How to build a cybersecurity culture across your business
As a company's cyber-risks evolve, so must its culture. Follow these tips to create a strong cybersecurity culture that helps protect your organization from cyberthreats.
Every organized group of people has a culture -- a combination of norms that guide them, structured roles they fill and common practices and tools they use to play their roles. Well-managed companies have an overall corporate culture and specific ones in key business areas, including cybersecurity. A cybersecurity culture is an organization's set of norms, roles, practices and tools focused on securing IT systems and business data.
Establishing a successful cybersecurity culture in an organization is crucial to protecting it against the ever-changing threat landscape. As cybersecurity challenges continue to evolve, so must efforts to combat them. A strong cybersecurity culture is essential to setting and implementing effective cybersecurity strategies, so building one should be a top priority for CISOs, CSOs and other security leaders. By investing in actions to develop an internal culture that supports cybersecurity initiatives, organizations can better protect networks, systems and data against cyberthreats and improve business resilience.
Why is a strong cybersecurity culture important?
The constant threat of sophisticated cyberattacks mandates a well-informed and proactive approach that starts with eradicating ignorance about security risks and the relationship between solid cybersecurity and business success. All employees must recognize the role they play in protecting the organization: Everyone is part of the threat surface, and everyone needs to be part of the defense against attacks.
For example, every employee needs to be aware of the dangers of phishing attacks and the possible repercussions of weak passwords and risky online behavior. Broad cybersecurity awareness and improved cyber hygiene among employees help fortify a company's digital defenses. By ingraining better security practices across the enterprise, a strong cybersecurity culture engenders an environment in which everyone, in every part of the organization, is an active participant in a holistic defense strategy.
Common challenges in building a cybersecurity culture
While most senior management teams today agree on the importance of effective cybersecurity, building a security culture companywide comes with challenges. The following are some of the primary hurdles:
- Lack of cybersecurity awareness and understanding. Many employees are unaware of how their actions can hurt or help the organization's security posture. As a result, they engage in potentially dangerous behaviors, like clicking on links in emails from unknown senders, using weak passwords for personal email accounts on their work devices or sharing sensitive information without following proper procedures. This complicates efforts to establish a comprehensive cybersecurity culture.
- Increased use of AI in the cybersecurity process. While AI and machine learning can help security teams detect and respond to cyberthreats more efficiently, the integration of AI into cybersecurity practices also presents challenges. These include the need for skilled personnel who understand both cybersecurity and AI, the risk of AI hallucinations that generate false positives or faulty recommendations in threat detection, and potential vulnerabilities in AI systems that attackers could exploit. Moreover, relying too heavily on AI can lead to complacency, where organizations might neglect essential aspects of reinforcing cybersecurity's importance, such as employee training.
- Business operations that don't see cybersecurity as their responsibility. Getting a security culture to permeate all levels of an organization is perhaps the biggest challenge. Because of cybersecurity's technical nature and increasing complexity, it's often seen as the sole responsibility of the IT department and cybersecurity team rather than a shared organizational responsibility. This can result in employees not committing to security best practices -- or worse, actively working around them whenever "doing it right" is perceived to require too much extra work or be too slow. Additionally, resistance to change, budget constraints and competing priorities can hinder efforts to make cybersecurity competency a key part of the organizational culture.
How to create a cybersecurity culture: 5 best practices
To overcome the challenges, leadership buy-in and support are essential. Board members, C-level executives and business managers must lead by example, demonstrating a commitment to cybersecurity in their actions and decisions. Here are five steps they can take in conjunction with security and IT teams to build an effective cybersecurity culture.
1. Promote a culture of responsibility and accountability
CISOs, CSOs and business leaders must foster an environment where every employee feels responsible for the organization's digital safety. This involves clearly communicating the role that each individual plays in cybersecurity efforts and establishing clear guidelines and protocols for reporting potential security incidents.
