
Ransomware in 2022: Evolving threats, slow progress
Experts say trends involving new forms of leverage, increasing numbers of affiliates and the evolving cyber insurance market are shaping the ransomware landscape in 2022.
While activity has apparently declined in recent months, experts say the story of ransomware in 2022 involves notable trends beyond just the sheer number of attacks.
Ransomware's boom in the past decade has taken many twists and turns, from now-ubiquitous double extortion techniques to attacks against critical infrastructure. It has also been a wake-up call to organizations without adequate security postures.
In Sophos' State of Ransomware report for 2022, the vendor surveyed 5,600 IT professionals from small, medium and large organizations about ransomware, with over 900 sharing details of ransom payments made. The April report, overall, was a mixed bag.
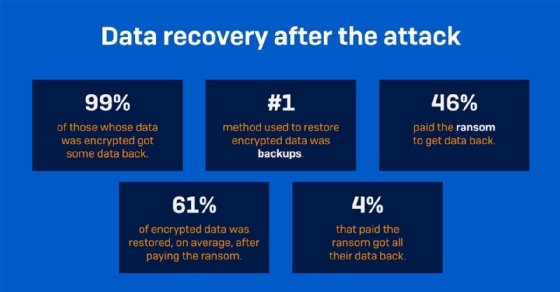
On the more negative end, 66% of surveyed organizations were hit with ransomware last year, up from 37% in 2020. Ransom payments are also higher, in part thanks to the rise of big game attacks. More victims, too, are paying the ransom according to Sophos.
More positively, the average remediation cost following an attack dropped from $1.85 million to $1.4 million. Sophos gave two reasons for this. One, the prevalence of ransomware has lowered the reputational damage endured by a victim. Two, insurance providers are better able to guide victims through an attack.
More recently, U.S. officials have cited a drop in overall ransomware attacks against U.S. organizations since Russia's initial invasion of Ukraine earlier this year. This year, SearchSecurity began tracking ransomware attack disclosures and public reports in the U.S.; the data shows a significant decrease in reported and disclosed attacks in recent months.
However, infosec professionals say there's more to the picture than just the attack numbers. At RSA Conference 2022, SearchSecurity spoke with several experts and attended a number of sessions to assess the current state of ransomware in 2022. Some of the trends observed include new techniques threat actors use to gain leverage, the growing influence of cyber insurance and slow but steady progress against the threat.
The evolution of leverage
Ransomware, as a concept, has existed for decades -- effectively since the dawn of the consumer internet. Traditionally, ransomware has been defined as a threat actor using malware to encrypt the files on a victim's computer; the victim then would pay a ransom in order to decrypt their files.
Ransomware has changed significantly in recent years. While these classic attacks still happen, the standard enterprise ransomware attacks now involve "double extortion" techniques, where bad actors will both encrypt victim data and steal said data with the intent of publicly leaking it should the victim not pay up.
Double extortion techniques have become the norm in enterprise ransomware attacks, but they are by no means the only avenue threat actors use to get paid. For example, Sophos senior security advisor John Shier told SearchSecurity that one emerging trend involves threat actors stealing data without actually encrypting the victim's files. This is sometimes referred to as extortionware.
"It's too early to say whether this is actually a trend that's going to pick up, but I've seen some groups focusing on the data extortion itself," he said. "The thought is, if a threat actor encrypts stuff, you're just going to recover from backups. But you still want to make sure that the privacy commissioner doesn't find out and you don't get fined. We've seen some crews basically saying, 'No, we're not going to waste our time encrypting stuff. We're just going to steal as much data as we can and then use that as the ransom.'"
Another benefit to this style of attack is that it limits the potential for critical organizations like hospitals to have their operations disrupted, which would likely result in harsher law enforcement attention.
Data can be a powerful tool to get victims to pay ransomware threat actors, whether combined with encryption or not. For example, a Finnish psychotherapy practice experienced a theft of patient records in 2018 that later resulted in patients being extorted directly.
In other cases, encryption may be the most effective weapon to get a ransom payment. For example, industrial settings utilize internet-connected operational technology (OT) and industrial control systems (ICS) that often fall prey to ransomware attacks. ICS/OT attacks are particularly brutal, because the nature of industrial and critical settings means that work may come to a halt or critical services may be disrupted.
"Triple extortion" techniques are also beginning to emerge. In these attacks, cybercriminals encrypt data, steal data and threaten DDoS attacks against the victim organization.
Low barrier to entry
Attacks have gotten bigger, more expensive and more frequent in recent years, thanks in part to the ransomware as a service (RaaS) model. The RaaS ecosystem includes many different types of players, but the two main types of threat actors defining the market today are ransomware operators and ransomware affiliates.
The operators are the ransomware developers -- ringleaders who create the malware, distribute it, conduct their own attacks and recruit affiliates. The affiliates, meanwhile, are smaller-time cybercriminals who purchase access to a ransomware family's malware kit and infrastructure for a price, typically a combination of subscription fee and profit sharing with the operator.
Well-known ransomware operators who have had affiliate programs include REvil, DarkSide and LockBit.
John Dwyer, IBM's head of research at X-Force, told SearchSecurity that the rise of affiliates is a reflection of the multifaceted economy that has built up around ransomware.
"If you look at the perfect storm of events that have happened that enable the criminal ecosystems that support ransomware, you have the affiliate model and the rise of cryptocurrency -- to actually be able to exchange money with from criminals," he said. "And then you also have the little economies that support the business, like through the access brokers and things like that."
