10 key cybersecurity metrics and KPIs your board wants tracked
Security leaders need cybersecurity metrics to track their programs and inform decision-makers. These 10 metrics and KPIs provide a good foundation for tracking essential activity.
Metrics are the lifeblood of any organization. Without metrics or KPIs, enterprise managers can be blind to critical variables that determine success and help them hit financial and production targets.
For cybersecurity practitioners, metrics are critical to monitoring and managing digital risks and demonstrating to executives, board members and other stakeholders how well the organization defends itself from threats. They are essential snapshots of an organization's overall security health.
Why it's important to track cybersecurity metrics for your business
Cybersecurity metrics and KPIs are necessary for measuring the strength of an organization's security program and revealing patterns that either reinforce existing practices or point to areas that need improvement.
"Without metrics, you don't know if you're doing the right things or improving or sharpening your tools," said David Lindner, CISO of Contrast Security, which makes application security software. "If I see trends of certain metrics going the wrong direction, I will reinvest resources to try to resolve those things, fix them and make them go the other direction."
Metrics can also help an organization improve its security program over time. "Metrics are becoming more and more foundational guidelines that you look at daily, weekly and monthly to track how you're doing, show your improvement and get buy-in for your security program," said Steve Cobb, CISO of SecurityScorecard, a maker of supply chain detection and response software.
Security metrics can also help explain the value of an organization's cybersecurity program to decision-makers and stakeholders, including the C-suite and board. "There is value in using those metrics to show ROI or value to leadership so that you can continue to invest in your cybersecurity programs and develop your resources internally to take your cybersecurity practice to a better state," Cobb said.
Finally, metrics can help organizations build threat actor profiles for cyberdefenders, enabling them to develop the most effective strategies for countering threats.
10 cybersecurity metrics and KPIs to track
Security professionals can choose from an endless array of metrics and KPIs, which is why Bob Maley, CSO of Black Kite, which makes a cyber-risk intelligence platform, recommends starting with objectives and key results or comparable goal frameworks in their cybersecurity planning and then working backward to identify the metrics to track to achieve those objectives.
"It's important to measure things that directly affect the company's overall objectives, rather than collecting metrics for the sake of it," he said.
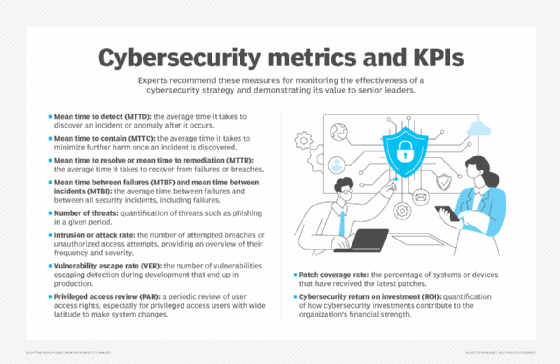
Experts generally point to 10 foundational cybersecurity metrics that security leaders find the most useful for achieving their security goals. These metrics are the following:
- Mean time to detect. MTTD measures the average time it takes to discover an incident or anomaly after it occurs. "Mean time to detect or mean time to acknowledge is how quickly you detect incidents," Lindner said. "Is it taking you an hour, [or] is it taking you two days a month?"
- Mean time to contain. MTTC measures the time it takes to minimize further harm once an incident is discovered. "Mean time to contain is kind of grouped in with mean time to resolve, but they're two different things," Lindner said. "Containment to me doesn't necessarily mean resolution. It's just that I've contained whatever we've found. I've limited the blast radius and the potential future damage by containing it, and now, I need to resolve it."
- Mean time to resolve or mean time to remediation (MTTR). These two metrics are subtly different but often used interchangeably, given that they both measure the average time it takes to recover from failures or breaches. "One of the things that we really track internally is mean time to remediation, or how quickly we fix things when found," Lindner said. "If I see that creeping up -- maybe one month it was like seven days on average for a critical vulnerability, and the next quarter, it's up to 14, and the next quarter it's up to 30 -- that's a trend that I don't like to see."
