What is a password?
A password is a string of characters used to verify the identity of a user during the authentication process. Passwords are typically used in tandem with a username; they are designed to be known only to the user and allow that user to gain access to a device, application or website.
Anatomy of a password
Passwords can vary in length and can contain different letters, numbers, special characters, or some combination of letters, numbers and special characters. Passwords that combine letters, numbers and special characters as opposed to only letters or only numbers are considered stronger and therefore less susceptible to theft and compromise.
For example, "santaclaus," "password" and "12345678" are all considered weak passwords since they are easy to guess and commonly used, and therefore easy to break. In fact, cybercriminals frequently use methods like dictionary attacks, rainbow table attacks, brute-force attacks and credential stuffing to steal such simple passwords and gain access to the accounts they are meant to protect.
In contrast, "Mandal#orian@1980!!" and "U&see#me!2024" are considered strong passwords since they are not easy to guess and therefore harder to break.
The stronger a password, the better it can protect an account and its user, which means the account and user are less likely to be compromised by an unauthorized or malicious user, such as a hacker or cybercriminal. This is why modern applications and security experts all suggest that users create strong passwords for their online accounts and digital devices.
Challenge-response authentication and passwords
Challenge-response authentication is a security mechanism in digital communications in which one party, the user, sends a response to a challenge or question issued by the other party, such as a server. The user must provide the correct answer to authenticate themselves and convince the server that they are who they say are. Once performed, the server verifies the types, number and order of characters provided to confirm the user's identity. When this authentication process is complete, the server grants the user access to the password-protected system.
It is expected that the authorized user will be the only one who knows the exact password. For a password to be an effective security mechanism, its details must be kept secret. Otherwise, unauthorized users could gain access to the files that the password and user are trying to protect.
Apart from passwords, other examples of challenge-response authentication mechanisms include the following:
- CAPTCHA codes.
- Biometrics.
- Secure Shell.
- Time-based one-time passwords.
- OATH Challenge-Response Algorithm.
- Challenge-Handshake Authentication Protocol.
How to create a secure password
Passwords, when carefully created and protected, facilitate safe and secure interactions online and in the workplace. Strong passwords are hard to crack or harder to "read" by unauthorized persons or threat actors.
To maximize the strength and efficacy of passwords, organizations often establish password policies. These policies are designed to help users create strong passwords and adopt best practices for managing login credentials and keep them safe from theft and compromise.
Following are a few examples of the practices that help users create strong passwords:
- A minimum length of eight characters and a maximum between 16 to 64 characters. While there is no limit to the length of a password, it does reach a point of diminishing returns from a security standpoint. Generally, a password that's complex and at least eight to 10 characters long is considered stronger than a password that's less complex but 30 characters long.
- Include both uppercase and lowercase letters with case sensitivity. A mix of cases increases the password's complexity.
- Use at least one number.
- Use at least one special character.
- Avoid using easily guessed elements such as names of children, pet names and birthdays.
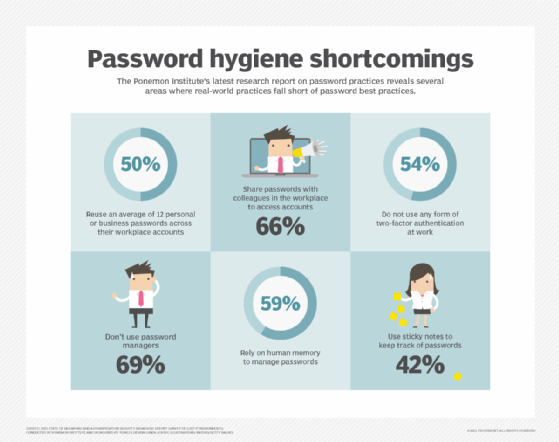
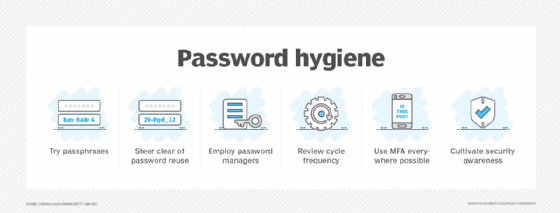
Many websites and online tools require users to frequently change passwords, avoid reusing old passwords, avoid sharing passwords with others and avoid writing down passwords where they can be intercepted or stolen. Using a password manager helps users create strong passwords and keep them secure. Finally, a security best practice advises to never store passwords in encrypted locations like text files or Excel files.
Examples of strong passwords
The most important components of strong passwords include sufficient length and a mix of character types. Security experts recommend using passwords or passphrases that combine several words and interchange numbers and symbols but are still easy to remember.
For example, the phrase "my hobby is buying shoes online" can be converted to "Myho88y!$ buYing$HO3$0nlin3" to increase its complexity and to reduce its susceptibility to cracking and theft.
Security practitioners also recommend using the first letter of each word in a long sentence to create a complex string, and again, replace some letters with numbers and symbols.
For example, instead of the phrase "I spend all my money in the shoe department at Nordstrom because their shoes are great," a user can use "I$@MM1TSD@N8T$AG." To the user, this jumbled phrase would likely make perfect sense and be easy to remember -- and difficult for a hacker to guess.
Random password generators and password management tools can also produce complex passwords and remember them, so users don't have to. Despite vulnerabilities that sometimes surface in password managers, the security community recommends their use as part of a broader security strategy.
How to avoid weak passwords
Users and businesses should strive to eliminate common password vulnerabilities that threat actors tend to look for. Persistent cybercriminals can easily obtain simple passwords, commonly used passwords and passwords containing recognizable personal information to achieve the following:
- Gain unauthorized access to a user's digital resources.
