
sdecoret - stock.adobe.com
Network monitoring market converges with security analytics
As cyber attacks increase and enterprise networks require threat detection and protection, network monitoring and security analytics are converging for more comprehensive visibility.
The network monitoring market encompasses multiple segments, including network traffic analytics, network detection and response, network visibility and network performance monitoring. Although the terms often overlap among vendors, products and analyst firms, enterprises rely on these tools to monitor and secure their networks, even more so as network threats increase and evolve amid the COVID-19 pandemic.
As enterprises shifted to a remote workforce, they needed to quickly accommodate the influx of VPN and web traffic, relying on VPN capacity increases, while easing security policies. Enterprise networks extended beyond the typical corporate office, reaching into employee homes with varying levels of reliable and secure connectivity.
Cyber attacks surged as bad actors preyed on network vulnerabilities with ransomware, phishing and malware. The attacks have persisted, elevating the importance of network monitoring as a vital business objective. Network and security teams need to secure remote access, provide collaboration tools, and monitor the various connections and traffic -- all of which are driving growth in the network monitoring market.
According to Global Market Insights in its "Network Traffic Analytics Market" report, the network traffic analytics market is expected to grow at a 17% annual growth rate between 2020 and 2026, eventually reaching $4.5 billion. Similarly, Gartner forecasted the worldwide network performance monitoring and diagnostics (NPMD) market will reach almost $3 billion in 2020 and grow at an annual growth rate of 12.1% through 2023. And, according to 451 Research, the network detection and response (NDR) market is surging as enterprises implement tools to detect threats before they breach the network.
Network monitoring converges with security
With the network monitoring and security markets ripe for growth, enterprises are prioritizing network monitoring, even as it shifts to a security focus. More and more, enterprises are finding that traditional NPMD tools converge with security analytics tools -- such as network traffic analytics -- especially as vendors revamp their products to offer more comprehensive threat detection capabilities, Gartner said in its NPMD report.
"The goals of network operations are increasingly aligned with security operations, which share the objective of guaranteeing a well-performing and secure network," Gartner said. As a result of this hybrid networking approach, Gartner said 50% of network operations teams will need to rearchitect their network monitoring stack by 2024.
Many network teams might opt to make these changes by increasing throughput, lowering latency or automating certain processes with new hardware and software, said Andrew Froehlich, president of West Gate Networks and founder of research firm InfraMomentum, in the firm's recent report "Notable Advancements in Network Monitoring and Management Tools." But these changes can't offer what modern network monitoring tools can.
Traditional networking tools -- such as Simple Network Management Protocol, syslog and NetFlow -- have the ability to collect and centrally store packet capture data, but IT teams often don't have maintainable ways to analyze the large amounts of data for performance and security, the report said.
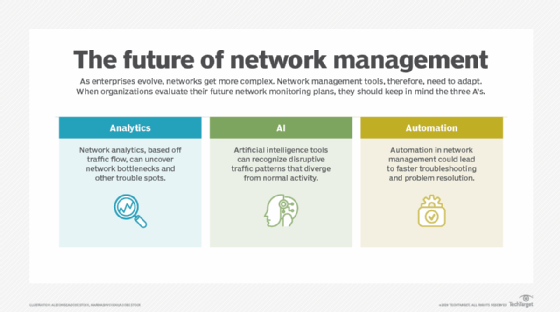
Modern network performance tools provide the same capabilities with the addition of advanced analytics that have improved with machine learning and AI, enabling them to analyze network traffic and detect threats. As a result, the lines have blurred between traditional NPMD and the more evolving NDR segment.
Network performance monitoring and diagnostics
NPMD tools glean traffic data and network health metrics from network devices and raw network packets to "identify the root causes of performance degradations," according to Gartner. These tools use AIOps functionality to predict network behavior and real-time analytics to assess network performance.
Many vendors are starting to introduce the use of AI- and machine learning-based analytics to improve anomaly detection and root cause analysis, Gartner said. The NPMD market includes segments such as application performance monitoring, IT infrastructure monitoring and AIOps.
Network detection and response
NDR tools use machine learning and other analytical techniques to detect suspicious traffic on enterprise networks, Gartner said in its NDR report. These tools constantly assess network traffic flows in real time, analyzing network behavior and alerting teams if they detect anomalies.
According to Gartner, NDR offerings must provide the following functionality:
- analyze raw network packet traffic or traffic flows in real time;
- monitor and analyze north-south traffic and east-west traffic;
- model normal network traffic and highlight suspicious traffic;
- provide machine learning or advanced analytics to detect network anomalies; and
- offer automatic or manual response capabilities to respond to vulnerabilities.
Gartner previously referred to NDR as network traffic analysis but changed its terminology to reflect the evolving functions of these tools. Likewise, 451 Research also changed its network traffic analysis terminology and now uses network visibility, detection and response (NVDR). While the former term emphasized analytics to assess network data, it didn't underscore the importance of security, according to Scott Crawford, research vice president of security at 451 Research.
"We settled on NVDR because every security operations team expressed the need to better understand their environment, better detect threats before outsiders find them first and better shut down attacks to minimize adverse business risks," Crawford said in the firm's NVDR report.







