
How effective is security awareness training? Not enough
Annual security awareness trainings do little to improve security. Learn why they aren't helpful, and discover steps to improve your organization's training program.
Organizations can adopt all the security technologies they want, but the truth is they are only as secure as their weakest link: people.
Insider threats account for up to 60% of all data breaches by some accounts, with negligent insiders causing 56% of insider threat incidents in 2021, according to the "2022 Ponemon Cost of Insider Threats Global Report." Negligent insiders include employees using insecure devices, ignoring or disobeying security policies, and not patching or upgrading software and devices. The other insider threats were caused by malicious actors (26%) and user credential theft (18%).
"Cybercriminals are experts at social engineering and tricking employees into clicking on malicious links that initiate attacks," said William Candrick, director analyst at Gartner. "While security professionals know that social engineering is a top risk, many still struggle to stop employees from being fooled."
Organizations often rely on cybersecurity awareness training to combat and prevent negligent and malicious insider threats. The effectiveness and efficacy of these trainings, however, is often called into question as it becomes increasingly clear that many cybersecurity awareness trainings don't achieve their intended result.
Why aren't cybersecurity awareness trainings effective?
Many organizations conduct security awareness trainings on an annual basis. While these trainings are intended to reduce risk and improve security, too often they are conducted to check a box to comply with standards and regulations, such as NIST 800-53, ISO/IEC 27002 and GDPR, or to fulfill stipulations within cybersecurity insurance coverage.
"A once-a-year training module isn't going to move the risk needle," Candrick said, adding that such an approach does little to change employee behavior.
Simply put, employees struggle to retain and apply what they learn in sporadic trainings to their everyday work lives. Further, most trainings contain outdated, mundane and disengaging presentations, and they are often not specific enough to employees' individual roles within their organization.
Johna Till Johnson, CEO and founder of Nemertes Research, agreed. "It's like learning a language and never practicing it," she said.
These viewpoints align with the results of a Usenix report on the effectiveness of phishing awareness trainings. Participants were asked to identify malicious emails at different intervals after a security awareness training, ranging from before to directly after and four, six, eight and 12 months after. Rates of recognition were high at the fourth month, but response rates significantly decreased after six months, suggesting security awareness trainings are most effective when conducted two to three times per year.
How to improve cybersecurity trainings
Despite their pitfalls, cybersecurity awareness trainings aren't going anywhere.
"Security awareness training is the most public-facing thing a security team does within an organization," said Jinan Budge, principal analyst at Forrester Research. "If you perpetuate this image of security as boring -- people in hoodies and locks and keys -- you're going to further alienate people."
But in order for security awareness trainings to be informative and stick with employees after the training session is over, it is important for organizations to shift away from compliance-based trainings to focus on human behaviors and culture.
"We encourage clients to measure behavior outcome metrics rather than activity metrics," Candrick said. Activity metrics, such as the number of phishing simulations or training modules completed each year, can't measure employees' level of understanding. However, behavior outcomes -- such as click and report rates on phishing simulations -- offer insight into the success of an organization's security awareness program and where improvements can be made.
Behavior metrics guide human risk quantification models -- processes that help security teams identify gaps between knowledge and behaviors and calculate the potential risk of certain actions to an organization's cybersecurity posture. Ultimately, organizations mitigate risk by reducing risky actions, such as employees not using password managers or bypassing data loss prevention software.
Human risk quantification models are increasing in popularity, Budge said. Some organizations have started using risk quantification models to identify risky behavior and flag employees who perform insecure actions. Flagged employees can then be prompted to complete an automated on-the-spot training. Unlike broad annual trainings, these trainings are short, individualized and based on the specific circumstance.
Beyond automated trainings, moving forward, security automation tools and analytics will continue to shape cybersecurity risk prevention and awareness practices.
"If the process makes sense and the automation is there, you don't need the training," Johnson said. "Banks could have spent hundreds of millions of dollars training people not to leave their card in ATMs, but instead they changed the machines so people have to take their cards before they can get cash."
Organizations can adopt a similar approach to security. If a company doesn't allow its employees to use thumb drives, for example, it could use a script that automatically rejects or disconnects unapproved devices from its machines.
Despite automated guardrails, it's still employees' responsibility to help protect their organization. Many employees, however, don't understand how their roles or duties affect the organization's cybersecurity posture.
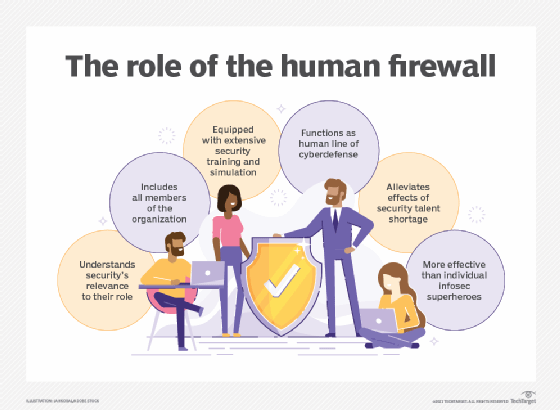
Human firewalls help fill this gap. A human firewall training program includes specialized exercises that teach employees security that is specific to their roles and daily routines. Human firewall trainings should also hold employees accountable using metrics and incentives.
Security culture mapping can also help make trainings more personalized and engaging, Budge said. This technique involves sending out a broad survey to all employees with an array of questions, including the following: What are your feelings toward security? How likely are you to engage with the security team? How likely are you to adopt certain policies? Security teams can use the survey results to target specific teams, people and departments.
gamification and creating quality security awareness videos that use puppets or anime can further engage employees in the training, Budge said.
Johnson also said to expect an uptick in the use of war gaming and real-world response scenarios in the next few years.
Annual cybersecurity trainings aren't effective, but don't write off awareness trainings altogether. "Companies must design more frequent, shorter and multichannel engagement to teach and reinforce good behavior," Candrick said.








