15 of the biggest ransomware attacks in history
From attacks on private organizations and manufacturers to healthcare organizations and even entire countries, ransomware has done extensive damage in recent years.
Ransomware has become a favorite attack strategy for bad actors, with reports labeling it the most effective way for cybercriminals to monetize illegal access into networks. News of ransomware attacks appears daily.
More troubling still are predictions that ransomware gangs are becoming more adept at using AI, and well-funded ones could soon use agentic AI to launch even more sophisticated attacks at scale.
Such advances show how far the world has come from the first ransomware attack back in 1989, when thousands of the World Health Organization's AIDS Conference attendees returned home to find floppy disks in their mailboxes that allegedly held a questionnaire about the likelihood of contracting HIV. But they didn't find any questions: The disks contained a program designed to encrypt the names of their computer files. If they wanted their files restored, they were told to send $189 to a Panamanian post office box.
Fast-forward a few years to see the evolution of ransomware, enabled by the rise of the internet, society's shift to an interconnected digital world and the introduction of cryptocurrency. Malicious actors organized. Ransomware as a service (RaaS) emerged. Double and triple extortion attacks became common.
Consequently, the number of victims, the amount of money demanded and the impact of successful attacks have soared over the years.
Data on the number of ransomware attacks, estimated ransom payments and the total costs incurred by victims varies from one report to the next. Because victims are sometimes reluctant to publicly share that they've been hit by ransomware, whether they paid a ransom or how much they spent to recover from such an incident, an accurate estimate of the damage is difficult to determine.
Studies, however, do point to some troubling numbers. For example, NCC Group counted 5,263 ransomware cases in 2024, noting in its "2024 Cyber Threat Monitor Report" that the tally is the highest volume in annual cases since the cybersecurity software and services company started monitoring ransomware activity in 2021. In "The State of Ransomware 2024," security vendor Sophos estimated that 59% of organizations were hit by some type of ransomware incident in the prior year.
Quantifying the biggest attacks can be difficult, but some stand out. The following is a list of 15 of the most impactful ransomware attacks to date, ordered alphabetically.
1. Ascension
Type of ransomware: Black Basta ransomware
Attacker: Reportedly Black Basta
Date: May 8, 2024
Losses: $1.3 billion
Ascension, a St. Louis-based Catholic health system, said it had been hit by ransomware that disrupted its access to electronic health records, telecommunications systems and some critical operational systems, including ones used for patient care. Ascension was forced to divert ambulances and close pharmacies, while its clinicians reported that the incident affected their ability to care for patients. Furthermore, the attack exposed the personal information of 5.6 million individuals and cost the nonprofit system a reported $1.3 billion. It is unclear whether Ascension paid a ransom as part of its remediation and recovery efforts.
2. Caesars and MGM casinos
Type of ransomware: Assault on NCR Aloha POS platform
Attacker: ALPHV/BlackCat
Date: September 2023
Losses: Upward of $100 million
Caesars and MGM, two of the biggest and most recognizable U.S. hotel and casino chains, fell victim to ransomware attacks launched by the ALPHV/BlackCat group. The attacks on Caesars and MGM stemmed from a larger assault on the NCR Aloha point-of-sale platform, which was widely used in the hospitality industry. Both Caesars and MGM lost access to their entire IT infrastructure, including slot machines. According to cybersecurity company Kaspersky, Caesars paid a $15 million ransom, which was half the demanded amount, while MGM did not pay a ransom, opting to restore its systems at a cost of $10 million and suffering a loss of $100 million during the nine-day recovery time.
3. CDK Global
Type of ransomware: Not reported
Attacker: BlackSuit
Date: June 8, 2024
Losses: $1 billion-plus collectively in addition to a reported ransom payment of $25 million worth of bitcoin
The attack on CDK Global led to widespread system outages at 15,000 U.S. and Canadian auto dealerships, halting their ability to track inventory, schedule services and process sales. The initial attack, believed to come from the BlackSuit ransomware gang, was followed by a second attack while CDK Global was working to recover its systems. The attack cost auto dealerships more than $1 billion collectively, according to an estimate from consulting firm Anderson Economic Group.
4. Change Healthcare/UnitedHealth Group
Type of ransomware: Exploitation of a Citrix portal account
Attacker: ALPHV/BlackCat
Date: Feb. 21, 2024
Losses: More than $800 million in direct damages, including a $22 million ransom, and estimated overall costs of approximately $2.5 billion
ALPHV/BlackCat launched a successful ransomware attack on Change Healthcare, a division of UnitedHealth Group. The attackers, who gained access by exploiting a Citrix portal account that lacked multifactor authentication, spent nine days stealing data as they moved undetected within the company's systems. They then hit the company with a ransomware attack that disrupted more than 100 applications, resulting in the inability for healthcare entities nationwide to process electronic payments and medical claims. The incident is the largest healthcare breach in the U.S. to date, affecting more than 100 million people. It cost the company more than $800 million in direct costs, including a $22 million ransom payment made in cryptocurrency. Total costs from the attack were an estimated $2.5 billion to $3 billion.