- Mean time between failures (MTBF) and mean time between incidents (MTBI). Both metrics measure the average time between incidents, but there are differences. MTBF focuses only on the time between failures, while MTBI measures the time between all security incidents, including failures. "Basically, I want to extend the time between an incident and the next incident. The further I can make those two apart, the better the program is," Lindner said.
- Number of threats. This metric quantifies the threats, such as phishing, network or cloud security threats, for a given period. It helps organizations understand the scale of risks they face. "This metric is more informational than operational, but it provides overarching guidance to you and your cybersecurity program," Cobb said.
- Intrusion or attack rate. The intrusion or attack rate measures the number of attempted breaches or unauthorized access attempts made against an organization's assets, providing an overview of the frequency or severity of attacks security teams need to know. "It tells you a lot about the footprint and who's possibly coming after you," Lindner said.
- Vulnerability escape rate. VER, a key indicator of software security, measures how many vulnerabilities escape detection during development and make it into the production environment. "Every business is a software organization," Lindner said, and VER measures how many vulnerabilities are getting through the development process, including the application security program and testing.
- Privileged access review. PAR is a periodic review of user access rights, especially for privileged access users who have wide latitude to make system changes. PAR is essential when investigating unauthorized access, a method that threat actors increasingly use to penetrate networks. Lindner called frequently reviewing privileged accounts "pretty important in today's world."
- Patch coverage rate. This KPI measures the percentage of systems or devices that have received the latest patches. "It's getting harder and harder to track," Lindner said. "There are 150 CVEs or vulnerabilities that might need patching released every day. At one point, we used 700 different SaaS vendors. I can't track patching on any of those. So, there's this big black hole."
- Cybersecurity ROI. Cybersecurity ROI measures the success of a cybersecurity program by quantifying how much cybersecurity investments have contributed to an organization's financial strength. Cobb said security professionals should show this figure to board members and others to demonstrate how cybersecurity is not just a cost of doing business, but also helps provide better service to customers and boost the organization's reputation and brand.
How to manage the process of tracking cybersecurity metrics
Although tracking metrics and putting them to good use can sometimes seem daunting, experts offer a few tips to make the process easier. "Security leaders should consider what story they want to tell, what data is available and whether the metrics are easily measurable," said Black Kite's Maley.
SecurityScorecard's Cobb underscored the importance of using metrics to tell a story. "If you look back over security events that happen many times, you can see breadcrumbs that were left far in advance of the actual event taking place, like an increased number of phishing attacks or other things that you may track from a metric perspective in your cybersecurity program," Cobb said. "Those can tell a story and give you an understanding of what's to come."
Finally, measuring and reporting security metrics can be challenging but can also be made easier by "correlating different metrics, such as click-through rates and phishing attacks, to get a comprehensive picture of the security situation," Maley said.
How to present cybersecurity metrics to the board and other stakeholders
Even as metrics offer essential guidance for cybersecurity leaders in developing their own plans, they can also be valuable tools for keeping management and board-level decision-makers plugged in to the organization's cybersecurity program.
However, experts say it is not always easy to translate these key measures in ways that executives who are not steeped in cybersecurity can understand. "It's not easy to talk to boards at all, especially in the language most cybersecurity practitioners and leaders use," Cobb said.
"There's a language barrier between the practitioners and what the board sees in ROI and how they translate that," he added. "One of the biggest challenges I see for CISOs and security practitioners today is mastering that translation."
"Most boards that don't have insight into the day to day of a security organization are probably going to be more interested in the badness, the nuance of what's changed and why, and what are we doing about it," Lindner said. As soon as something bad happens, "that's when they get a little bit more invested," he added. "Frankly, it makes my job easier to explain why we need something."
Above all else, security professionals should steer board-level conversations to the bottom line. "When communicating with the C-suite or board, focus on how security metrics connect to the company's bottom line and operational value," Maley said. "Present a narrative that demonstrates trends in security threats and their potential impact on the business, rather than just providing technical metrics."
Cynthia Brumfield is a writer, analyst, publisher and instructor specializing in cybersecurity. She is the author of the Wiley book, Cybersecurity Risk Management: Mastering the Fundamentals Using the NIST Cybersecurity Framework.








