
Passkey vs. password: What is the difference?
Companies are turning to passkeys as a secure login for consumers. Passkeys make it more difficult for thieves to steal information, and they are also more convenient for users.
Passwords might be a thing of the past as tech giants move to new passkey technology -- a passwordless login that is more secure and convenient.
Passwords require users to remember a string of characters to sign in -- which can be an inconvenience to users who must remember several passwords -- and can result in security issues such as breaches, phishing and stolen identities. Passkeys rely on biometric authentication, a PIN or pattern to authenticate a user's ability to sign onto a device, which reduces data breaches and other security vulnerabilities.
The move to a passwordless future is underway, with Apple and Google updating their phone software and web browsers to use passkey technology. Let's review some key differences between passkeys and passwords to help prepare for this change.
What is a passkey?
Passkeys are a new type of login credential that removes the need for passwords. The authentication requires either biometric authentication -- such as a fingerprint or facial recognition -- or a PIN or swipe pattern used with Androids for access.
The passkey works on a person's device, so users can't use passkey functions on another device without a QR code. Users can scan the QR code from their phone and use their Face ID or Touch ID to sign in from another nearby device.
Passkeys were created with the Web Authentication API security standard that uses public key cryptography for access. Each key is unique and created with encrypted data for added security -- think of a digital version of a keycard.
What is a password?
A password uses a string of characters for identification during sign-on. They are typically used together with a username. Passwords should be unique and only known to the user.
Passwords can vary in length and can also contain special characters, letters and numbers. To protect data, businesses should implement password policies, including guidelines for strong passwords and a timeframe for updating them regularly.
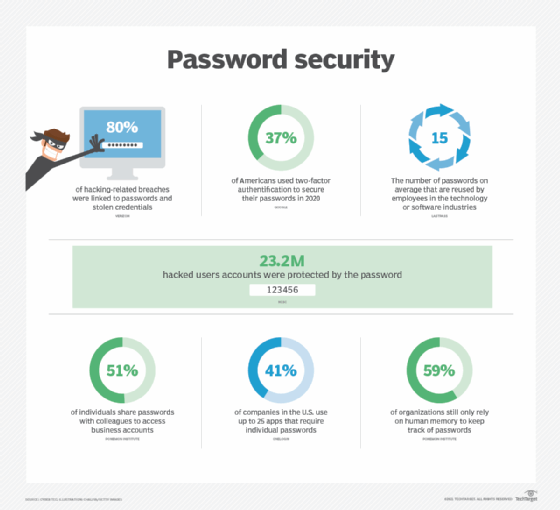
One of the main problems with passwords is remembering multiple passwords and not reusing them. Reusing passwords can present security issues because once bad actors get one password, they can access various accounts using the same credentials.
To help remember multiple passwords, users turn to password managers, which use one master password or key to pull the correct password from a database to authenticate the login for the website or application. After entering the main login, the password manager will fill in the form to log the user in so they don't have to remember multiple passwords. Having a password manager might help users remember passwords, but they are not completely secure if the master password is stolen.
Learn more about password hygiene practices.
How does a passkey work?
Passkeys use Bluetooth technology, which requires physical proximity, to help verify the user.
After signing in and linking accounts, a push notification is sent to the device through Bluetooth. The user then needs to unlock their device with their private key -- which is either a biometric authentication or PIN -- to create a unique public key that relates to the login. At the next login, the user will only have to use the chosen credential when prompted, which is their private identification with no password to remember. The passkey option will appear by the username field.
Google's Chrome password and Apple's iCloud Keychain synchronize passkeys across multiple devices through the cloud. When adding a new device, the user will have to sync it up to use passkey technology.
How are passkeys more secure than passwords?
Passwords are the current standard for sign on, but they aren't the perfect standard. First, people must remember their passwords, which can be a hassle if there are multiple passwords. Users must also create a complex password to avoid password cracking. Here are additional reasons why passkeys are a more secure option than passwords.
- Passkeys cannot be stolen as easily as passwords because data is stored on a device and not a web server. Bad actors can use phishing scams to trick people into sharing passwords on fraudulent websites, making them vulnerable to cyberattacks and data breaches.
- Passkeys require bad actors to access the device and the fingerprint, facial ID or PIN to unlock it. A bad actor would also have to be near a person's device to use Bluetooth. If someone loses a device, the thief will be unable to access information without biometric authentication.
- Each passkey is unique and created using a strong encryption algorithm. The user doesn't have to worry about weak passwords that can be guessed.
- People typically choose the same password for multiple sign-on and sites. If a bad actor learns the password, they could get access to multiple accounts. Weak passwords create vulnerabilities to both the user and business.
Why are companies moving to passwordless authentication?
Passkeys might be easier to use than passwords and safer for companies to help avoid breaches. Apple, Google and Microsoft have worked with the FIDO Alliance and the World Wide Web Consortium (W3C) to ensure passkeys are implemented in ways that work across multiple platforms. Passkeys are the newest technology developed by the FIDO Alliance.
Password-only authentication is a big security problem and can be inconvenient for consumers, according to the FIDO Alliance. When consumers reuse passwords, there is a bigger risk for data breaches and stolen identities. Even with password managers and two-factor authentication, passwords can still be stolen because they are stored online. The initiatives from the FIDO Alliance and W3C are an industrywide collaboration to make sign-on technology more user-friendly and safer.
Users won't be forced to use passkey technology, but more websites and apps will start offering passkeys as an option. The FIDO Alliance reports passkey adoption is growing as people choose this method over passwords to secure their online accounts and apps.
Editor's note: This article was updated in December 2024 to improve the reader experience.
Amanda Hetler is a senior editor and writer for WhatIs where she writes technology explainer articles and works with freelancers.







