobile apps played a bigger part in 2020's election cycle as well, from apps that helped voters decide who to choose based on the issues they cared about to mobile voting apps used by some states.
Still no standards
With no countrywide or statewide standard systems for voting, the types of hardware, software and the approach to casting ballots vary by district. Many districts use optical scanners to read paper ballots. Some districts print electronic votes and then use optical scanners to read them. Others moved to mobile or electronic voting this year to prevent the spread of COVID-19, despite security warnings about those approaches.
Ahead of election day, experts were concerned about the quick addition of new technologies and expected there to be problems, especially for districts that processed a massive influx of mail-in ballots for the first time.
"This election is totally novel in U.S. history," said Walter Mebane, Ph.D., a professor of political science and statistics at the University of Michigan, Ann Arbor. "And any time you have an innovation in election administration, things go wrong."
Indeed, the influx of mail-in ballots counted after in-person voting was completed fueled claims of election fraud by President Donald Trump, whose campaign has spent millions in recounts in states including Georgia, Iowa and Wisconsin. Recounts have verified President-elect Joe Biden's win.
In early November, Cybersecurity and Infrastructure Security Agency (CISA) director Chris Krebs, hired by Trump in 2017, declared there was no evidence of foreign cyber attacks on election systems. On Nov. 12, the Election Infrastructure Government Coordinating Council along with CISA and other national government agencies published a joint statement saying "The November 3rd election was the most secure in American history." In bold type, the statement reiterated Krebs' statement, saying "There is no evidence that any voting system deleted or lost votes, changed votes, or was in any way compromised."
The group cited security measures such as pre-election testing, state certification of voting equipment and the U.S. Election Assistance Commission's certification of voting equipment.
Nevertheless, Krebs was fired by Trump on Nov. 17.
On Dec. 1, Attorney General William Barr said the Justice Department uncovered no evidence of widespread voter fraud that would change the results of the presidential election.
Election insecurity
The lack of confidence many American voters had in the election system, fueled by President Trump's continuous claims of election fraud, sowed seeds of suspicion around mail-in voting. Trump spread warnings of a "rigged election" during his 2016 presidential run as well.
Experts said the level of mistrust of the election process from inside the White House would make vote audits and verification technologies all that much more critical.
"It's a real challenge, this insider attack [from President Trump]," said Mebane, who is also a member of the Election Verification Network, a nonpartisan group concerned with the integrity and improvement of U.S. voting systems.
"Once the paranoia sets in, even if all the votes are tallied and in order, with all the suspicions being raised, when the inevitable small and big problems occur -- some due to innocent accidents -- a large part of the public won't trust the outcome, whatever it is," he said.
Meanwhile, age-old voter suppression efforts were exponentially easier to pull off using web-based messaging tools.
In March, the Texas secretary of state received reports of robocalls to voters on Super Tuesday falsely stating that the primary would take place the following day. During the congressional primary in Florida this summer, some voters received texts with a link to a video that appeared to be from a Republican candidate saying he dropped out. Twilio's messaging platform was used to deploy those text blasts.
Absentee ballot fraud was uncovered in North Carolina in connection with the Republican candidate for Congress in 2018. Absentee ballots were allowed to be collected on behalf of others. In 2020, absentee voters in North Carolina and many other states relied on online ballot tracking technology to make sure the vote they cast wasn't tampered with and was counted correctly.
Voting systems far from ironclad
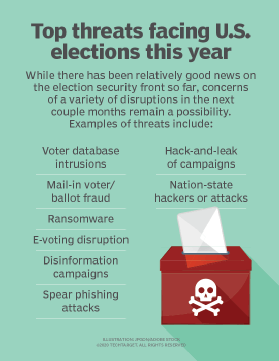
Even with technologies to provide peace of mind that ballots are properly processed, there are a number of risks associated with the U.S. election system. One persistent concern is ransomware attacks on voter registration databases.
Over the summer, a false Russian news report claimed Michigan voter data was hacked. No hack occurred, and the "leaked" voter data was already publicly available. The goal of that misinformation, like so much of it, was to create controversy and distrust of U.S. election systems, according to Doug Cahill, vice president and group director of cybersecurity at Enterprise Strategy Group.
"Disinformation is more of a threat to voter confidence than any technology vulnerabilities," Cahill told SearchDataBackup in a report on voter data security. That's not to say the U.S. election system isn't vulnerable to cyber attacks; hacks happen. Computer scientists warn against the use of internet-connected voting systems, or direct electronic recording systems.