Leaders also need to encourage a sense of accountability, where employees understand the consequences of cybersecurity lapses and are motivated to adhere to security best practices. As part of that, recognizing and rewarding proactive cybersecurity behavior can reinforce the importance of vigilance and responsibility across the organization.
2. Create a culture of continuous learning through advanced security training
Given the dynamic nature of cyberthreats, building a cybersecurity culture necessitates an emphasis on continuous learning and adaptation. Advanced security training programs, tailored to the unique needs of different roles within an organization, are a must. These programs should go beyond basic security awareness training to include hands-on simulations, role-playing exercises and scenario-based training that mimics real-world attacks.
Security training that's relevant, informative and engaging encourages a growth mindset among employees, which helps foster a proactive view of cybersecurity. Such training can be augmented with AI and machine learning tools to provide personalized learning experiences, ensuring that all employees, regardless of their role, understand their part in safeguarding the organization.

3. Take advantage of AI to enhance threat detection and response capabilities
Despite the challenges listed above, AI can significantly transform how organizations approach cybersecurity. Its ability to analyze vast amounts of data at unprecedented speeds enables security teams to identify threats and anomalies that are impossible for humans to detect in a timely manner. Incorporating AI into cybersecurity strategies helps organizations become more adaptive and responsive to emerging threats.
AI-driven tools can also automate routine tasks, freeing cybersecurity professionals to focus on more complex security issues. Managed effectively, this efficiency not only enhances an organization's defensive capabilities but also seamlessly integrates into a culture of continuous improvement and innovation in cybersecurity practices.
A word of caution: While AI is advancing very quickly, we suggest focusing it more on threat detection and data filtering versus automatic actions such as server, network or power shutdown if it detects a possible cyberattack. AI is still best suited to eliminating hay from the cybersecurity haystack instead of finding and dealing with needles hidden there. Trained staff are still needed to supervise AI tools and interpret their results.
4. Encourage cross-departmental collaboration
Cybersecurity is a cross-functional concern that affects every aspect of an organization. Encouraging collaboration between departments can lead to a more holistic understanding and assessment of cybersecurity risks, along with a more cohesive defense strategy.
For example, regular meetings and workshops that bring together IT, security, business operations and executive leadership facilitate the sharing of insights and best practices. This collaborative approach ensures that cybersecurity considerations are integrated into all business decisions, from product development to marketing strategies.
5. Integrate security and network operations centers for a unified security posture
A security operations center (SOC) is the nerve center for cybersecurity initiatives, providing continuous monitoring and analysis of an organization's security posture. SOCs better enable organizations to detect, analyze and respond to security threats in real time. This proactive capability is essential in today's digital world, where threats evolve rapidly.
While a SOC focuses on identifying, assessing and responding to security incidents, a network operations center (NOC) manages networks and ensures the availability of IT infrastructure. Integrating SOCs and NOCs can be a complex process. They have historically distinct roles, and challenges often arise due to differences in tools, processes and objectives. But doing so creates a unified security posture and defense against cyberthreats.
Combining the functions of an organization's SOC and NOC can lead to improved communication, faster incident response and a better understanding of enterprise security issues. It ensures that both security and network performance are optimized, fostering a cybersecurity culture that can rapidly adapt to new challenges.
How mature is your cybersecurity culture?
After a cybersecurity culture is established, security leaders should monitor its maturity on an ongoing basis. Beyond tracking general cybersecurity metrics, such as the number of data breaches or mean time to detect and then resolve security incidents, measuring the culture's reach and effectiveness also requires looking at metrics related to employee preparation and security performance.
On the preparation side, one key metric to watch is the timely completion of new and updated cybersecurity training modules. Another is participation in awareness-raising activities, such as lunch-and-learn sessions.
On the performance side, key metrics include the following examples:
- Click-through rates on fake phishing emails sent out to test employees, which should decrease as the culture improves.
- Reporting of both real and fake phishing attempts, which should increase.
- Data-leak events detected by data loss prevention (DLP) tools, which should decrease.