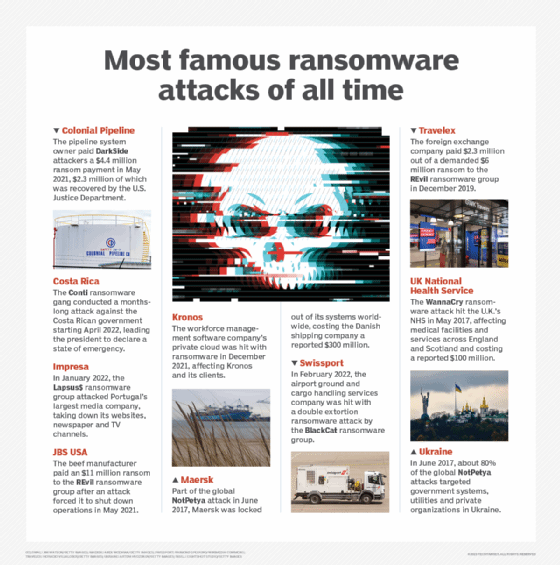
5. Colonial Pipeline
Type of ransomware: DarkSide RaaS
Attacker: DarkSide
Date: May 7, 2021
Losses: $4.4 million (approximately $2.3 million was recovered)
The attack on Colonial Pipeline became one of the most notorious ransomware attacks because of its impact on everyday Americans, with those living in Southeast states suddenly facing gas supply shortages.
Colonial Pipeline, owner of a pipeline system carrying fuel from Texas to the Southeast, suffered a ransomware attack on the computer systems that managed the pipeline. DarkSide attackers accessed the systems through a compromised credential for a legacy VPN. Working with the FBI, the company paid a $4.4 million ransom within hours of the attack. The impact lasted for days, however, as the company struggled to fully restore operations.
Federal and state officials, including then-President Joe Biden, issued emergency declarations in the days after the attack to ensure fuel could reach the affected region and limit damages. The attack also led Biden to issue an executive order to improve the country's cybersecurity.
The U.S. Department of Justice later announced it had seized $2.3 million of the $4.4 million in bitcoin used to pay the ransom.
6. Costa Rica
Type of ransomware: Conti
Attacker: Conti gang
Date: April 17, 2022
Losses: $30 million a day
The Conti ransomware gang launched a monthslong attack against Costa Rican government institutions. The initial attack on the Ministry of Finance used compromised credentials to install malware. The Costa Rican Ministry of Science, Innovation, Technology and Telecommunications and the Ministry of Labor and Social Security were later attacked. The government shut down multiple systems, resulting in delayed government payments, slowed and halted trade, and limited services.
Within the first week of the attack, then-President Carlos Alvarado refused to pay the purported $10 million ransom. The Conti ransomware gang then leaked almost all the 672 GB of data it stole during the attacks. It took months before systems were restored -- but not before the country's newly elected president, Rodrigo Chaves Robles, declared a state of emergency.
7. Impresa
Type of ransomware: Lapsus$
Attacker: Lapsus$
Date: Jan. 1, 2022
Losses: Not reported
Ransomware group Lapsus$ launched one of the world's most conspicuous ransomware attacks when it struck Impresa, Portugal's largest media conglomerate. The attack took down all its websites, its weekly newspaper and its TV channels. Attackers also gained control of the company's Twitter account and claimed it had access to the company's AWS account. According to news reports, Impresa confirmed the attack but said no ransom demand was made.
Lapsus$, which had attacked Brazil's Ministry of Health in 2021, posted a ransom message that threatened to release company data. Portuguese authorities labeled the Impresa attack the largest cyberattack in the country's history.
8. JBS USA
Type of ransomware: REvil RaaS
Attacker: REvil
Date: May 30, 2021
Losses: $11 million ransom payment
Beef manufacturer JBS USA Holdings Inc. paid an $11 million ransom in bitcoin to malicious actors after an attack forced it to shut down operations. IT staffers initially noticed problems with some of the company's servers, and shortly thereafter, the company received a message demanding a ransom. Pilgrim's Pride Corp., a unit of JBS, was also affected by the attack. Operations were restored within days, but not before JBS made the hefty payment.
