Why effective cybersecurity is important for businesses
Cyberattacks can have serious financial and business consequences for companies, which makes implementing strong cybersecurity protections a critical step.
The threat of a successful cyberattack ranks among the more significant business risks organizations of all sizes and across all industries face. Business and IT executives have good reason to rate cyberthreats as a high-level risk -- and to invest in a strong cybersecurity program for their company.
The volume and sophistication of cyberattacks have grown significantly since the first computer viruses emerged in the 1970s and the Morris worm became the first major internet-based attack in 1988. Moreover, the number of devices connected to the internet and corporate networks exploded during the past few decades. The reliance on IT systems for everyday business tasks also spiked in recent years, driven partly by digital transformation initiatives in companies.
Consequently, a single successful attack can have a catastrophic effect, with the potential to expose personal information, bring a company's operations to a halt, cripple critical infrastructure and even physically harm people.
Recognizing the importance of cybersecurity, enterprise leaders in many organizations have increasingly prioritized it, seeking to implement more rigorous policies, procedures and technologies to defend against cyberthreats of all kinds -- data breaches, ransomware attacks, phishing and more.
For instance, the "2025 Focus on the Future" report from risk management platform provider AuditBoard identified cybersecurity and data security as the No. 1 risk category among surveyed risk management and internal audit executives for the fourth year in a row. More than 80% of the 376 respondents also put it in the top spot for expected audit efforts in 2025. Similarly, the "2025 Global Digital Trust Insights" survey of 4,042 IT and business executives by professional services firm PwC found that mitigating cyber risk was "top-of-mind" among two-thirds of IT leaders and nearly half of business leaders in 2024.
Such viewpoints are pushing up cybersecurity budgets. Seventy-seven percent of PwC's survey respondents expect their cyber budget to increase during 2025, with data protection and data trust the top priority for 48% of business leaders and cloud security tops for 34% of IT leaders. Gartner projected that spending on information security by user organizations worldwide will total $212 billion in 2025, a 15.1% increase over the $183.9 billion it estimated for 2024.
Why strong cybersecurity is critical to business success
The following factors show why effective cybersecurity is a necessary part of doing business:
- Nearly every organization requires IT systems to function, which has significantly increased the consequences of a successful cyberattack. "We have become so dependent on technology that the majority of businesses cannot operate without it," said Carl Eyler, director of the National Cybersecurity Institute at Excelsior University and head of information security and technology risk at Mbanq, a loan origination platform provider.
- Data is now one of the more valuable assets -- often the single most valuable one -- in most companies. Any security issues that hurt an organization's data quality or access could affect business operations.
- Cybercrime continues to grow in nearly every way. The number of bad actors is increasing, as are the sophistication of their attacks and the available tools and technologies to help launch those attacks. As an example, the growing availability of ransomware as a service and other as-a-service malware has made it easier for attackers to strike, said Sarb Sembhi, CTO and CISO at information services company Virtually Informed. Google Cloud's "Cybersecurity Forecast 2025" report cited that attackers will increasingly use AI for phishing, vishing and social engineering attacks and take advantage of new developments in ransomware and malware platforms that make it easier to launch attacks.
- Government regulations and industry requirements mandate cybersecurity standards for many businesses, giving them no choice in making cybersecurity a priority. The U.S., individual states, the EU and other governments all have laws requiring organizations to safeguard sensitive data and implement prescribed cybersecurity practices. The U.S. Securities and Exchange Commission in July 2023, for example, adopted rules requiring all companies that file registration statements for stock offerings to disclose "material cybersecurity incidents" and to annually submit information on their cybersecurity strategy, governance and risk management initiatives. A case in point on industry mandates is PCI DSS, which sets standard security policies and procedures for any entity that accepts payment cards.
- Many consumers and business partners now have higher expectations that companies will make the necessary cybersecurity investments to thwart cybercriminals from stealing customer information and doing anything else that could harm customers and partners by extension. Meeting those demands presents business opportunities. "Creating and building trust with customers can be translated into revenue gains," said Erik Avakian, a cybersecurity executive counselor at Info-Tech Research Group and former CISO for the Commonwealth of Pennsylvania.
Cybercrime's business costs and consequences
The cost of cybercrime is staggering -- despite some research showing a reduction in the cost per breach. Here are some overall figures.
