
Sikov - stock.adobe.com
Cryptocurrency wallets might be vulnerable to 'Randstorm' flaw
Cryptocurrency recovery company Unciphered discovered a vulnerability in a JavaScript Bitcoin library that could jeopardize private keys.
Millions of cryptocurrency wallets created between 2011 and 2015 are potentially affected by an open source software vulnerability and might need to be regenerated, according to new research from Unciphered.
While helping a customer regain access to a locked Bitcoin wallet last year, Unciphered discovered issues in the open source JavaScript Bitcoin library BitcoinJS that required further investigation. Security researchers at the cryptocurrency recovery firm confirmed that the vulnerability stemmed from a string of programming mistakes -- and realized they were not the first to uncover the cryptocurrency threat.
Unciphered worked on the vulnerability for the last 22 months, engaging in coordinated disclosure with multiple entities, proving that its researchers could break into crypto wallets, working on remediations and alerting millions of users. Public disclosure proved difficult because researchers did not want to tip off attackers.
In addition, because patching alone is insufficient, researchers had to identity and notify cryptocurrency wallet developers that were active between 2011 and 2015 and ask them to warn customers if possible.
Like the disclosure process, the vulnerability was not straightforward either. There is no CVE for the flaw, but it affects the random numbers generated to secure cryptocurrency wallets. In addition, the researchers discovered other issues that, if combined, would allow attackers to gain access to wallet keys. Researchers dubbed the threat "Randstorm."
"Randstorm() is a term we coined to describe a collection of bugs, design decisions, and API changes that, when brought in contact with each other, combine to dramatically reduce the quality of random numbers produced by web browsers of a certain era (2011-2015)," Unciphered wrote in its FAQ. "Large random numbers are a critical ingredient in the overall security of blockchain technology."
Unciphered disclosed technical details in another blog post Tuesday. Researchers pinpointed the source of the vulnerability to the SecureRandom() function found in the JSBN JavaScript library, which BitcoinJS used through 2014.
The vulnerability chain combines the SecureRandom() function "with weaknesses that existed in major browser implementations of Math.random()." As a result, Bitcoin private keys could have been generated with less than the required amount of entropy, making them more vulnerable to attacks.
While an exact time frame was difficult to establish, researchers observed vulnerable wallets being generated from 2011 to 2015. Bitcoin wallets were affected, but Dogecoin wallets might be as well.
Billions of dollars at risk
The investigation also determined that Unciphered was not the first to discover security issues in BitcoinJS. Reports of vulnerabilities in the SecureRandom() function that affected numerous cryptocurrency products were detailed in 2018, while issues related to Math.random() dated back to 2015.
Since discovery in January 2022, Unciphered said it has notified Blockchain.com, BitGo, Block.io/Dogechain.info, BitPay, Blockstream Green, Bitaddress.org, Coinkite and BitcoinJS. Not all notified vendors were affected, and Unciphered warned that there could be other unidentified affected parties.
Researchers added that attack impact also varies. Factors include how long the vulnerable code was used, what additional mitigations were enacted and the size of the user base at the time.
"Typically, in order for this attack to be feasible, an attacker would need something which was generated from Math.random() at the time of wallet generation -- this would typically be the wallet GUID or IV. This reduces the amount of necessary work anywhere from 32 to 64-bits," the blog read.
Researchers warned that the vulnerability "potentially affects millions of cryptocurrency wallets" generated between 2011 and 2015. Unciphered estimated that approximately 1.4 million bitcoin are contained in wallets with weak keys. "If we conservatively estimate that only 3-5% of wallets generated during that time were affected, the current value of coins at risk is between 1.2 - 2.1Billion USD (assuming 1 BTC=$30,000)," the company wrote in the FAQ.
While the potential attack scope and fallout could be substantial, Unciphered said the BitcoinJS vulnerability speaks to a bigger issue with the software supply chain that researchers illustrated with an image from the popular webcomic XKCD.
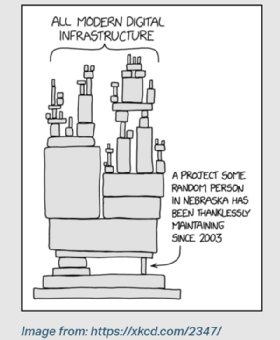
"Almost all substantial software development projects rely on third party libraries. As articulated in the cartoon above, it is not uncommon for popular code to be reliant on projects which are under-staffed or even abandoned," the blog read.
Unciphered highlighted a warning taken from BitcoinJS's GitHub page that urged users to "audit and verify any underlying code." That recommendation should apply for code taken from any open source project, according to the blog.
While Randstorm has not been exploited yet, researchers confirmed that it is possible. Recent attacks show that cryptocurrency remains a popular target for threat actors.
"In the event that software used to generate wallets is discovered to have created vulnerable wallets, the only solution is for the users to move the assets to new wallets, or have those users legally direct someone else to do it on their behalf," the blog read. "This is why we are still dealing with this vulnerability in 2023."
Arielle Waldman is a Boston-based reporter covering enterprise security news.







