Twin - stock.adobe.com
Healthcare CISO offers alternatives to 'snake oil' companies
Indiana University Health CISO Mitchell Parker discussed internal risk assessments, security snake oil salesmen and more at his Black Hat USA 2020 talk.
Indiana University Health CISO Mitchell Parker believes part of the reason hospitals and medical facilities are hacked so frequently is that they're falling for "snake oil companies" that fail to improve security postures.
In a Black Hat USA 2020 session, titled "Stopping Snake Oil with Smaller Healthcare Providers: Addressing Security with Actionable Plans and Maximum Value," Parker discussed his experiences working with several different healthcare organizations, which were spending their limited security budgets on the wrong things. The session warned of snake oil vendors, or, as Parker said, companies "that have only provided risk assessments, that cost a lot of these smaller providers tens of thousands of dollars, and don't deliver anything of value. And worse, taking money out of the risk management plans, A.K.A. negative value."
A healthcare CISO can't afford to waste money on those kinds of companies and get bad advice on how to better protect their organization, Parker said.
"Healthcare has been the most affected industry by ransomware, data breaches and hacks. I take a look on the news every week -- there's yet another provider that's been hacked. In a lot of cases, providers have had to shut down, and patients were not even able to get hold of their medical records," Parker said. "And so what we've noticed in our work is the guidance provided to many providers has not addressed what organizations actually need to do to protect their patients and themselves."
The healthcare industry has long been inundated with cyber attacks, from ransomware infections to data breaches. Despite some ransomware groups publicly pledging to not attack hospitals or medical facilities during the COVID-19 pandemic, many security experts say healthcare is still one of the widely attacked industries.
"We know for a fact the healthcare organization is the most highly targeted, in general," Maya Levine, security engineer at Check Point Software Technologies, said. "Healthcare organizations are always being targeted for a really terrible reason: It's an incredible disruption to business and the livelihood of people."
During a live Q&A following the presentation, SearchSecurity asked Parker what he considered to be warning signs for snake oil vendors or risk management firms. "If someone says they can solve all of your problems instantly, or if they offer solutions without analyzing your systems, then watch out," he said.
Security advice for healthcare CISOs
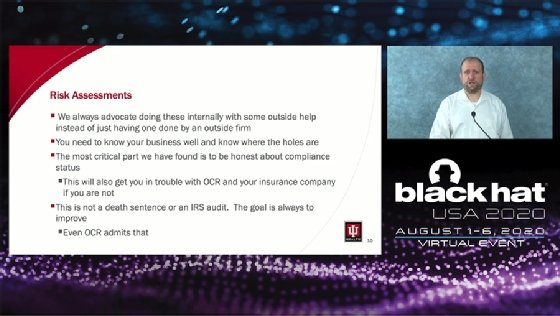
As part of the presentation's advice to organizations, Park said healthcare organizations, especially smaller hospitals and medical facilities, should employ cloud-based backups and conduct risk assessments internally -- with some outside help -- to protect against ransomware.
"We always advocate doing [risk assessments] internally with a little bit of outside help instead of just having one done by an outside firm. The reason why is you need to know your business well and where your holes are," Parker said.
He recommended healthcare organizations adopt password managers to better protect accounts and credentials. "You need to get very good with password managers to make sure your team knows how to use them" because "no other industry I've worked in has had an emphasis on having numerous incompatible logins," Parker said.
This can work in tandem with two-factor authentication. "If there's one factor to stop the majority of hack attempts, it's good two-factor authentication like Duo, Authy or YubiKeys -- all of which work very, very well," he said. This is especially true for healthcare, Parker argued, because numerous phishing attacks in healthcare use compromised accounts to conduct their attacks.
He also discussed the dangers of remote desktop protocol (RDP) and VPNs.
"One of the most important lessons we learned over the past year is that remote access is a huge target and there's actually been numerous successful attacks on both remote desktop and unpatched VPN software," Parker said. "I'll be very clear about something else. Straight remote desktop is not effective. You will get owned, BlueKeep or not. You will get owned."
Cloud backups are critical, Parker said, mainly to ensure quicker recovery time from cyber attacks. In addition to simply having cloud backups, he recommended organizations protect their backups, test their backups and store backups separately under different credentials.
In one of the session's final points, he discussed the value of endpoint detection and response (EDR) over antivirus. Not only does it integrate better with SIEMs and log management technology, but antivirus just doesn't work for the healthcare tech environment.
"When it comes to EDR, I'll be very clear about something else. Antivirus in healthcare is DOA. Why? Because there's too much interference with applications and most of your software packages out there in healthcare that run come with an exceptions list, which means that it takes me about 30 seconds on Google to find the exceptions list to know where I can place custom malware. So you want to get rid of the ability for the exceptions to run. That's why we like EDR better."
Parker also offered recommendations to healthcare organizations for physical, EHR maintenance, ZFS management and more.
Lastly, Parker encouraged healthcare organizations to vet their medical device vendors and offered IU Health's own baselines and requirements for information security and vendor management for other companies to use. "You need to perform a risk analysis of your vendors," he said. "Everyone from small providers to some of the largest healthcare systems in the world use ours."