- The average cost of a data breach among 604 organizations worldwide was $4.9 million, according to the IBM "Cost of a Data Breach Report 2024" from IBM and research firm Ponemon Institute that examined breaches between March 2023 and March 2024. That was an all-time high for the annual report and amounted to a 10% increase from the year before. The largest percentage of data breaches involved data stored across multiple environments, with the highest breach cost ($5.17 million) attributed to data stored in public clouds.
- PwC's "2025 Global Digital Trust Insights" survey found the average cost of a cyberattack to be $3.3 million compared to $4.4 million the previous year. Cloud-related threats (42%), hack-and-leak operations (38%) and third-party data breaches (35%) ranked as the highest cyberthreats.
- The average ransom payment in response to a successful ransomware attack has dropped 50% over the past year, yet still reached $1 million, according to cybersecurity software provider Sophos' "The State of Ransomware 2025" survey of 3,400 IT and cybersecurity professionals. Likewise, the average cost to recover from a ransomware attack dropped by 44% to $1.53 million vs. $2.73 million the previous year, covering things such as downtime, people time, device costs and lost business opportunities.
- Still, the annual cost of cybercrime worldwide is expected to surpass $10 trillion in 2025 and surge to $16 trillion in 2029, due in large part to phishing, ransomware, credential theft and fraud, according to market data and research firm Statista.
The list of cybersecurity incidents goes on and on. An organization that finds its cybersecurity defenses have been penetrated typically faces a long list of expenses as it seeks to repel the attack, restore affected systems and recover from the incident.
In July 2024, CrowdStrike released a flawed update to its endpoint detection and response software that affected millions of Microsoft Windows devices and caused outages at airlines, banks, broadcasters, healthcare providers, retail payment terminals and cash machines globally. Considered the largest IT outage in history, the cost to U.S. Fortune 500 companies has been estimated at $5.4 billion.
A September 2023 ransomware attack on MGM Resorts International that used social engineering techniques to gain access to privileged user accounts cost the hospitality company an estimated $100 million and disrupted customer room access, casino games and other services. MGM said it expected its cybersecurity insurance policy to cover all the costs, but it also disclosed that the attackers stole personal information on some customers, including driver's license, Social Security and passport numbers.
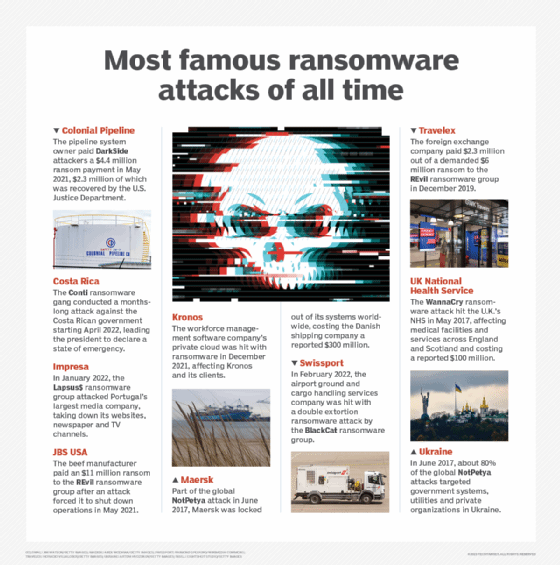
In another well-known example, a 2021 ransomware attack on Colonial Pipeline led to gas supply shortages in multiple U.S. states and cost the pipeline operator $4.4 million in ransom payments, some of which was later recovered by the U.S. Department of Justice. And Denmark-based shipping giant A.P. Moller-Maersk suffered upward of $300 million in losses after a 2017 malware attack shut down the systems used to operate its shipping terminals around the world.
In addition to the required staff time, Eyler said organizations can expect to pay for outside technical support, inside and outside legal counsel, data breach notification costs and regulatory fines. They'll also suffer costs due to lost sales and business opportunities. "You don't know how far-reaching the costs are going to be when you've been breached," Eyler noted.
A company's reputation with customers likely will also take a hit, which can translate into additional lost business in the future. Sembhi said the costs and consequences of an attack could even tank organizations -- especially those without enough resources and reserves to weather the event's aftermath. "With small businesses, one attack can take them out," he said.