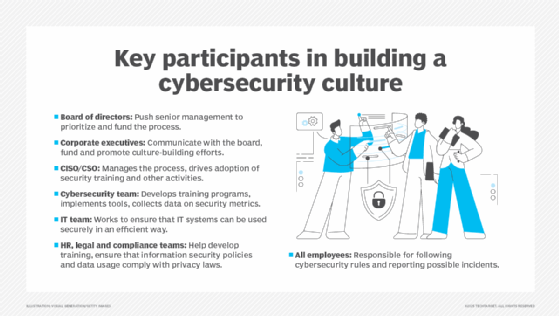
Who plays a role in a company's cybersecurity culture?
Everyone in a company has a role to play in fostering its cybersecurity culture. Here's a rundown of the key roles and responsibilities.
- Board members. Culture starts at the very top, with the company's board of directors and its influence on high-level corporate priorities as well as the allocation of resources to pursue them. By compelling C-level executives to prioritize and fund the process of building a cybersecurity culture, board members can ensure that the whole organization sees how important cybersecurity is. They can also model good behavior themselves -- for example, by taking part in security training.
- Corporate executives. C-suite executives have responsibilities to the board, each other and the rest of the organization. They should continually communicate with the board about the potential business impact of security incidents and the ROI of cybersecurity initiatives. Corporate execs need to join their peers in promoting the cybersecurity culture and sharing the resource burden of culture-building efforts. They must give their direct reports time and funding for training, encourage the use of secure methods and proper protocols by business teams, and enforce consequences when users fail to do so. They should also support efforts to improve security protocols and tools to better meet operational needs.
- CISO or CSO. These positions have special responsibilities among C-level execs, since cybersecurity is their focus. They need to drive the adoption of training programs and other activities that go into developing a broad-based cybersecurity culture, while overseeing management of that process. In addition, CISOs and CSOs must incorporate the importance of fostering the culture into their own process building, policy definition, team development and security tool or service selection procedures.
- Cybersecurity team. These staff members help shape the security training curriculum based on their knowledge of the enterprise's IT environment and cybersecurity measures. They should also work behind the scenes to make it as easy as possible for everyone else to do things the right way from a cybersecurity perspective. For example, that might mean implementing passwordless authentication or making sure DLP monitoring is well tuned to how business users share information internally and externally to avoid erroneous alerts and interceptions. The security team is usually responsible for collecting metrics data, too.
- IT team. Like the cybersecurity team, IT's main job in fostering a strong cybersecurity culture -- aside from "walking the walk" and following good cybersecurity practices themselves -- is making it as easy as possible for everyone else to do what they need to do to work securely while using the organization's networks, systems and applications.
- HR, legal and compliance teams. As part of its core responsibilities, the HR team is instrumental in building and maintaining a cybersecurity training and assessment program for employees. Along with the legal and compliance teams, HR must ensure that training content, frequency and methods meet corporate needs as well as legal and regulatory requirements. The legal and compliance teams also share responsibility for making sure that information security policies and data usage comply with applicable data protection and privacy laws.
- All employees. Every employee has a role to play in cybersecurity by being alert, aware and cautious as well as following proper processes in handling information and using systems. They're also responsible for providing honest feedback on security processes that put correct behavior at odds with getting things done in a timely fashion. Such feedback helps IT and security teams find a way -- by redesigning an interface or replacing a tool, for example -- to keep cybersecurity a business enabler rather than a roadblock.
Editor's note: This article was updated in July 2025 to add new information.
Jerald Murphy is senior vice president of research and consulting with Nemertes Research. With more than three decades of technology experience, Murphy has worked on a range of technology topics, including neural networking research, integrated circuit design, computer programming and global data center design. He was also the CEO of a managed services company.
John Burke is CTO and a research analyst at Nemertes Research. Burke joined Nemertes in 2005 with nearly two decades of technology experience. He has worked at all levels of IT, including end-user support specialist, programmer, system administrator, database specialist, network administrator, network architect and systems architect.