"I think we've now seen a business model being built around a particular sort of cybercrime. And that is, what we're seeing is that the attack isn't changing; the number of opportunities for attack based on the sheer number of criminals that are in the businesses is increasing."
X-Force head Charles Henderson said affiliates have created a condition in which "criminals are more collaborative than the cybersecurity industry."
"That is a that is a recipe for disaster, frankly, largely because anyone that's run a red team or any kind of offensive security knows that you succeed when the attacker communicates better than the defender," Henderson said. "There are a lot of indicators, when you're running a red team, that something is going wrong to the defender. But unless they correlate those items and piece them together, the likelihood is that the overall mission will go undetected. I think as an industry, we need to get better."
An early June X-Force report found that the average length of an enterprise ransomware attack -- between initial access and malware deployment -- dropped 94.34% between 2019 and 2021. Attacks went from taking over two months to just 3.85 days on average. The rapid exploitation of vulnerabilities like ZeroLogon was a factor, the report claimed, but Dwyer said another factor is the low barrier to entry ransomware actors enjoy today.
"If we look at the data, the tools, techniques and procedures aren't evolving at such a high rate that it would cause a drop in the overall lifecycle. But it's never been easier than it is right now to carry out a ransomware attack," he said. "Because of the affiliate models and things -- you can rent infrastructure, you can rent tools -- you can buy into the game for a small investment."
Cyber insurance's seat at the table
Cyber insurance is a controversial topic within the infosec community. The controversy is not because organizations shouldn't be protected financially in cyber crises, but rather over whether organizations treat cyber insurance as a replacement for implementing holistic security practices.
Sophos' Shier said that Sophos, which sends out a survey to organizations every year as part of its State of Ransomware report, asked this year whether responders expect to get hit by ransomware over the next 12 months. One response to the multiple-choice question is along the lines of, "No, we don't expect it because we have cyber insurance."
"I can't remember the numbers but it's shockingly high, and in my opinion anything above zero is shockingly high because cyber insurance does nothing to prevent an attack," Shier said. "Yet people are under the impression that for some reason, it's just going to magically keep the attackers away."
Previously, companies weren't motivated to have a detailed cyber response plan thanks to high probability of insurance payouts, but there is indication the tides are changing.
According to Sophos' April ransomware report, cyber insurance paid out some or all of an attack's cost in 98% of cases.
Additionally, 94% of respondents said their experience getting covered by insurance has changed over the last year, "with higher demands for cybersecurity measures, more complex or expensive policies and fewer organizations offering insurance protection." In addition, 97% said they had made changes to their cyber defenses in order to better position themselves for coverage, while 52% have made process changes, 64% implemented new technology or services and 56% have increased employee education.
X-Force's Henderson said that, on a whole, organizations are getting better at using insurance as part of the response plan rather than as the incident response plan itself.
"One thing that I think as of late, we're getting better at is the understanding that cyber insurance is not an incident response plan," he said. "Cyber insurance is a good thing for many organizations. They can help guard against the inevitable, but it isn't your response plan."
Progress and room for improvement
SearchSecurity asked ransomware experts about what organizations are getting better at in the fight against ransomware.
Marc Rogers, Okta executive director of cybersecurity, said that one area where he has seen improvement is transparency following a cyber attack.
"I think that there is a much stronger desire to be transparent," he said. "I've been around three decades now, and when I started it was unheard of for a company to talk about [being hit by a cyber attack]. Now, I would say it is normal for companies to talk about it. The challenge comes to how much they talk about it. What do they say? What does transparency mean? And I think we're still feeling around that and trying to find the right answer. But I do think the trend is toward being more transparent."
Rogers, who is also a member of the Ransomware Task Force established last year, also spoke positively about the communication line between private sector organizations and the U.S. government.
"We, the private sector, are closer to the government, more than we've ever been before. The doors are open in a way that we can inject what we believe and what we hear into processes, and we get questions back, which tells me they're listening and they're looking for further guidance on what to do," he said. "If you look at some of the hearings that have been held on various major vulnerabilities like Log4j, the private sector has been given a very loud voice in terms of how the government should handle this and prevent this. And the implementation has followed quite quickly."
At RSAC 2022, Cybersecurity and Infrastructure Security Agency (CISA) Director Jen Easterly appeared on a panel with other U.S. government officials where she promoted collaboration between sectors and within government agencies. CISA also recently begun initiatives to strengthen national defenses and promote cyber readiness, including Shields Up and the Joint Cyber Defense Collaborative.
Another area of improvement came from Ransomware Task Force members at an RSAC 2022 session. During it, panelists called for better incident reporting following a ransomware attack. Michael Phillips, chief claims officer at cyber insurer Resilience, said low incident reporting has previously resulted in a data gap between organizations, the government and the number of ransomware attacks actually occurring.
IBM X-Force head of strategy John Hendley, who was part of the same interview with Dwyer and Henderson, said he is heartened by organizations taking offensive cybersecurity like red teaming more seriously. However, he noted that one major area for improvement is for organizations to implement the recommendations that come from red team exercises.
"Let's say that we go into an organization and we find a bunch of high- or critical-risk issues. You do that test again a year later and there's a decent chance that a lot of those are still going to be there," Hendley said. "Unfortunately, we see a lot of organizations struggle to actually implement the change."
Alexander Culafi is a writer, journalist and podcaster based in Boston.







