How to create a company password policy, with template
Use these guidelines and our free template to ensure your company's password policy sets the ground rules for strong and effective password creation and use.
Passwords are one of the first lines of defense in enterprises, authenticating users to access critical accounts and data. As such, choosing strong passwords and maintaining their safety are paramount.
A well-defined password policy enables companies to lay out password security best practices and recommendations, while ensuring users understand password requirements and their role in keeping companies safe.
Learn more about what a password policy is, why one is critical to enterprise security and how to write a policy customized to your company's needs.
What is a password policy?
Password policies establish rules for password administration, penalties for violation of password rules, procedures for addressing access attempts using invalid passwords and other security-related activities. The level of detail in a password policy can range from simple, such as the minimum required characteristics of a password, to a more detailed policy reflective of an enterprise-wide security program.
Senior management should approve the password policy and review and update it periodically to reflect new business activities. During M&A, for example, the companies involved likely have different security protocols, so upgrade the existing policies to align them.
Why do companies need a password policy?
Passwords historically have been a weak point for companies. The "2023 Verizon Data Breach Investigations Report" found 49% of data breaches involved stolen credentials. To prevent password-related breaches, it is important to ensure users create strong passwords and follow password rules and recommendations.
An enterprise-wide password policy sets the rules for password administration and provides guidelines for compliance. It's also an essential piece of evidence during audits and a key part of an organization's security activities and programs.
Components of a password policy
The template included in this article provides the foundation for preparing a password policy. The level of detail is up to the IT department and C-level management.
A password policy should, at minimum, include the following sections:
- Purpose and scope.
- A set of definitions relevant to passwords.
- A description of employees' roles in administering the password policy.
- Procedures on how to create a password.
- Password administration activities.
- Password resetting.
- Procedures for misused passwords.
- Penalties for unauthorized password activities.
The policy should include a section to track changes, updates and approvals.
How to prepare a password policy
In addition to the items listed above, consider the following when developing a strong but user-friendly password policy:
- Consider the use of one-time passwords (OTPs).
- Use password management software to help users create, encrypt, store and update passwords.
- Establish a password team within the security team.
- Consider using bring your own identity technology to minimize the number of passwords needed.
- Consider using single sign-on to reduce required access steps for different systems.
- Consider using the password policy as part of an identity and access management program.
- Establish a security breach management procedure.
- Provide periodic password awareness, education and training activities to all employees.
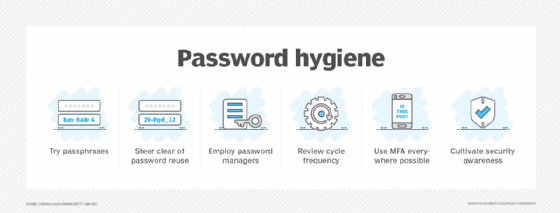
Password policy best practices
When developing a password policy, consider the following best practices:
- Implement multifactor authentication. Require users add more authentication factors when logging in to accounts, whether it's an OTP, authentication app or biometrics.
- Require a minimum character length and complexity. Set minimum length and complexity requirements when users create a new password, including requiring them to use special characters.
- Check passwords against commonly used ones and those found in data breaches. When users attempt to create a new password, check it against commonly used passwords and through a system such as Have I Been Pwned.
- Don't use default admin passwords. Require admins to change passwords upon logging in to admin accounts for the first time.
- Don't rely on password rotation based on age. Previous guidance suggested organizations require passwords changes every 60, 90 or 120 days. This often leads to users changing Password1 to Password 2, however. Consider the best password change cycle for your organization, weighing the benefits and users' tendency to choose weak passwords. As always, require users to change passwords after a suspected breach.
How to use the password policy template
This template is a framework for preparing a password policy. Use as much of the suggested content as needed. Incorporate any existing policy content, and add content that is appropriate for your organization.
Have the drafted policy reviewed by a subject matter expert, and update the policy as needed before submitting for C-level approval. It's helpful to have a lawyer review the policy, as well as risk management and HR.
Once approved, advise employees on the policy. Train help desk staff to answer questions, especially regarding policy implementation and enforcement.
As with any policy, be sure to review and update it periodically to maintain its relevance and effectiveness.