- Execute a data breach.
- Execute account takeover attacks.
- Steal individuals' identities (identity theft).
- Steal a person's or organization's funds or intellectual property.
Common password weaknesses include the following:
- Use of the word "password" as the password.
- Using sequential numbers starting from one, such as "12345678".
- Inclusion of accessible information: birthdates, names of relatives, home addresses and names of pets or children.
One well-known example of the devastating consequences of using weak passwords is the SolarWinds hack of late 2020. This attack, which resulted from the hackers simply guessing the password of the company's update server ("solarwinds123"), shows how cybercriminals can compromise weak passwords to create havoc. Once they cracked the password, they were able to hide a virus in SolarWinds' Orion software update, which was later shipped to its clients and ended up compromising them as well.
How often should passwords be changed?
The process of regularly changing passwords is also known as password resetting or password rotation. Password rotation is another recommended security practice.
While there's no hard and fast rule about how frequently passwords should change, corporate password policies often place an expiration date on their users' passcodes. These policies mandate users to replace old passwords with new ones after a certain time period has elapsed -- generally 90 to 180 days.
Some policies also force users to create new passwords that don't share major similarities to previous iterations. For example, if a password created on January 1 2024 was "!loveLucy#1968," a password to the same account that's changed March 1 2024 cannot be "Lucy@Rocks@1969" since it is too similar to the previous password.
That said, manually changing passwords for multiple accounts can be a hassle for users. Password managers can reduce the hassle by securely creating, storing and managing all passwords, thus eliminating the need for users to manage these activities. Additionally, they generate strong, random passwords, increasing password complexity and therefore security.
Passphrases vs. passwords and passkeys vs. passwords
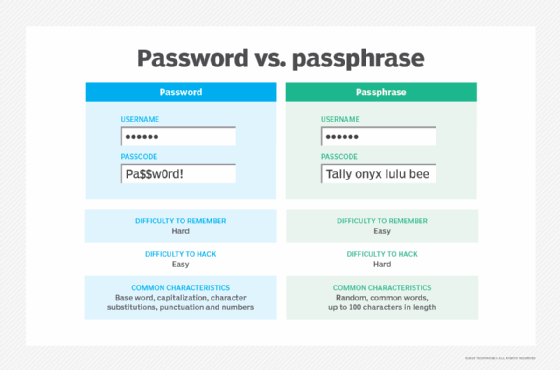
A password is sometimes called a passphrase when it uses more than one word. However, a password is not the same as a passphrase. Where a password is a short string of characters, a passphrase is a combination of words or even an entire sentence.
Passphrases are longer and often more complex than passwords, however, users often find it easier to remember passphrases.
For example, a password like "Comedy$2024@haha123" is strong but hard to remember. However, a passphrase like "$einfeld!sc0me$yG0ld" can be easier to remember because it is creative and has some appeal for the user.
Many tools and sites are available to help users generate strong passphrases that are memorable to them but hard to guess for others.
When the password uses only numbers, such as a personal identification number (PIN), it is known as a passcode or passkey. But the terms password and passkey are not strictly synonyms. A passkey is an authentication method that eliminates the need for passwords. Many sites, browsers and platforms allow users to use passkeys, such as their fingerprints, face scans or a PIN instead of passwords to securely log in. Passkeys are considered more secure than passwords because they can only exist on user devices (desktops, laptops, phones, hardware security keys, etc.) and therefore cannot be given to or stolen by an unauthorized party.
What is password management?
Password management refers to the systematic practice of creating, storing, managing and accessing passwords, while enforcing best practices in all these areas. Increasingly, many individuals and organizations use password managers.
A password manager application generates complex passwords for multiple accounts, thus helping to increase online security for the account and its user. Password managers also securely store all passwords in a password vault, or an encrypted location protected by a single master password. Encryption helps to safeguard passwords from cracking and theft.
Additionally, the master password eliminates the need for the user to remember the individual passwords for each website or app that they use. To use these resources, they only need to remember the master password. Once they provide the master password, the password manager facilitates access to different accounts.
Alternative methods to passwords
Passwordless authentication has emerged to help eliminate the complexities and vulnerabilities of traditional passwords. This method is especially beneficial for use on mobile devices or social platforms. Instead of creating a unique password, users receive a one-time authentication code via a text message, email or other messaging alert or service. The code allows them to log in automatically without having to remember, change, store or manage complex passwords.
Other authentication methods can also be combined with passwords or used in place of passwords. These are some options available:
- Two-factor authentication. The 2FA option requires users to provide two authentication factors that include a combination of something the user knows (like a password or PIN), something the user has (like an ID card, security token or smartphone) and something the user is (like a fingerprint or eye scan).
- Multifactor authentication. MFA is similar to 2FA except that it requires users to provide more than two authentication factors. Adding authentication factors provides more security because hackers will need to guess all those factors in order to compromise an account.
- Biometrics. Biometric methods authenticate users based on physiological characteristics such as fingerprints or retinal scans, or behavioral characteristics such as typing patterns and voice recognition.
- Tokens. A security token is a physical hardware device like a smart card or key fob that a user carries to authorize access to a network.
- One-time passwords. An OTP is an automatically generated password that only authenticates a user for a single transaction or session. These passwords change for every use and are typically generated by security tokens or are automatically sent by the system to the user's device via email or text message.
- Social login. This method enables users to authenticate themselves on applications or websites by connecting to a social media account such as Facebook instead of having to log in separately to each site or app.
Learn more about the differences between passwords and passkeys to see why passkeys make it more difficult for thieves to steal data while being more convenient for users. Read more about the different types of cyberattacks that involve password theft or compromise.







