
Serg Nvns - Fotolia
How to manage third-party risk in the supply chain
From third-party risk assessments to multifactor authentication, follow these steps to ensure suppliers don't end up being your enterprise cybersecurity strategy's weakest link.
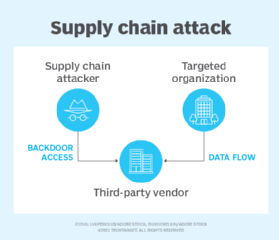
The recent SolarWinds supply chain hack has affected public and private organizations worldwide, but this type of attack is not new. The Target, Home Depot, Boston Medical Center and PNI Digital Media data breaches are all instances where malicious actors took advantage of security weaknesses in the supply chain to compromise more heavily defended or more valuable networks.
Stolen login credentials, certificates and keys are often at the root of these attacks, enabling hackers to open the door to their smaller or less security-aware targets' internal networks.
The SolarWinds incident shows, however, that even highly secure providers can be used as a steppingstone when extremely skilled hackers are involved. To mitigate this potent threat and other threats like it, every organization needs to learn how to manage third-party risk.
Here, learn what to expect and require from any third party connecting to enterprise systems to create a vetted and trusted security-aware supply chain.
Verify partners' controls and certifications
Organizations must require subcontractors, vendors and supply chain partners to meet the certification requirements of appropriate compliance standards, such as ISO 27001, PCI DSS, HIPAA and ITAR. This will demonstrate that at least a certain level of IT security is being met.
Note, however, that gaining these accreditations may be too costly for smaller companies. In this case, their policies and practices should be contractually obliged to meet the organization's own security standards. Asking for a System and Organization Controls 2 report is a good place to start, as it covers how a business oversees security, availability, processing integrity, confidentiality and privacy of a system.
Perform third-party risk assessments
Even with certifications and compliance standards assurances in place, a third-party risk assessment should be performed on each supplier to identify exactly which types of security controls and monitoring are required. An annual third-party audit should be conducted to ensure these controls are in place and working correctly. Where this is not possible, agree on a mechanism capable of monitoring compliance.
Be sure to make risk assessments information-driven rather than supplier-centric. This approach makes assessments easier to repeat across different vendors. Assign an assurance level to each application handling data. To determine the security controls required before access can be granted, base those assurances on business risk factors, such as sensitive information disclosure, personal safety, reputation damage, financial loss, operational risk and legal violations.
As stolen credentials are often used to gain a foothold in a network, multifactor authentication should be mandatory for access to any shared resources.
Map flow of traffic and critical data
Security teams must agree on a well-defined strategy that governs access to the organization's internal resources. This should be based on the principle of least privilege and strictly map the flow of traffic and critical data to enable efficient monitoring of supplier access.
This monitoring should -- at a minimum -- be able to detect threats, unusual activity and data exfiltration. Network segmentation and compartmentalization, or the use of parallel networks to run supply chain applications, will also help to build a more resilient environment able to detect, deny and disrupt an attack.
With regard to data sharing, it is important to contractually agree on what information can be shared and with whom, as well as who maintains ownership of the data and what is considered acceptable use. In addition, all members of the supply chain should be required to encrypt data at rest and data in transit.
Additional steps
Beyond certifications, risk assessments and data management, security awareness training and social engineering assessments are also important to ensure all personnel in the supply chain have received appropriate training.
To be prepared for the worst, organizations can also periodically test off-site data backups and disaster recovery plans; this should include test scenarios with suppliers. Both parties must have a plan to notify the other if their network, systems or data have been compromised or if a breach is suspected so there can be a coordinated response.
Security is only as strong as the weakest link. While securing your supply chain may seem rather onerous, failure to do so could prove far more costly. Marriott's failure to perform due diligence on its subsidiary Starwood's IT infrastructure has been specifically singled out in litigation following a data breach that affected up to 500 million guests.
Supply chain and third-party risk management must be embedded within procurement and vendor management processes with clear metrics and service-level agreements governing application and data security. Although these steps will not guarantee complete security of sensitive data, they will make the supply chain stronger and the organization less likely to become the victim of a supply chain-based attack.







