
adimas - Fotolia
Maze ransomware gang pledges to stop attacking hospitals
The infamous Maze gang announced it has stopped ransomware attacks on healthcare and medical facilities because of the seriousness of the coronavirus pandemic.
The notorious Maze ransomware gang announced Wednesday that it will not attack any healthcare organizations during the COVID-19 pandemic.
The pandemic has put a strain hospitals and public health agencies in recent weeks as governments across the globe struggle to contain the spread of COVID-19, also known as the new coronavirus. Some security vendors have expressed concern that coronavirus-related threats could soon include ransomware attacks, which would have a crippling effect on healthcare and government organizations working on treatment and containment of the virus.
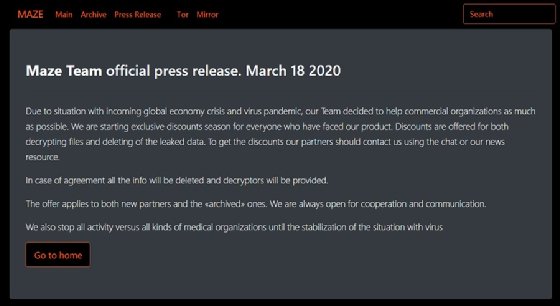
But at least one cybercrime outfit is pledging to refrain from such attacks, at least on healthcare organizations. The Maze ransomware gang, which last year began "shaming" victims by exfiltrating and publishing organizations' sensitive data, promised to " stop all activity versus all kinds of medical organizations until the stabilization of the situation with virus," according to an announcement on its website.
BleepingComputer, which first reported the announcement, also contacted other ransomware operators about stopping attacks on healthcare and medical organizations during the pandemic. The DoppelPaymer gang also pledged to stop such attacks, though other ransomware groups such as Ryuk and Sodinokibi/REvil did not respond to Bleeping Computer's queries.
The Maze gang's pledge, however, says nothing about attacks on city, state or local governments or public health agencies. The Maze gang also said it will "help commercial organizations as much as possible" during the pandemic by offering "exclusive discounts" on ransoms to both current and future ransomware victims; the cybercriminals said they will provide decryptors and deleted any data published on its website.
Despite the promises of the DoppelPaymer and Maze ransomware gangs, it's unclear how much control they have over what organizations are attacked. Many outfits use a ransomware-as-a-service model where they develop the malicious code and then sell it to other cybercriminals, which are often called affiliates.
These affiliates then conduct the actual intrusions, data exfiltration and ransomware deployment and pay the authors. Many ransomware incidents are initiated through phishing emails and brute-force attacks on remote desktop protocol instances; threat researchers have said it's likely that ransomware actors aren't specifically targeting organizations by name or industry and are merely capitalizing on the most vulnerable networks.