In an Election Security hearing on Jan. 9, Matt Blaze, McDevitt professor of computer science and law at Georgetown University, gave testimony recommending paperless e-voting machines be phased out and "replaced with precinct-counted, optical scan ballots that leave a direct artifact of voters' choices." He also called for audits after every election to immediately detect and correct software failures and attacks, adding that "state and local voting officials need resources, infrastructure and training to properly protect election management IT systems against sophisticated threat actors."
Despite those election security concerns, widely held by computer scientists, the risks of spreading COVID-19 through in-person voting and a desire to give active-duty military a way to vote while overseas tipped the scale in favor of e-voting and mobile voting in some areas of the U.S.
West Virginians were able to cast their vote on a mobile app that used blockchain to store the ballots until election night. It required a "heightened standard of identity verification for users than traditional absentee ballot processes," according to information on the secretary of state's website. Voters from six counties used the app to vote in the primary election. Post-election security audits by "several independent and widely respected technology auditing companies" deemed it a secure platform for voting, according to the website.
While blockchain's distributed ledgers have proven effective for cryptocurrency, security experts are skeptical about applying it to election systems because it could introduce other issues.
In a keynote presentation during the 2020 Black Hat conference, Blaze said blockchain-based e-voting adds another layer of software, and complexity, to the election process and makes ballot secrecy nearly impossible. In addition, he said implementations are heavily dependent on the integrity of client software and the data entered into the ledger in the first place.
Further complicating the process, there are multiple approaches to voting -- and multiple technologies -- used within each state. For example, 13 different vote-counting and tabulation systems are used across Ohio's 88 counties. All are provided by private companies whose proprietary software runs on equipment manufactured overseas, if not entirely, then in part.
Election validation
Election Verification Network's Mebane co-leads the Election Forensics project to develop a set of open source statistical and computational tools that use pattern recognition to help determine whether votes have been tampered with. There is also Microsoft ElectionGuard, a free, open source toolkit that allows voters and third-party organizations to verify election results and allows voters to confirm that their votes were counted correctly. That tool hasn't been widely deployed yet, but it could be part of election infrastructure in the future.
Open source systems that provide transparency into voting verification will be critical in providing confidence to voters. The FBI and CISA released a joint public service statement in September warning that foreign threat actors and cybercriminals were expected to spread disinformation regarding election results.
Disinformation, cyber attacks and social media
With social distancing and lockdown orders in the 2020 pandemic, voters relied more on digital tools for political discussions. Instead of discussing candidates and issues with co-workers in the office, Americans shared political views in a vacuum on social media, spreading and consuming misinformation on those platforms.
A Pew Research study published in July showed that social media is now among the most common ways that people, especially young adults, consume political news. This tendency makes it easier for bad actors to get disinformation in front of voters.
Twitter's policy prohibits posts that manipulate or interfere in civic processes, but states that "not all false or untrue information about politics or civic processes constitutes manipulation or interference."
Under enormous pressure to weed out false information, Facebook in September said it would push authoritative information and take steps to limit misinformation. In late October, the company removed three separate networks for violating its policy against coordinated inauthentic behavior, or CIB, where people coordinated and used fake accounts to mislead people about who they are and their mission, according to a post by the social media giant's head of security policy.
Election forecast techniques problematic -- again
Following the incorrect political polls in the 2016 election, when Hillary Clinton was projected to be a runaway winner, faith in polling data was weak. In the leadup to the 2020 election, data scientist said they had learned hard lessons and had updated data collection practices to be sure they included the types of voters statisticians missed four years ago.
That optimism was brought down when 2020 presidential polling data missed the mark. Analytical models accurately predicted the overall outcome, but in many cases underestimated the percentage of voters who would vote to reelect Trump.
While the social media companies work to keep inauthentic accounts off their platforms, authenticity is becoming more difficult to sus out -- particularly with easy-to-create deepfake videos. These AI-driven videos are often used as a tool to damage political candidates, but the more serious threat of deepfake videos is their potential to spread incorrect information about how, where and when to vote in the days leading up to the election. Microsoft recently released an AI tool called Video Authenticator to help identify deepfakes. The algorithm behind the technology has an accuracy rate of just 65%.
Microsoft detected cyber attacks targeting candidates in the 2020 presidential election, including unsuccessful attacks on people associated with both the Trump and Biden campaigns.
In October, Microsoft obtained a court order to intercept a ransomware botnet called Trickbot that posed an election security threat. In partnership with telecommunications providers around the world, Microsoft reported that it cut off key infrastructure to prevent Trickbot operators from initiating new infections or activating ransomware already dropped into computer systems.
Also ahead of the 2020 election, Microsoft trained election officials in 38 states on cybersecurity.






