dictionary attack
What is a dictionary attack?
A dictionary attack is a method of breaking into a password-protected computer, network or other IT resource by systematically entering every word in a dictionary, or word list, as a password. A dictionary attack can also be used in an attempt to find the key necessary to decrypt an encrypted message or document.
Dictionary attacks work because many computer users and businesses insist on using ordinary words as passwords. Modern dictionary attacks use a wordlist as a base then try combinations of words and permutations with common substitutions, such as replacing an "e" with a "3." These tools can even find unique passwords if they are simple enough.
In systems with strong password requirements, the brute-force method of attack, in which every possible combination of characters and spaces is tested up to a certain maximum length, can sometimes be effective. However, a brute-force attack can take a long time to produce results.
Strong, randomized passwords consisting of random characters and symbols are the strongest type of password. They cannot be easily predicted, and they are highly unlikely to be included in the predetermined password library. Because a dictionary attack's guess attempts are limited to a preselected list, it is essentially impossible to use one to crack nonpredictable passwords.
How do dictionary attacks work?
A dictionary attack uses a preselected library of words and phrases to guess possible passwords. It operates under the assumption that users tend to pull from a basic list of passwords, such as "password," "123abc" and "123456."
These lists include predictable patterns that can vary by region. For example, hackers looking to launch a dictionary attack on a New York-based group of targets might look to test phrases like "knicksfan2020" or "newyorkknicks1234." Attackers incorporate words related to sports teams, monuments, cities, addresses and other regionally specific items when building their attack library dictionaries. Many dictionary attack word lists now incorporate leaked passwords to reflect actual passwords that people use.
These word lists aren't as extensive as a character-based brute-force attack, but they can become quite large. Processing and testing all these passwords manually or one by one is not a practical approach. Therefore, additional technology is typically required to speed up the process. Attackers use supporting programs, such as password dictionaries or other brute-force attack tools. Modern programs based on graphics processing units can try millions of passwords per second.
How dictionary attacks are conducted depends on whether the account, network or device the attacker is logging into is online or offline. In an online attack, the attacker must be mindful of the number of attempts they can use to guess the correct password. Past a certain number of tries, a site administrator, account manager, user or intrusion detection system might detect the attack, or a password attempt limit might come into play. If any of those scenarios happen, the system can lock the attacker out.
Dictionary attacks with a shorter prioritized list of likely passwords can be more successful. Sophisticated hackers might also be able to disable the detection features or password attempt limits.
For offline attacks, a hacker has few restrictions when it comes to the number of passwords they can try or the length of time they can spend. However, executing an offline attack requires access to the password storage file from the system, the password hash. Only then can a dictionary attack be launched in an offline setting. Offline attacks can be used against file-based encryption, such as password protected PDFs, zip files or offline email caches.
Find out more about the passwordless authentication method
Passwordless authentication options and best practices
How to start implementing passwordless authentication today
Passwordless authentication issues to address before adoption
Multifactor authentication isn't perfect, passwordless is better
Is a passwordless future getting closer to reality?
When will we finally ditch passwords? Here's Microsoft's 4-step plan
Brute-force attack vs. dictionary attack
A dictionary attack is considered a type of brute-force attack. In common use though a brute-force attack will use a systematic approach to try all possible passwords. In everyday usage, the main difference between a brute-force attack and a dictionary attack is the number of password permutations that are attempted and the use of a word list.
Brute-force attacks
A brute-force attack will try every possible character combination. This can take a significant amount of time to complete. For example, it might start with the password "a" then change one letter at a time until it gets to "zzzzzzzz."
A five-digit combination lock provides a familiar example of the difference. Using a brute-force approach, an attacker would attempt every possible permutation available for the five-digit lock. A five-digit lock with individual values from zero to nine has exactly 100,000 possible permutations. A dictionary attack might start by trying the owner's birthday, house number, or simple patterns like 11111 or 12345.
Dictionary attacks
A dictionary attack will use a list of likely passwords in its attempts to break into a system. These attacks are more focused than brute-force attacks. Rather than trying to input every possible permutation, an attacker using a dictionary approach would attempt all the permutations in its predetermined library.
Sequential passcodes, like "12345," and static passcodes, like "00000," would be tested. If the five-digit permutation is particularly unique, the dictionary attack likely would not guess it. Like phishing attacks, dictionary attacks assume that a reasonable percentage of the users or accounts they target will be vulnerable and will have an easily identifiable five-digit passcode.
How to protect yourself against a dictionary attack
Users should select long unique passwords. Passwords consisting of completely random characters should be of at least 10 characters, with 14 being more future-proof. Using a passphrase with four to six random words offers similar protection but is easier for the average user to remember.
