
Laurent - stock.adobe.com
What's the purpose of CAPTCHA technology and how does it work?
Learn about the purpose of CAPTCHA challenges that enable websites to differentiate bots from authentic users to stop spammers from hijacking forums and blog comment sections.
What is the technology used on blogs and some web search tools when a user is presented a box with letters and has to retype the displayed information to verify their identity or that they are the intended recipient?
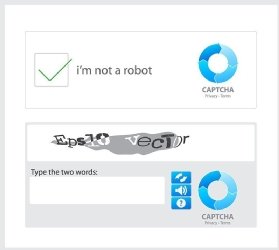
This technology is CAPTCHA, an acronym for Completely Automated Public Turing test to tell Computers and Humans Apart. A CAPTCHA is usually a graphic image with a series of distorted letters on an equally distorted or multicolored background. Other types of CAPTCHA challenges require a user to identify photos, do simple arithmetic problems, provide a response to an audio snippet or simply click a box that says, "I'm not a robot."
The CAPTCHA algorithm is public, as the "P" in the name implies. The test was developed in various forms around 1996, but it got its distinctive name in 2000 from researchers at Carnegie Mellon University and IBM. Cracking the algorithm won't make the CAPTCHA vulnerable, since the algorithm is only used for generating the random series of letters and numbers in the image. The system works because humans and computers process strings of characters differently.
Why is CAPTCHA important?
One of the most important reasons for CAPTCHA is to defend against ad spammers who promote their scams in comments on webpages. By requiring all users to negotiate the CAPTCHA authentication, administrators can filter out spammers who attempt to automate their activities.
CAPTCHA technology authenticates that a real person is accessing the web content to block spammers and bots that try to automatically harvest email addresses or try to automatically sign up for access to websites, blogs or forums. CAPTCHA blocks automated systems, which can't read the distorted letters in the graphic.
How CAPTCHA works
CAPTCHA is a form of challenge-response authentication, using challenges that can easily be responded to by people but that are difficult for bots. Rather than authenticating the identity of the person accessing the resource, CAPTCHA is used to authenticate that the entity attempting to access the resource is actually human and not a bot or other piece of malicious software.
CAPTCHA challenges need to be difficult enough to defeat attacks that use AI to try to solve them but easy enough for people to solve.
One of the problems with CAPTCHA is that, sometimes, the characters are so distorted that they can't even be recognized by people with good vision -- let alone visually impaired individuals. Depending on local accessibility regulations for websites, this can also be a compliance issue for some web-based businesses.
The reCAPTCHA project improves on CAPTCHA's
antibot strategy.
Even as the CAPTCHA developers continue to improve the utility, attackers are also always on the alert for new vulnerabilities and tactics for defeating CAPTCHA. In 2015, CAPTCHA-bypassing malware was discovered in Android apps offered through Google Play Store. And, early in 2019, security researchers reported the ability to bypass spoken phrases with the UnCAPTCHA proof-of-concept attack. The reCAPTCHA project aims to strengthen CAPTCHA, even as attackers continue to target it through exploits like ReBreakCAPTCHA.
When to use CAPTCHA
Use CAPTCHA for webpages that accept input from unauthenticated users. CAPTCHA is not usually needed for accepting input from users who have already logged into their accounts, but it can help slow down unauthenticated users -- like bots -- that try to post spammy comments in forums or blogs without the need to be authenticated as legitimate users.
CAPTCHA technology is easy to implement but requires some knowledge of PHP or other web scripting languages. For more information about integrating CAPTCHA protections, check the reCAPTCHA project's developer's guide.