Business benefits of effective cybersecurity
The ramifications of cyberattacks have pushed many enterprise leaders -- directors, CEOs, CFOs and other senior business executives, as well as CIOs and CISOs -- to focus on improving their organization's security posture.
The" Global Future of Cyber Survey, 4th Edition," released in 2024 by professional services firm Deloitte, found that 86% of nearly 1,200 cybersecurity decision-makers will implement specific activities or actions to increase cybersecurity, while 57% of respondents anticipate increasing their cybersecurity budget over the next 12 to 24 months. The top three business outcomes organizations expect to achieve with their cybersecurity initiatives are protecting intellectual property, improving threat detection and response, and increasing efficiency and agility.
Such findings reflect a shift in thinking among executives who now see a cybersecurity program as an enabler of business operations, not merely a backstop for preventing losses. "That's the perspective companies have to have when it comes to cybersecurity," said Fred Rica, a partner in the advisory practice at professional services firm BPM. "It allows them to do things they couldn't do before, and it allows them to be more efficient, save money and be more productive."
Key elements of a cybersecurity strategy
There's no universal basis for what makes a strong cybersecurity program -- each organization must determine its required level of security. To do so, Rica said companies should primarily think about whether their security efforts are appropriate from a business perspective.
That involves concepts such as risk appetite and risk tolerance and how much residual risk business executives are willing to accept. "If they're comfortable that they've identified their risks, that those risks are managed and that the risks they've left on the table fit their risk profile, then they have a good program," Rica said.
Organizations must also identify critical systems and assets and understand the cyberthreats they're most likely to face, so they can invest in the right people, processes and technology to mitigate security risks to an acceptable level, Avakian said. He added that developing a cybersecurity strategy is an ongoing exercise because "things change all the time."
Other key elements of creating a successful cybersecurity strategy include the following:
- Alignment with business goals to ensure long-term continuity.
- Visibility into where data resides within the organization. "Understand where it is, who has access to it, what access controls are in place and the entry points to the data," Eyler said.
- An understanding of the security and data privacy laws with which the organization must comply.
- A detailed cybersecurity risk assessment that evaluates the organization's existing ability to protect itself from cyberthreats and identifies where its defenses fall short. "Measure where you have gaps and then decide what initiatives to put in place to close those gaps," Avakian said.
- A defined set of cybersecurity metrics for measuring how well the security program performs and how it improves over time.
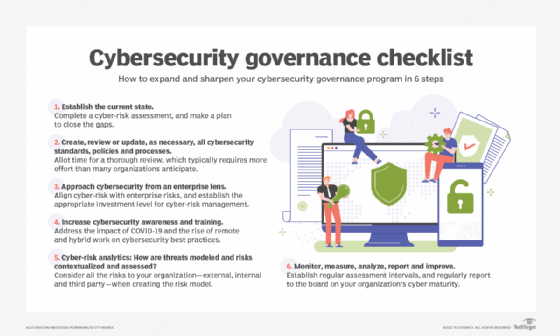
- A cybersecurity governance structure to ensure that employees adhere to established security policies and procedures.
- Support and involvement from senior executives to help ensure that there's adequate funding and high-level advocacy for the cybersecurity program.
- A detailed incident response plan that's regularly tested and practiced by both the security team and business units.
Tips on implementing and managing a cybersecurity program
Use the following best practices to create an effective cybersecurity program:
- Build a security-minded culture. Developing an internal culture that emphasizes cybersecurity is a must. "All stakeholders should know and understand what their responsibilities are from a cybersecurity perspective because security should be everybody's job," Eyler said.
- Implement a comprehensive cybersecurity awareness and training program. To help foster a cybersecurity culture, all employees and relevant stakeholders should be trained on the importance of cybersecurity and the policies and procedures adopted by the organization.
- Create cybersecurity champions. These are people throughout the organization who can evangelize the importance of following security policies and procedures. "Championing security starts with the CISO, but the CISO can't do it all," Avakian explained.
- Focus on improving cybersecurity performance over time. "Every day should be about continuous improvement," Avakian said.
Editor's note: This article was originally published in January 2024 and updated in July 2025 to reflect the latest developments in cybersecurity.
Mary K. Pratt is an award-winning freelance journalist with a focus on covering enterprise IT and cybersecurity management.