To understand why passphrases can be better than passwords, it's helpful to consider the total entropy or randomness in any given password. A simple password of eight lowercase characters means 26^8 combinations, or approx. 2*10^11. Eight characters including uppercase, lowercase, numbers and symbols (considering 95 possible characters in the printable ASCII set on a standard English keyboard) is 95^8 combinations, or 6*10^15. An English dictionary might have 100,000 to 300,000 words, selecting four at random would be 10^20 possible combinations, 100,000 times more complex than eight random characters, and much easier to remember. Passwords of 10 random characters and four-word passphrases are about equivalent in total complexity.
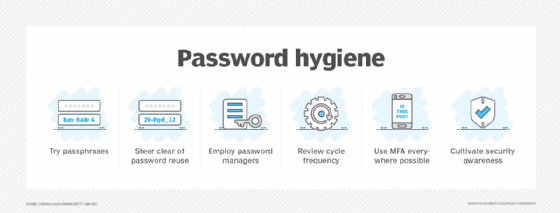
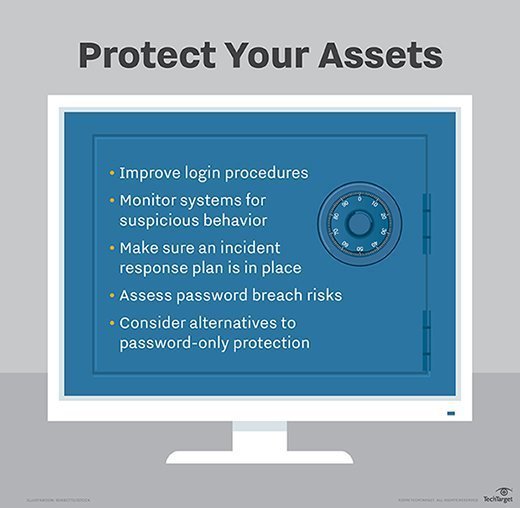
System administrators can limit vulnerability to brute-force attacks or decryption key assaults to near-zero by limiting the number of attempts allowed within a given period and by wisely choosing passwords or keys. An approach that will render a system immune to dictionary attacks and practically immune to brute-force attacks requires the following three conditions:
- Allows only three password attempts.
- Requires 15 minutes to elapse before the next three attempts are allowed.
- The password or key is a long, meaningless jumble of letters, numerals and special symbols.
The National Institute of Standards and Technology authentication guidelines recommend that no more than 100 incorrect password attempts be allowed before the account is locked.
Passkeys are a modern authentication method that seeks to replace passwords to protect against brute-force and dictionary attacks. With passkeys, the server and client exchange a public/private RSA key pair eliminating a stored password from the server. On the user's device, the passkey is protected by an unlock gesture. If an attacker gains control of a user's device and the passkey is protected by a password, they might be able to attack the device with a dictionary attack to unlock the passkey. This type of targeted attack is much more difficult for an attacker to achieve than against a regular password protected service.
Email spammers often use a form of dictionary attack. A message is sent to email addresses consisting of words or names, followed by the @ symbol and the name of a particular domain. Long lists of given names -- such as Frank, George, Judith or Donna -- or individual letters of the alphabet followed by surnames -- such as "csmith," "jwilson" or "pthomas" -- in combination with a domain name, are usually successful.
How effective is a dictionary attack?
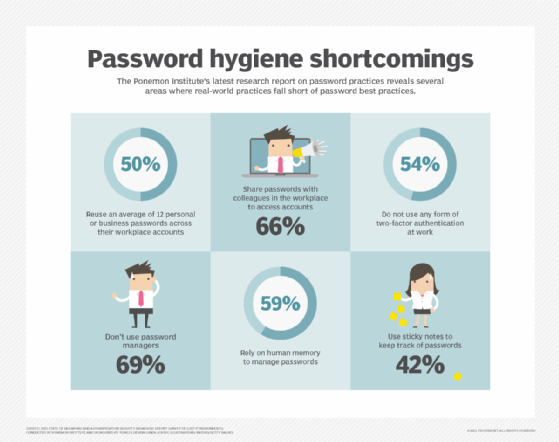
How successful a dictionary attack is depends on how strong the passwords are for the individuals a hacker is targeting. Because weak passwords are still common and users will often reuse passwords, attackers continue to have success with these attacks. Individual users, however, aren't the only ones who are subject to weak password security.
The massive SolarWinds data breach was executed using a dictionary attack. Russian-backed hackers were able to log in to SolarWinds' update server by correctly guessing the administrator password, "solarwinds123," and then planting a backdoor that was activated when SolarWinds customers updated their software.
As long as passwords remain simple and predictable, dictionary attacks will be effective. NordPass ranked the top 200 passwords in order of popularity for 2020. The highest-ranked password, with 2,543,285 occurrences, was "123456." Other high-ranking passwords in the top 10 included "picture1" and "password." Lists like this that are published or leaked are incorporated into the password libraries that dictionary attackers use.
Learn more about the latest thinking on password length and security.







