
photo-dave - Fotolia
Understanding Exchange Online's Role-Based Access Control model
The Role-Based Access Control model manages and evaluates permissions in Exchange Online. Admins can explore the model, create new permissions and customize roles.
Managing permissions in an Exchange Server environment can be complex, and Exchange Online is no different.
Administrators who manage this messaging platform should understand the Role-Based Access Control model when setting up permissions for end users.
To enable the management of a Role-Based Access Control (RBAC) model in Exchange, we need to import the PowerShell cmdlets on the administrator's computer.
To do this, connect to Exchange Online and import the session with the following script:
$Session = New-PSSession -ConfigurationName Microsoft.Exchange -ConnectionUri https://outlook.office365.com/powershell-liveid/ -Credential (Get-Credential) -Authentication Basic -AllowRedirection
Import-PSSession -Session $Session
This script will request a password before connecting to Exchange; it then will bring in the necessary cmdlets.
The Exchange Online Role-Based Access Control model consists of several different components: Roles, Role Groups, Role Entries and Role Assignments. To begin exploring, run the Get-ManagementRole cmdlet to see what management roles exist in the environment.
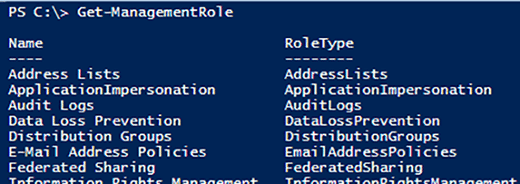
The list can get lengthy, which may lead you to believe there are a lot of roles to manage. However, there is also the default Role Groups, as shown below.
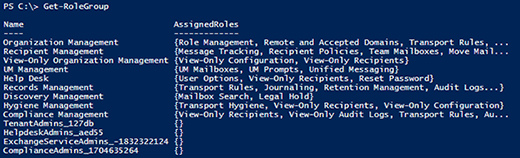
That default set of Role Groups comes with every subscription and is a way to aggregate a large, complex set of granular permissions into a more digestible set of descriptively named groups. Role Groups spare the administrator from having to look at detail-level permissions.
Adding people to roles
Assume an employee has moved to the Help Desk department. There is a Role Group called Help Desk, so the administrator needs to add that end user to the Help Desk role. You can check what role memberships the end user has. Because you don't want to see individual roles, just the role groups, run the following script:
Get-ManagementRoleAssigment -RoleAssignee "jnewhire" | Select-Object -unique RoleAssigneeName
This query returns no results; the blank output means that this user has no roles assigned to it. The following command fixes this:
Add-RoleGroupMember -Identity "Help Desk" -Member "jnewhire"
Next, run the previous command again to find the role membership, which now is called Help Desk.
Adding users to roles one at a time can be tedious. An easier way is to build a filter for the Get-User Cmdlet that finds users and adds them, as such:
Get-User -filter {StateOrProvince -eq "CA" -And Department -eq "Support"} | Foreach-Object{Add-RoleGroupMember -Identity "Help Desk" -Member $_.Identity}
The role membership allows you to run a script to see which PowerShell cmdlets and parameters users in the Help Desk role can run. Results show which Management Roles are grouped into the Help Desk Management Role Group.
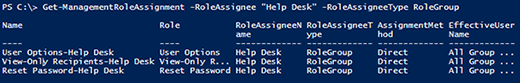
The Name column is the name of a Role Assignment Entry. To the left of the dash is the Role Name, and the part to the right is the name of the Role Group -- where role is assigned. Running the following command shows which commands each Role Assignment Entry will allow the user to access:
Get-ManagementRoleEntry -Identity "View-Only Recipients\*"
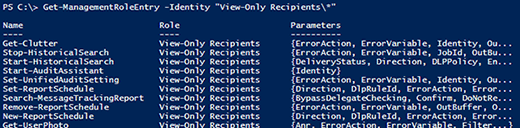
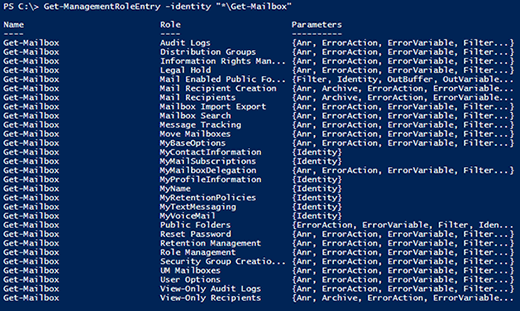
This list can be extensive. To see what roles give access to a specific command, invoke Get-ManagementRoleEntry, as shown below.
Get-ManagementRoleEntry -identity "*\Get-Mailbox"
Custom role assignment
Default Role Groups and Role Assignments within the Role-Based Access Control model work well for a lot of Exchange Online users, but they're not right for every end user. If the business needs something custom, PowerShell is the best bet.
To customize a role using PowerShell, enable customization by running the Enable-OrganizationCustomization cmdletS. To customize the role, run the cmdlet to instruct Exchange Online that you want your own copy.
For example, customization can help if you want to give Help Desk users the ability to see more of the configuration within the Exchange environment. This should help them track down issues faster before they need to escalate tickets to more privileged admins. We can add the View-Only Configuration role to the Help Desk Role Group, and let them see -- but not change -- more settings.
New-ManagementRoleAssignment -SecurityGroup "Help Desk" -Role "View-Only Configuration"
This command lets Help Desk users view the Exchange environment configuration.







