built-in administrator account
What is built-in administrator account?
In the Windows operating system, the built-in administrator account -- the first account created when the OS was installed -- has the highest permissions of any profile on the computer system. That means the built-in administrator account has elevated administrator privileges to do anything on the system without requiring confirmation.
Windows OS built-in administrator account explained
In Windows systems, the built-in administrator account is similar to the "root" or "superuser" accounts in other operating systems. It was originally intended to facilitate system setup and disaster recovery. It can also be used to run programs and apps before a user account is created.
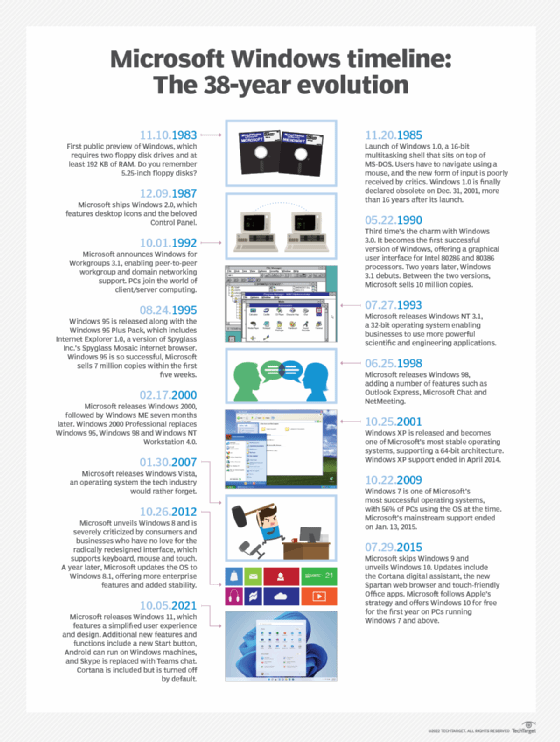
In Windows XP and prior versions of the OS, the built-in administrator account was enabled by default. Although the administrator account was necessary in Windows XP and earlier OSes, it's not needed in later versions, so it is disabled by default to reduce the attack surface of a Windows PC.
The built-in administrator account is useful for troubleshooting deep system-level issues but must be used sparingly. Even when it is enabled cautiously, it's good practice to immediately disable the account once troubleshooting is complete.
Security concerns with built-in administrator accounts
In Windows XP and previous systems, the built-in administrator account was always called "administrator." For this reason, it had the same username on all computers and was often given a consistent password throughout the enterprise. By default, this password was blank. This created security problems for two reasons:
- Anyone could log into the account and gain full access to the system.
- Any malware installed on a system -- either deliberately or mistakenly – could end up infecting everything on the computer because the admin account could not stop it from spreading
To address these concerns, Microsoft disabled the administrator account by default starting in Windows Vista. This ensures that only local accounts specifically created with administrator privileges -- or domain accounts that are members of the domain administrator's group -- can log on as administrator.
Built-in administrator account and user account control
The built-in administrator account can bypass all user access control (UAC) protections. In Windows, UAC shows a security prompt when a user tries to perform an action that requires elevated privilege levels. Examples of such actions include installing an application for all users, editing a registry and opening the command prompt as admin.
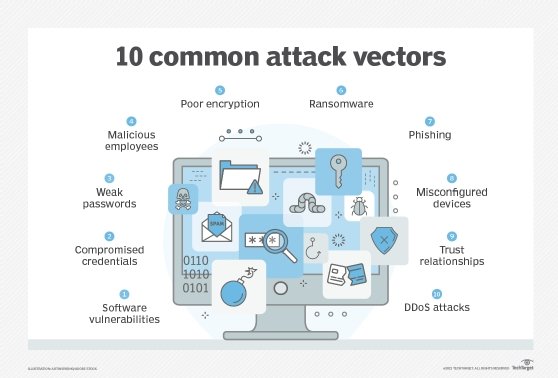
When users with standard privileges are prompted by UAC, they must provide admin credentials (username plus password) to proceed. Admin-level users, however, only need to click on a confirmation button. Since the built-in administrator account has no boundaries or limitations, it can bypass all UAC protections and end up making the system vulnerable to cyber attacks.
Further, allowing every non-admin user to use the administrator account makes it harder for real admins to audit what users are doing. This lack of auditability -- and transparency -- can be problematic when a cyber attack needs to be investigated.
Enabling built-in administrator accounts
Later versions of Windows disable the built-in administrator account by default. However, users can disable the account in three ways:
- Using an answer file
The built-in administrator account can be enabled by modifying the AutoLogon setting to Administrator in Microsoft-Windows-Shell-Setup component. This method enables the account even if the password is not specified.
To create the answer file, the Windows System Image Manager (Windows SIM) available in the Assessment and Deployment Kit is required.
- Reentering audit mode
This method is applicable only to those systems/computers that have not yet gone through OOBE (out-of-box experience). Pronounced "oo-be," the term refers to the part of the installation users go through when setting up a new device. Here, the built-in administrator account can be enabled by reentering the audit mode.
- Using Local Users and Groups MMC (for server versions)
With the help of Local Users and Groups Microsoft Management Console (MMC), the properties of the administrator account can be changed by following these steps:
- Open MMC and select "Local Users and Groups."
- Right-click the "Administrator" account and select "Properties."
- The "Administrator Properties" window appears.
- In the "General" tab, clear the "Account is Disabled" checkbox.
- Exit MMC.
Disabling the built-in administrator account
For new installations, once the end user creates an account in OOBE, the administrator account is automatically disabled. Also, original equipment manufacturers (OEMs) and system builders are required to disable the account before handing the system over to customers.
However, in upgrade installations, the account remains enabled unless there is an active local administrator on the computer and when the computer is not part of a domain. In such a scenario, the following methods can be used to disable the built-in administrator account:
- Run the sysprep/generalize command. By running this command, the built-in administrator account gets disabled automatically the next time the computer restarts.
- Use the net user command. The command can be run after the computer is configured and before it is delivered to the user. The command syntax is net user administrator /active:no.
Best practices for managing a built-in administrator account
To reduce the computer's attack surface and minimize the possibility of a cyber attack, follow these best practices to manage a built-in administrator account:
- Disable it during normal operations.
The built-in administrator account is meant for setup and disaster recovery only. The account is useful for OEM system builders who may need to modify the system before the OOBE experience is complete and for system troubleshooters who may need it for system recovery. Typically, end users have no other reason to enable or use the account, so it should not be used during normal operations.
- Secure the account with a unique password.
If the admin accounts on all systems are not secured with unique and different passwords, a security issue in one system can affect all the systems in the IT ecosystem. For this reason, every system must have a unique local administrator password. In addition, the password should be long --127 characters or longer.
- Avoid sharing and renaming the account.
The built-in administrator account should never be shared or renamed. Sharing reduces accountability, which can be a big problem in the event of a cyber attack and subsequent investigations. Renaming accounts to fool would-be attackers also doesn't work, since knowledgeable attackers can still identify such accounts to manipulate their access privileges.
So, instead of wasting time on renaming the administrator account, it's better to disable it entirely and install other protection tools to secure the computer and its network.
See also: five system administrator skills Windows admins should hone, Windows Admin Center brings server management under one roof, how to locate privileged accounts in Active Directory, determine the right level of data center access for administrators and how to configure folder redirection works with roaming profiles.






