
ashumskiy - Fotolia
Design a human firewall training program in 5 steps
Follow these five steps to develop human firewall training that's not only effective at preventing social engineering attacks, but also relevant and accessible to employees.
The proliferation of cybersecurity breaches is forcing government and business leaders to analyze the limitations of technology and reevaluate the role of people.
Despite incredible advances in both threat mitigation and penetration testing techniques, studies have found human error remains the weakest link in cybersecurity fortification. Phishing, in particular, accounts for an estimated 90% of attacks on business networks. As bad actors conduct more sophisticated social engineering attacks and increasingly prey on people's vulnerabilities and fears -- especially regarding the COVID-19 pandemic -- investing in the human side of security is as important as the IT side.
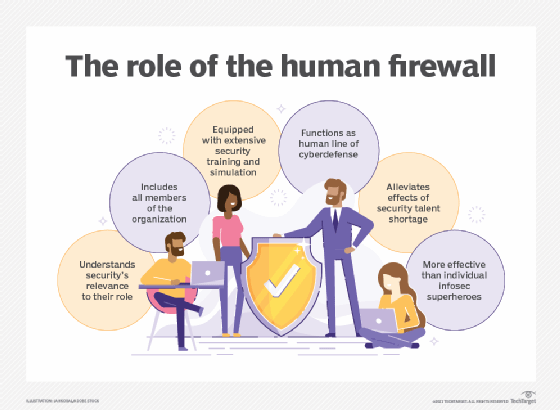
From IT firewall to human firewall
To mitigate the human element of risk, security leaders need to translate IT concepts into analogous ways of thinking. Organizations have long deployed firewalls around their technical assets. Now, they must apply this same principle to people to build a human firewall -- a line of defense composed of people who combat threats to the organization to which they belong. This human layer of protection is a mindset empowered through education and incentives, spanning teams, business functions and technologies across the entire organization.
Best practices for human firewall training
Culture is rarely easy to shift, particularly in large organizations. Unlike technical firewalls, configuring a human firewall requires changes to the organization's security culture. Part of that includes shifting peoples' mindsets and behaviors.
Here are five strategic best practices security leaders can take to ensure successful human firewall training.
1. Leadership must lead by example
Executives and senior leaders are key to communicating the strategic context for behavioral change. They are also instrumental to endorsing shifts in security practices by connecting specific divisions within the company directly to investments and integration. Leaders should:
- prioritize security training and organization-wide employee resources as equal to security technology investments;
- incorporate security posture and resourcing into adjacent strategic pillars, including HR, product and marketing; and
- identify cultural barriers to security-mindedness and practices, as these likely exist across different teams.
2. Ongoing education and adaptation are essential
Cybersecurity threats and vulnerabilities are not obvious to most people. But, because social engineering and human error account for the majority of breaches, building awareness within organizations and across teams is as critical a foundation for defense as technology. Human firewall training must be comprehensive yet simple to understand -- concrete yet ongoing. This education should:
- develop the context for employees by being transparent about the risks, implications and cascading effects of bad security hygiene;
- illustrate threat landscapes, not only across proprietary assets, but also across third-party vendors and remote working tools;
- design educational curricula to go beyond PowerPoints, password tips and annual pass/fail exams by including updated, relevant examples or tutorials; and
- ensure clarity of feedback mechanisms to improve security culture, processes and tools.
3. Identify cross-functional liaisons
Given the diversity of threats, endpoints and vulnerabilities, companies must recruit a multidisciplinary task force dedicated to fortifying the organization. It's equally important for employees to feel welcome at and empowered by human firewall training, rather than intimidated. Cross-functional liaisons should help:
- identify risks and opportunities;
- bridge security priorities across different groups, such as IT/operational technology or sales and support;
- incorporate learnings into ongoing education curriculum development;
- assess areas of redundancy or gaps in tools and vendor products and services;
- develop specific safeguards to be deployed across business functions, teams and products; and
- analyze the ecosystem for industry- or product-specific security practices and translate those to their teams.
4. Make it relevant and accountable
Developing a human firewall is an inclusive exercise; after all, an organization's security is only as strong as its weakest link. But it must also be tailored to different roles and needs. It is crucial employees understand how their roles and behaviors can help or hinder the overall security structure of the organization, as well as their specific responsibilities to mitigate risks. This includes developing cybersecurity procedures that integrate into their daily work routines and procedures, rather than asking for more cumbersome or radical behavioral changes.
Metrics are also key. Use metrics to demonstrate the value proposition to leadership for continued investment, as well as incentivize employees to continually improve. Consider the following measures to make human firewall training more relevant to employees:
- experiment with learning tools and training styles to personalize content;
- integrate scenarios that will resonate, such as steps to take before releasing code for developers, pertinent issue resolutions for support staff or areas that exceed industry standards for sales teams;
- incorporate gaming, competitions or quick tests during and after training to monitor which modules resonated and what concrete behaviors stuck; and
- tie metrics to productivity enhancements or employee incentives to create opportunities for skills development.
5. Don't forget: Keep it human
The culture of an organization is about how people feel, including their beliefs, assumptions and general engagement with the company and its perceived values. For the security culture to improve, employees need to feel comfortable making mistakes and confident when an incident occurs. Simply put, employees should feel positive about contributing to the cybersecurity resilience of the company. Here's how to accomplish this:
- center accessibility so people across different teams, geographies, languages, demographics and abilities are empowered and inspired to contribute;
- ensure learning modalities are fun, tell stories, encourage face-to-face interactions and incorporate several types of experiential learning, including games, simulations, role-playing and recognition; and
- address employees' technical and emotional vulnerabilities, which are exploited by malicious actors but are also opportunities to forge greater trust in the organization.








