Cybersecurity governance: A guide for businesses to follow
Cybersecurity governance is now critical, with NIST CSF 2.0 recently adding it as a dedicated function. Learn why governance is core to an effective cyber strategy.
Cybersecurity governance is becoming vitally important for organizations today, with senior leadership, customers, business partners, regulators and others expecting sound cybersecurity governance programs to be built into an organization's cybersecurity strategy.
The demand for stronger guidance on cybersecurity governance led to a significant addition to the NIST Cybersecurity Framework version 2.0, published in 2024. The update added an entire function dedicated to governance, which NIST defines as responsible for ensuring that an "organization's cybersecurity risk management strategy, expectations, and policy are established, communicated, and monitored."
Under the revised framework, cybersecurity governance serves as the foundation for a business's cybersecurity risk management programs and practices, including asset identification, risk assessment, asset protection, continuous monitoring, and incident detection, response and recovery capabilities. Without governance, risk management programs and security controls are far more likely to have significant deficiencies, ultimately leading to more incidents and bigger negative impacts from incidents.
This article provides information and actionable recommendations for implementing a cybersecurity governance framework within your business, based on the components of the NIST CSF 2.0 Govern function.
The strategic role of leadership in cybersecurity governance
While leadership has vital roles in all areas of cybersecurity governance, the most important strategic roles involve three parts of the CSF 2.0 Govern function:
- Organizational context. Leadership must understand the business's mission and objectives, key stakeholders, and high-level privacy and cybersecurity requirements, and they must ensure that the context these provide is effectively communicated and addressed within the business. Leadership must also understand the business's critical dependencies -- that is, what the organization relies on, such as its external suppliers and vendors, technology systems and key personnel -- as well as the dependencies on the business, such as customers, supply chain partners, regulatory bodies and employees.
- Risk management strategy. Leadership must establish the business's risk management objectives, risk appetite and risk tolerance as the basis for its cybersecurity risk management program. Leadership is also responsible for ensuring that key elements of the cybersecurity strategy are implemented. This entails consistently communicating risks within the business and with third parties, as well as looking for positive risks (i.e., opportunities) that might benefit the business.
- Policy. The business's cybersecurity policy should be the heart of the cybersecurity risk management program. Leadership must review and approve the policy. Cybersecurity is likely to be taken more seriously if leadership endorses the policy and communicates its importance to the workforce.
Core aspects of cybersecurity governance
In addition to the strategic governance areas already discussed, leadership needs to play an active role in all other areas. The rest of the CSF 2.0 Govern function defines the following three areas:
- Roles, responsibilities and authorities. Leadership must accept responsibility for the business's cybersecurity risk management and lead the risk management culture by example. All necessary roles and responsibilities for cybersecurity risk management must be implemented. The business must allocate the necessary resources for performing cybersecurity risk management, including regularly training all staff on their cybersecurity responsibilities. Finally, human resources activities must include cybersecurity considerations, where applicable.
- Oversight. The business's cybersecurity risk management strategy must be regularly reviewed and improved over time. It must also be adjusted to account for new cybersecurity requirements and other evolving factors affecting risk, such as the rise of AI. Oversight also includes measuring and evaluating the business's cybersecurity risk management performance against established metrics.
- Cybersecurity supply chain risk management. The same types of cybersecurity risk management practices that the business uses internally need to be extended to apply to technology product and service providers as well as their products and services. These practices include defining cybersecurity responsibilities for suppliers, specifying cybersecurity requirements in contracts with suppliers, assessing the risks of suppliers and their products and services, and including suppliers in incident response plans and exercises.
Benefits of cybersecurity governance
Cybersecurity governance can provide many benefits to businesses, including the following:
- It can help businesses identify shortcomings in their current cybersecurity practices, plan how to address those shortcomings, execute that plan to improve the business's cybersecurity risk management, and monitor as well as measure progress.
- It helps ensure that a business manages its cybersecurity risks as effectively as it manages all the other types of risks it faces. Many businesses are well versed in managing financial risk, physical risk and other risks besides cybersecurity. Bringing cybersecurity risk up to the same level as other risks and integrating it with the business's enterprise risk management (ERM) practices help ensure consistent, effective management of all the business's risks.
- It enables businesses to identify, understand and comply with all cybersecurity requirements, including laws, regulations and contractual clauses they are subject to. Cybersecurity governance also fosters the monitoring and improvement of cybersecurity risk management over time in response to new requirements that must be complied with to avoid fines, reputational damage and even the possibility of imprisonment for senior leadership.
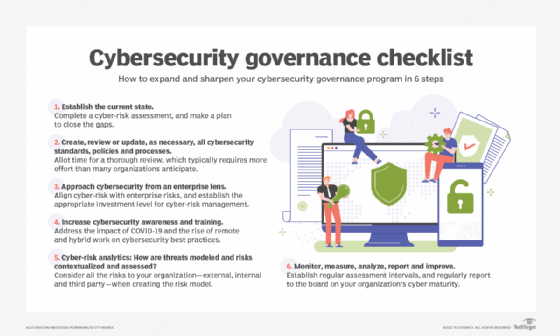
How to build a cybersecurity governance program
The CSF 2.0 Resource Center is an excellent starting point for any business interested in building a cybersecurity governance program. Its materials are all freely available, including the CSF 2.0 publication, accompanying quick-start guides and informative references, which provide mappings to numerous cybersecurity standards and guidelines. Follow the steps outlined in the CSF 2.0 publication to start assessing your business's current cybersecurity posture and planning the high-level actions needed to strengthen that posture.
The Resource Center also provides a list of CSF implementation examples for each element of the CSF 2.0. For example, actions supporting cybersecurity governance include updating both short-term and long-term cybersecurity risk management objectives annually and including cybersecurity risk managers in ERM planning.
Challenges of implementing cybersecurity governance
Implementing cybersecurity governance means making significant changes to how the business manages its cybersecurity risk. Change at this scale, including defining or redefining the business's cybersecurity risk management strategy and policies, revamping cybersecurity-related roles and responsibilities, and extending cybersecurity risk management to technology suppliers, requires significant resources and labor. Most importantly, it relies on strong buy-in and support from the business's senior leadership, along with open and transparent communication throughout the business.
Implementing governance will take patience. It can't all be done at once. The business's mission and requirements need to be understood before its cybersecurity risk management strategy and policies can be established, for example. And governance components like supply chain risk management will take even longer because they'll require coordination with many suppliers and, potentially, updates to many contracts and other agreements.
Conclusion
There are many excellent cybersecurity governance resources freely available. An advantage of using the NIST CSF 2.0 as a starting point is that it doesn't dictate exactly how you implement governance. This enables businesses to plan governance activities while using whatever existing cybersecurity risk management frameworks or standards are already in place. Think of the CSF 2.0 as providing a common language for speaking about governance with others. It helps open lines of communication both inside your business and outside.
Karen Scarfone is a general cybersecurity expert who helps organizations communicate their technical information through written content. She co-authored the Cybersecurity Framework (CSF) 2.0 and was formerly a senior computer scientist for NIST.