9. Kronos
Type of ransomware: Not reported
Attacker: Not reported
Date: Dec. 11, 2021
Losses: In addition to a reported ransom payment, Kronos paid $6 million in 2023 to settle a class-action lawsuit filed by Kronos clients who alleged the company didn't do enough to protect its systems.
Ultimate Kronos Group, a workforce management software maker doing business in more than 100 countries, was hit by a ransomware attack on its private cloud. The incident affected customers around the globe, spawned yearslong ripple effects and exposed an earlier breach that magnified the impact.
The attack exposed employee data for many of the company's enterprise clients. As a result, these clients faced interruptions, delays and errors in issuing paychecks to their workers.
The Kronos attack raised questions about vendor accountability and highlighted the importance of third-party risk management, as organizations recognized that attacks on their business partners could affect them as well.
10. Maersk
Type of ransomware: NotPetya
Attacker: Russian-backed hackers suspected in the attack
Date: June 27, 2017
Losses: Approximately $300 million
Danish shipping giant A.P. Moller-Maersk suffered approximately $300 million in losses after it was hit as part of the global NotPetya attacks. The malware, which exploited the EternalBlue Windows vulnerability and spread through a backdoor in the legitimate financial software MeDoc, locked the company out of the systems it used to operate shipping terminals all over the world. As wiperware, NotPetya was designed to inflict maximum damage by not only encrypting all files on infected computers but also completely wiping or rewriting them so they could not be recovered -- even through decryption. It took Maersk two weeks to recover its computer operations.
11. Swissport
Type of ransomware: BlackCat RaaS
Attacker: BlackCat
Date: Feb. 3, 2022
Losses: Air service disruptions; no financial data reported
Swissport, a Swiss company providing airport ground- and cargo-handling services, announced that its systems had been hit by a ransomware attack in 2022. The incident delayed a small number of flights, but Swissport said it had contained the incident within 24 hours. Ransomware group BlackCat, however, soon indicated it had not only encrypted the company's files but also had stolen 1.6 TB of Swissport data it was looking to sell in a classic example of a double extortion attack.
12. Synnovis/U.K. National Health Service
Type of ransomware: Not reported
Attacker: Qilin
Date: June 3, 2024
Losses: £33 million
Synnovis, a pathology and laboratory services provider to the U.K.'s National Health Service (NHS), fell victim to a ransomware attack launched by the cybercriminal group Qilin. The attack encrypted Synnovis' IT systems, creating significant disruptions to patient healthcare -- namely, cancelled and postponed procedures, blood transfusions, tests and outpatient appointments. It also forced healthcare providers to revert to manual and paper-based systems to process information. The attack exposed the data of nearly 1 million NHS patients, with the attackers stealing and eventually leaking 400 GB worth of sensitive data when Synnovis did not pay the demanded $50 million ransom.
13. Travelex
Type of ransomware: REvil RaaS
Attacker: REvil
Date: Dec. 31, 2019
Losses: $2.3 million ransom paid; company forced into administration in 2020 in part due to the attack
At the time it was hit by the REvil ransomware gang, Travelex was the world's largest foreign exchange bureau. Attackers targeted a known vulnerability in Pulse Secure VPN servers to infiltrate the company's systems and encrypt 5 GB of data. They demanded a $6 million ransom, which was negotiated down to $2.3 million.
The attack took down the company's internal systems for nearly two weeks. The financial fallout was so severe that it ultimately forced the company into administration in 2020.
14. U.K. National Health Service
Type of ransomware: WannaCry
Attacker: Linked to North Korea
Date: May 2017
Losses: £92 million (approximately $100 million)
Companies around the world felt the impact of the WannaCry ransomware attack, the first ransomware to exploit the EternalBlue flaw in Windows systems.
The U.K.'s NHS was one of the most prominent WannaCry victims, with multiple hospitals, general practitioners and pharmacies affected in England and Scotland. NHS facilities were forced to delay and divert medical services.
15. Ukraine
Type of ransomware: NotPetya
Attacker: Russia's GRU military spy agency named as attacker, according to the CIA
Date: June 27, 2017
Losses: Estimated at $10 billion globally
While more than 60 countries were affected, the initial global NotPetya attacks in 2017 mainly targeted victims in France, Germany and Ukraine, the latter of which sustained about 80% of the attacks, according to researchers from cybersecurity software company ESET. The country's computer systems were affected, as well as networks operated by private companies and electric utilities. The aforementioned Maersk ransomware attack was also part of this series of attacks.
Mary K. Pratt is an award-winning freelance journalist with a focus on covering enterprise IT and cybersecurity management.








